
- •Warning and Disclaimer
- •Feedback Information
- •Trademark Acknowledgments
- •About the Author
- •About the Technical Reviewers
- •Dedication
- •Acknowledgments
- •Contents at a Glance
- •Contents
- •Icons Used in This Book
- •Command Syntax Conventions
- •Cisco’s Motivation: Certifying Partners
- •Format of the CCNA Exams
- •What’s on the CCNA Exams
- •ICND Exam Topics
- •Cross-Reference Between Exam Topics and Book Parts
- •CCNA Exam Topics
- •INTRO and ICND Course Outlines
- •Objectives and Methods
- •Book Features
- •How This Book Is Organized
- •Part I: LAN Switching
- •Part II: TCP/IP
- •Part III: Wide-Area Networks
- •Part IV: Network Security
- •Part V: Final Preparation
- •Part VI: Appendixes
- •How to Use These Books to Prepare for the CCNA Exam
- •For More Information
- •Part I: LAN Switching
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Brief Review of LAN Switching
- •The Forward-Versus-Filter Decision
- •How Switches Learn MAC Addresses
- •Forwarding Unknown Unicasts and Broadcasts
- •LAN Switch Logic Summary
- •Basic Switch Operation
- •Foundation Summary
- •Spanning Tree Protocol
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Spanning Tree Protocol
- •What IEEE 802.1d Spanning Tree Does
- •How Spanning Tree Works
- •Electing the Root and Discovering Root Ports and Designated Ports
- •Reacting to Changes in the Network
- •Spanning Tree Protocol Summary
- •Optional STP Features
- •EtherChannel
- •PortFast
- •Rapid Spanning Tree (IEEE 802.1w)
- •RSTP Link and Edge Types
- •RSTP Port States
- •RSTP Port Roles
- •RSTP Convergence
- •Edge-Type Behavior and PortFast
- •Link-Type Shared
- •Link-Type Point-to-Point
- •An Example of Speedy RSTP Convergence
- •Basic STP show Commands
- •Changing STP Port Costs and Bridge Priority
- •Foundation Summary
- •Foundation Summary
- •Virtual LANs and Trunking
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Review of Virtual LAN Concepts
- •Trunking with ISL and 802.1Q
- •ISL and 802.1Q Compared
- •VLAN Trunking Protocol (VTP)
- •How VTP Works
- •VTP Pruning
- •Foundation Summary
- •Part II: TCP/IP
- •IP Addressing and Subnetting
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •IP Addressing Review
- •IP Subnetting
- •Analyzing and Interpreting IP Addresses and Subnets
- •Math Operations Used to Answer Subnetting Questions
- •Converting IP Addresses from Decimal to Binary and Back Again
- •The Boolean AND Operation
- •How Many Hosts and How Many Subnets?
- •What Is the Subnet Number, and What Are the IP Addresses in the Subnet?
- •Finding the Subnet Number
- •Finding the Subnet Broadcast Address
- •Finding the Range of Valid IP Addresses in a Subnet
- •Finding the Answers Without Using Binary
- •Easier Math with Easy Masks
- •Which Subnet Masks Meet the Stated Design Requirements?
- •What Are the Other Subnet Numbers?
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Extended ping Command
- •Distance Vector Concepts
- •Distance Vector Loop-Avoidance Features
- •Route Poisoning
- •Split Horizon
- •Split Horizon with Poison Reverse
- •Hold-Down Timer
- •Triggered (Flash) Updates
- •RIP and IGRP
- •IGRP Metrics
- •Examination of RIP and IGRP debug and show Commands
- •Issues When Multiple Routes to the Same Subnet Exist
- •Administrative Distance
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Link-State Routing Protocol and OSPF Concepts
- •Steady-State Operation
- •Loop Avoidance
- •Scaling OSPF Through Hierarchical Design
- •OSPF Areas
- •Stub Areas
- •Summary: Comparing Link-State and OSPF to Distance Vector Protocols
- •Balanced Hybrid Routing Protocol and EIGRP Concepts
- •EIGRP Loop Avoidance
- •EIGRP Summary
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Route Summarization and Variable-Length Subnet Masks
- •Route Summarization Concepts
- •VLSM
- •Route Summarization Strategies
- •Sample “Best” Summary on Seville
- •Sample “Best” Summary on Yosemite
- •Classless Routing Protocols and Classless Routing
- •Classless and Classful Routing Protocols
- •Autosummarization
- •Classful and Classless Routing
- •Default Routes
- •Classless Routing
- •Foundation Summary
- •Advanced TCP/IP Topics
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Scaling the IP Address Space for the Internet
- •CIDR
- •Private Addressing
- •Network Address Translation
- •Static NAT
- •Dynamic NAT
- •Overloading NAT with Port Address Translation (PAT)
- •Translating Overlapping Addresses
- •Miscellaneous TCP/IP Topics
- •Internet Control Message Protocol (ICMP)
- •ICMP Echo Request and Echo Reply
- •Destination Unreachable ICMP Message
- •Time Exceeded ICMP Message
- •Redirect ICMP Message
- •Secondary IP Addressing
- •FTP and TFTP
- •TFTP
- •MTU and Fragmentation
- •Foundation Summary
- •Part III: Wide-Area Networks
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Review of WAN Basics
- •Physical Components of Point-to-Point Leased Lines
- •Data-Link Protocols for Point-to-Point Leased Lines
- •HDLC and PPP Compared
- •Looped Link Detection
- •Enhanced Error Detection
- •Authentication Over WAN Links
- •PAP and CHAP Authentication
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •ISDN Protocols and Design
- •Typical Uses of ISDN
- •ISDN Channels
- •ISDN Protocols
- •ISDN BRI Function Groups and Reference Points
- •ISDN PRI Function Groups and Reference Points
- •BRI and PRI Encoding and Framing
- •PRI Encoding
- •PRI Framing
- •BRI Framing and Encoding
- •DDR Step 1: Routing Packets Out the Interface to Be Dialed
- •DDR Step 2: Determining the Subset of the Packets That Trigger the Dialing Process
- •DDR Step 3: Dialing (Signaling)
- •DDR Step 4: Determining When the Connection Is Terminated
- •ISDN and DDR show and debug Commands
- •Multilink PPP
- •Foundation Summary
- •Frame Relay
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Frame Relay Protocols
- •Frame Relay Standards
- •Virtual Circuits
- •LMI and Encapsulation Types
- •DLCI Addressing Details
- •Network Layer Concerns with Frame Relay
- •Layer 3 Addressing with Frame Relay
- •Frame Relay Layer 3 Addressing: One Subnet Containing All Frame Relay DTEs
- •Frame Relay Layer 3 Addressing: One Subnet Per VC
- •Frame Relay Layer 3 Addressing: Hybrid Approach
- •Broadcast Handling
- •Frame Relay Service Interworking
- •A Fully-Meshed Network with One IP Subnet
- •Frame Relay Address Mapping
- •A Partially-Meshed Network with One IP Subnet Per VC
- •A Partially-Meshed Network with Some Fully-Meshed Parts
- •Foundation Summary
- •Part IV: Network Security
- •IP Access Control List Security
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Standard IP Access Control Lists
- •IP Standard ACL Concepts
- •Wildcard Masks
- •Standard IP ACL: Example 2
- •Extended IP Access Control Lists
- •Extended IP ACL Concepts
- •Extended IP Access Lists: Example 1
- •Extended IP Access Lists: Example 2
- •Miscellaneous ACL Topics
- •Named IP Access Lists
- •Controlling Telnet Access with ACLs
- •ACL Implementation Considerations
- •Foundation Summary
- •Part V: Final Preparation
- •Final Preparation
- •Suggestions for Final Preparation
- •Preparing for the Exam Experience
- •Final Lab Scenarios
- •Scenario 1
- •Scenario 1, Part A: Planning
- •Solutions to Scenario 1, Part A: Planning
- •Scenario 2
- •Scenario 2, Part A: Planning
- •Solutions to Scenario 2, Part A: Planning
- •Part VI: Appendixes
- •Glossary
- •Answers to the “Do I Know This Already?” Quizzes and Q&A Questions
- •Chapter 1
- •“Do I Know This Already?” Quiz
- •Chapter 2
- •“Do I Know This Already?” Quiz
- •Chapter 3
- •“Do I Know This Already?” Quiz
- •Chapter 4
- •“Do I Know This Already?” Quiz
- •Chapter 5
- •“Do I Know This Already?” Quiz
- •Chapter 6
- •“Do I Know This Already?” Quiz
- •Chapter 7
- •“Do I Know This Already?” Quiz
- •Chapter 8
- •“Do I Know This Already?” Quiz
- •Chapter 9
- •“Do I Know This Already?” Quiz
- •Chapter 10
- •“Do I Know This Already?” Quiz
- •Chapter 11
- •“Do I Know This Already?” Quiz
- •Chapter 12
- •“Do I Know This Already?” Quiz
- •Using the Simulation Software for the Hands-on Exercises
- •Accessing NetSim from the CD
- •Hands-on Exercises Available with NetSim
- •Scenarios
- •Labs
- •Listing of the Hands-on Exercises
- •How You Should Proceed with NetSim
- •Considerations When Using NetSim
- •Routing Protocol Overview
- •Comparing and Contrasting IP Routing Protocols
- •Routing Through the Internet with the Border Gateway Protocol
- •RIP Version 2
- •The Integrated IS-IS Link State Routing Protocol
- •Summary of Interior Routing Protocols
- •Numbering Ports (Interfaces)
326 Chapter 10: ISDN and Dial-on-Demand Routing
Foundation Topics
ISDN Protocols and Design
Integrated Services Digital Network (ISDN) provides switched (dialed) digital WAN services in increments of 64 kbps. Before ISDN, most dial services used the same analog lines that were connected to phones. Before ISDN was created, data rates using modems and analog phone lines typically did not exceed 9600 bits per second. The phone companies of the world created ISDN as a key building block for digital services of the future. They wanted to have a dialed digital service that not only allowed faster transmission rates but that also was pervasive as a simple analog line used for voice. Today, you could argue that the collective phone companies of the world were ultimately successful with these goals, but not totally successful: ISDN availability is widespread, but you can still find places where it is simply not available.
ISDN was created more than 20 years ago, and it began being widely deployed in the U.S. by the early 1990s. Competing technologies might eventually overtake the need for ISDN. As covered in Chapter 15, “Remote Access Technologies,” of CCNA INTRO Exam Certification Guide, for Internet access, ISDN has been usurped by competing technologies such as DSL, cable modems, and simply faster analog modems. ISDN remains a popular option for temporary connectivity between routers.
This chapter begins with some perspectives on when to use ISDN, followed by the technical details of the ISDN specifications. After that, you will read about how to configure ISDN.
Typical Uses of ISDN
One key reason to use dialed connections of any kind, including ISDN, might be to send and receive data for only short periods of time. “Occasional” connections might be used by a site for which instant access to data is not needed, but for which access is needed a few times per day. For example, a store might send in sales and resupply information overnight.
Routers frequently use ISDN to create a backup link when their primary leased line or Frame Relay connection is lost. Although the leased line or Frame Relay access link might seldom fail, when it does, a remote site might be completely cut off from the rest of the network.
Depending on the network’s business goals, long outages might not be acceptable, so ISDN could be used to dial back to the main site.
ISDN Protocols and Design 327
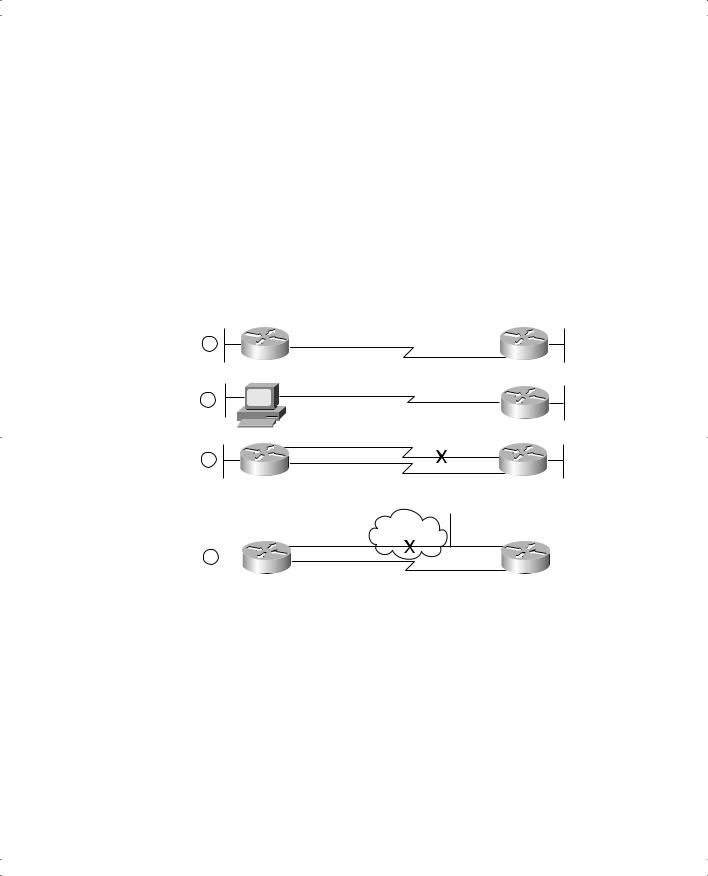
Figure 10-1 shows some typical network topologies when you’re using ISDN. These scenarios can be described as follows:
■Case 1 shows dial-on-demand routing. Logic is configured in the routers to trigger the dial when the user sends traffic that needs to get to another site.
■Case 2 shows a typical telecommuting environment.
■Case 3 shows a typical dial-backup topology. The leased line fails, so an ISDN call is established between the same two routers.
■Case 4 shows where an ISDN BRI can be used to dial directly to another router to replace a Frame Relay access link or a failed virtual circuit (VC).
Figure 10-1 Typical Occasional Connections Between Routers
1
|
ISDN |
2 |
|
Home |
Office |
|
3
ISDN
Frame Relay
4
ISDN
ISDN Channels
ISDN includes two types of interfaces: Basic Rate Interface (BRI) and Primary Rate Interface (PRI). Both BRI and PRI provide multiple digital bearer channels (B channels), over which temporary connections can be made and data can be sent. Because both BRI and PRI have multiple B channels, a single BRI or PRI line can have concurrent digital dial circuits to multiple sites, or multiple circuits to the same remote router to increase available bandwidth to that site.
B channels are used to transport data. B channels are called bearer channels because they bear or carry the data. B channels operate at speeds of up to 64 kbps, although the speed might be lower depending on the service provider.

328 Chapter 10: ISDN and Dial-on-Demand Routing
ISDN signals new data calls using the D channel. When a router creates a B channel call to another device using a BRI or PRI, it sends the phone number it wants to connect to inside a message sent across the D channel. The phone company’s switch receives the message and sets up the circuit. Signaling a new call over the D channel is effectively the same thing as picking up the phone and dialing a number to create a voice call.
The different types of ISDN lines are often described with a phrase that implies the number of each type of channel. For instance, BRIs are referred to as 2B+D, meaning two B channels and one D channel. PRIs based on T1 framing, as in the U.S., are referred to as 23B+D, and PRIs based on E1 framing are referred to as 30B+D. Table 10-2 lists the number of channels for each type of ISDN line and the terminology used to describe them.
Table 10-2 BRI and PRI B and D Channels
|
Number of Bearer (B) |
Number of Signaling |
|
Type of Interface |
Channels |
Channels |
Descriptive Term |
|
|
|
|
BRI |
2 |
1 (16 kbps) |
2B+D |
|
|
|
|
PRI (T1) |
23 |
1 (64 kbps) |
23B+D |
|
|
|
|
PRI (E1) |
30 |
1 (64 kbps) |
30B+D |
|
|
|
|
ISDN Protocols
The characterizations of several key protocols made by the Cisco ICND course are important for the exam. Table 10-3 is directly quoted from the ICND course. Be sure to learn the information in the Issue column. Knowing what each series of specifications is about is useful.
Table 10-3 ISDN Protocols
Issue |
Protocol |
Key Examples |
|
|
|
Telephone network and |
E-series |
E.163—International telephone numbering plan |
ISDN |
|
|
|
|
E.164—International ISDN addressing |
|
|
|
ISDN concepts, aspects, |
I-series |
I.100 series—Concepts, structures, and terminology |
and interfaces |
|
|
|
|
I.400 series—User-Network Interface (UNI) |
|
|
|
Switching and signaling |
Q-series |
Q.921—Link Access Procedure on the D channel |
|
|
(LAPD) |
|
|
Q.931—ISDN network layer |
|
|
|
ISDN Protocols and Design 329
The OSI layers correlating to the different ISDN specifications are also mentioned in the ICND course. It’s also useful to memorize the specifications listed in Table 10-4, as well as which OSI layer each specification matches.
Table 10-4 ISDN I-Series and Q-Series Mentioned in ICND: OSI Layer Comparison
Layer as |
|
|
|
Compared |
|
Equivalent Q-Series |
|
to OSI |
I-Series |
Specification |
Description |
|
|
|
|
1 |
ITU-T I.430 |
— |
Defines connectors, encoding, framing, |
|
|
|
and reference points. |
|
ITU-T I.431 |
|
|
|
|
|
|
2 |
ITU-T I.440 |
ITU-T Q.920 |
Defines the LAPD protocol used on |
|
|
|
the D channel to encapsulate signaling |
|
ITU-T I.441 |
ITU-T Q.921 |
requests. |
|
|
|
|
3 |
ITU-T I.450 |
ITU-T Q.930 |
Defines signaling messages, such as call |
|
|
|
setup and teardown messages. |
|
ITU-T I.451 |
ITU-T Q.931 |
|
|
|
|
|
NOTE A tool to help you remember the specifications and layers is that the second digit in the Q-series numbers matches the OSI layer. For example, in ITU-T Q.920, the second digit, 2, corresponds to OSI Layer 2. In the I-series, the second digit of the specification numbers is 2 more than the corresponding OSI layer. For example, I.430, with its second digit of 3, defines OSI Layer 1 equivalent functions.
Now that you have at least seen the names and numbers behind some of the ISDN protocols, you can concentrate on the more important protocols. The first of these is LAPD, defined in
Q.921, which is used as a data-link protocol across an ISDN D channel. Essentially, a router with an ISDN interface needs to send and receive signaling messages to and from the local ISDN switch to which it is connected. LAPD provides the data-link protocol that allows delivery of messages across that D channel to the local switch. Note that LAPD does not define the signaling messages. It just provides a data-link protocol that can be used to send the signaling messages.
The call setup and teardown messages themselves are defined by the Q.931 protocol. So, the local switch can receive a Q.931 call setup request from a router over the LAPD-controlled D channel, and it should react to that Q.931 message by setting up a circuit over the public network, as shown in Figure 10-2.
