
- •Warning and Disclaimer
- •Feedback Information
- •Trademark Acknowledgments
- •About the Author
- •About the Technical Reviewers
- •Dedication
- •Acknowledgments
- •Contents at a Glance
- •Contents
- •Icons Used in This Book
- •Command Syntax Conventions
- •Cisco’s Motivation: Certifying Partners
- •Format of the CCNA Exams
- •What’s on the CCNA Exams
- •ICND Exam Topics
- •Cross-Reference Between Exam Topics and Book Parts
- •CCNA Exam Topics
- •INTRO and ICND Course Outlines
- •Objectives and Methods
- •Book Features
- •How This Book Is Organized
- •Part I: LAN Switching
- •Part II: TCP/IP
- •Part III: Wide-Area Networks
- •Part IV: Network Security
- •Part V: Final Preparation
- •Part VI: Appendixes
- •How to Use These Books to Prepare for the CCNA Exam
- •For More Information
- •Part I: LAN Switching
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Brief Review of LAN Switching
- •The Forward-Versus-Filter Decision
- •How Switches Learn MAC Addresses
- •Forwarding Unknown Unicasts and Broadcasts
- •LAN Switch Logic Summary
- •Basic Switch Operation
- •Foundation Summary
- •Spanning Tree Protocol
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Spanning Tree Protocol
- •What IEEE 802.1d Spanning Tree Does
- •How Spanning Tree Works
- •Electing the Root and Discovering Root Ports and Designated Ports
- •Reacting to Changes in the Network
- •Spanning Tree Protocol Summary
- •Optional STP Features
- •EtherChannel
- •PortFast
- •Rapid Spanning Tree (IEEE 802.1w)
- •RSTP Link and Edge Types
- •RSTP Port States
- •RSTP Port Roles
- •RSTP Convergence
- •Edge-Type Behavior and PortFast
- •Link-Type Shared
- •Link-Type Point-to-Point
- •An Example of Speedy RSTP Convergence
- •Basic STP show Commands
- •Changing STP Port Costs and Bridge Priority
- •Foundation Summary
- •Foundation Summary
- •Virtual LANs and Trunking
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Review of Virtual LAN Concepts
- •Trunking with ISL and 802.1Q
- •ISL and 802.1Q Compared
- •VLAN Trunking Protocol (VTP)
- •How VTP Works
- •VTP Pruning
- •Foundation Summary
- •Part II: TCP/IP
- •IP Addressing and Subnetting
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •IP Addressing Review
- •IP Subnetting
- •Analyzing and Interpreting IP Addresses and Subnets
- •Math Operations Used to Answer Subnetting Questions
- •Converting IP Addresses from Decimal to Binary and Back Again
- •The Boolean AND Operation
- •How Many Hosts and How Many Subnets?
- •What Is the Subnet Number, and What Are the IP Addresses in the Subnet?
- •Finding the Subnet Number
- •Finding the Subnet Broadcast Address
- •Finding the Range of Valid IP Addresses in a Subnet
- •Finding the Answers Without Using Binary
- •Easier Math with Easy Masks
- •Which Subnet Masks Meet the Stated Design Requirements?
- •What Are the Other Subnet Numbers?
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Extended ping Command
- •Distance Vector Concepts
- •Distance Vector Loop-Avoidance Features
- •Route Poisoning
- •Split Horizon
- •Split Horizon with Poison Reverse
- •Hold-Down Timer
- •Triggered (Flash) Updates
- •RIP and IGRP
- •IGRP Metrics
- •Examination of RIP and IGRP debug and show Commands
- •Issues When Multiple Routes to the Same Subnet Exist
- •Administrative Distance
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Link-State Routing Protocol and OSPF Concepts
- •Steady-State Operation
- •Loop Avoidance
- •Scaling OSPF Through Hierarchical Design
- •OSPF Areas
- •Stub Areas
- •Summary: Comparing Link-State and OSPF to Distance Vector Protocols
- •Balanced Hybrid Routing Protocol and EIGRP Concepts
- •EIGRP Loop Avoidance
- •EIGRP Summary
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Route Summarization and Variable-Length Subnet Masks
- •Route Summarization Concepts
- •VLSM
- •Route Summarization Strategies
- •Sample “Best” Summary on Seville
- •Sample “Best” Summary on Yosemite
- •Classless Routing Protocols and Classless Routing
- •Classless and Classful Routing Protocols
- •Autosummarization
- •Classful and Classless Routing
- •Default Routes
- •Classless Routing
- •Foundation Summary
- •Advanced TCP/IP Topics
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Scaling the IP Address Space for the Internet
- •CIDR
- •Private Addressing
- •Network Address Translation
- •Static NAT
- •Dynamic NAT
- •Overloading NAT with Port Address Translation (PAT)
- •Translating Overlapping Addresses
- •Miscellaneous TCP/IP Topics
- •Internet Control Message Protocol (ICMP)
- •ICMP Echo Request and Echo Reply
- •Destination Unreachable ICMP Message
- •Time Exceeded ICMP Message
- •Redirect ICMP Message
- •Secondary IP Addressing
- •FTP and TFTP
- •TFTP
- •MTU and Fragmentation
- •Foundation Summary
- •Part III: Wide-Area Networks
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Review of WAN Basics
- •Physical Components of Point-to-Point Leased Lines
- •Data-Link Protocols for Point-to-Point Leased Lines
- •HDLC and PPP Compared
- •Looped Link Detection
- •Enhanced Error Detection
- •Authentication Over WAN Links
- •PAP and CHAP Authentication
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •ISDN Protocols and Design
- •Typical Uses of ISDN
- •ISDN Channels
- •ISDN Protocols
- •ISDN BRI Function Groups and Reference Points
- •ISDN PRI Function Groups and Reference Points
- •BRI and PRI Encoding and Framing
- •PRI Encoding
- •PRI Framing
- •BRI Framing and Encoding
- •DDR Step 1: Routing Packets Out the Interface to Be Dialed
- •DDR Step 2: Determining the Subset of the Packets That Trigger the Dialing Process
- •DDR Step 3: Dialing (Signaling)
- •DDR Step 4: Determining When the Connection Is Terminated
- •ISDN and DDR show and debug Commands
- •Multilink PPP
- •Foundation Summary
- •Frame Relay
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Frame Relay Protocols
- •Frame Relay Standards
- •Virtual Circuits
- •LMI and Encapsulation Types
- •DLCI Addressing Details
- •Network Layer Concerns with Frame Relay
- •Layer 3 Addressing with Frame Relay
- •Frame Relay Layer 3 Addressing: One Subnet Containing All Frame Relay DTEs
- •Frame Relay Layer 3 Addressing: One Subnet Per VC
- •Frame Relay Layer 3 Addressing: Hybrid Approach
- •Broadcast Handling
- •Frame Relay Service Interworking
- •A Fully-Meshed Network with One IP Subnet
- •Frame Relay Address Mapping
- •A Partially-Meshed Network with One IP Subnet Per VC
- •A Partially-Meshed Network with Some Fully-Meshed Parts
- •Foundation Summary
- •Part IV: Network Security
- •IP Access Control List Security
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Standard IP Access Control Lists
- •IP Standard ACL Concepts
- •Wildcard Masks
- •Standard IP ACL: Example 2
- •Extended IP Access Control Lists
- •Extended IP ACL Concepts
- •Extended IP Access Lists: Example 1
- •Extended IP Access Lists: Example 2
- •Miscellaneous ACL Topics
- •Named IP Access Lists
- •Controlling Telnet Access with ACLs
- •ACL Implementation Considerations
- •Foundation Summary
- •Part V: Final Preparation
- •Final Preparation
- •Suggestions for Final Preparation
- •Preparing for the Exam Experience
- •Final Lab Scenarios
- •Scenario 1
- •Scenario 1, Part A: Planning
- •Solutions to Scenario 1, Part A: Planning
- •Scenario 2
- •Scenario 2, Part A: Planning
- •Solutions to Scenario 2, Part A: Planning
- •Part VI: Appendixes
- •Glossary
- •Answers to the “Do I Know This Already?” Quizzes and Q&A Questions
- •Chapter 1
- •“Do I Know This Already?” Quiz
- •Chapter 2
- •“Do I Know This Already?” Quiz
- •Chapter 3
- •“Do I Know This Already?” Quiz
- •Chapter 4
- •“Do I Know This Already?” Quiz
- •Chapter 5
- •“Do I Know This Already?” Quiz
- •Chapter 6
- •“Do I Know This Already?” Quiz
- •Chapter 7
- •“Do I Know This Already?” Quiz
- •Chapter 8
- •“Do I Know This Already?” Quiz
- •Chapter 9
- •“Do I Know This Already?” Quiz
- •Chapter 10
- •“Do I Know This Already?” Quiz
- •Chapter 11
- •“Do I Know This Already?” Quiz
- •Chapter 12
- •“Do I Know This Already?” Quiz
- •Using the Simulation Software for the Hands-on Exercises
- •Accessing NetSim from the CD
- •Hands-on Exercises Available with NetSim
- •Scenarios
- •Labs
- •Listing of the Hands-on Exercises
- •How You Should Proceed with NetSim
- •Considerations When Using NetSim
- •Routing Protocol Overview
- •Comparing and Contrasting IP Routing Protocols
- •Routing Through the Internet with the Border Gateway Protocol
- •RIP Version 2
- •The Integrated IS-IS Link State Routing Protocol
- •Summary of Interior Routing Protocols
- •Numbering Ports (Interfaces)

260 Chapter 8: Advanced TCP/IP Topics
Table 8-2 RFC 1918 Private Address Space
Range of IP Addresses |
Class of Networks |
Number of Networks |
|
|
|
10.0.0.0 to 10.255.255.255 |
A |
1 |
|
|
|
172.16.0.0 to 172.31.255.255 |
B |
16 |
|
|
|
192.168.0.0 to 192.168.255.255 |
C |
256 |
|
|
|
In other words, any organization can use these network numbers. However, no organization is allowed to advertise these networks using a routing protocol on the Internet.
You might be wondering why you would bother to reserve special private network numbers when it doesn’t matter if the addresses are duplicates. Well, as it turns out, you can use private addressing in a network, and use the Internet at the same time, as long as you use Network Address Translation (NAT).
Network Address Translation
NAT, defined in RFC 1631, allows a host that does not have a valid registered IP address to communicate with other hosts through the Internet. The hosts might be using private addresses or addresses assigned to another organization. In either case, NAT allows these addresses that are not Internet-ready to continue to be used and still allows communication with hosts across the Internet.
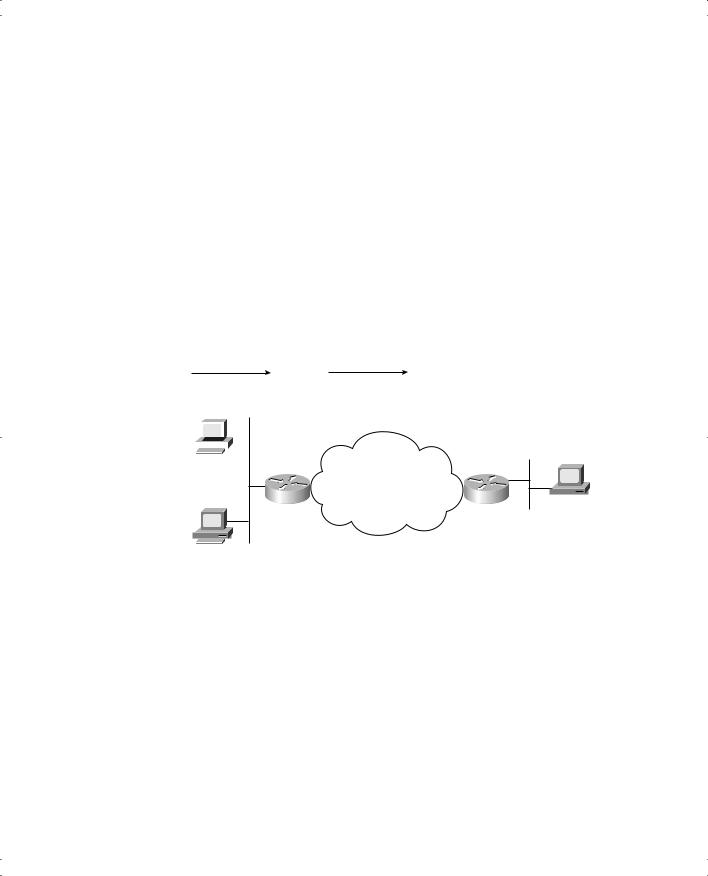
NAT achieves its goal by using a valid registered IP address to represent the private address to the rest of the Internet. The NAT function changes the private IP addresses to publicly registered IP addresses inside each IP packet, as shown in Figure 8-2.
Figure 8-2 NAT IP Address Swapping: Private Addressing
|
Client |
|
|
|
|
NAT |
|
|
|
Server |
||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||
|
|
|
|
|
|
Private |
|
|
|
|
Internet |
|
|
|
|
|
|
|
||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
10.1.1.1 |
|
|
|
|
|
|
|
|
|
www.cisco.com |
||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
170.1.1.1 |
|
|
|
||||||
|
Source |
Destination |
|
|
|
|
Source |
Destination |
||||||||||||||
|
10.1.1.1 |
170.1.1.1 |
........ |
|
|
|
200.1.1.1 |
170.1.1.1 |
|
|
........ |
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Source |
Destination |
|
|
|
|
Source |
Destination |
||||||||||||||
|
170.1.1.1 |
10.1.1.1 |
........ |
|
|
|
170.1.1.1 |
200.1.1.1 |
|
|
........ |
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Scaling the IP Address Space for the Internet 261
Notice that the router, performing NAT, changes the packet’s source IP address when leaving the private organization and the destination address in each packet forwarded back into the private network. (Network 200.1.1.0 is registered in Figure 8-2.) The NAT feature, configured in the router labeled NAT, performs the translation.
Cisco IOS software supports several variations of NAT. The next few pages cover the concepts behind several of these variations. The section after that covers the configuration related to each option.
Static NAT
Static NAT works just like the example shown in Figure 8-2, but with the IP addresses statically mapped to each other. To help you understand the implications of static NAT, and to explain several key terms, Figure 8-3 shows a similar example with more information.
Figure 8-3 Static NAT Showing Inside Local and Global Addresses
|
|
SA 10.1.1.1 |
|
|
|
SA 200.1.1.1 |
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
10.1.1.1 |
Server |
|
Internet
NAT  170.1.1.1
170.1.1.1
10.1.1.2
Private Address |
Public Address |
10.1.1.1 |
200.1.1.1 |
10.1.1.2 |
200.1.1.2 |
|
|
First, the concepts. The company’s ISP has assigned it registered network 200.1.1.0. Therefore, the NAT router must make the private IP addresses look like they are in network 200.1.1.0. To do so, the NAT router changes the source IP addresses in the packets going left to right in the figure.
In this example, the NAT router changes the source address (“SA” in the figure) of 10.1.1.1 to 200.1.1.1. With static NAT, the NAT router simply configures a one-to-one mapping between the private address and the registered address that is used on its behalf. The NAT router has statically configured a mapping between private address 10.1.1.1 and public, registered address 200.1.1.1.

262 Chapter 8: Advanced TCP/IP Topics
Supporting two IP hosts in the private network requires a second static one-to-one mapping using a second IP address in the public address range. For instance, to support 10.1.1.2, the router statically maps 10.1.1.2 to 200.1.1.2. Because the enterprise has a single registered Class C network, it can support at most 254 private IP addresses with NAT.
The terminology used with NAT, particularly with configuration, can be a little confusing. Notice in Figure 8-3 that the NAT table lists the private IP addresses as “private” and the public, registered addresses from network 200.1.1.0 as “public.” Cisco uses the term inside local for the private IP addresses in this example and inside global for the public IP addresses.
In Cisco terminology, the enterprise network that uses private addresses, and therefore that needs NAT, is the “inside” part of the network. The Internet side of the NAT function is the
“outside” part of the network. A host that needs NAT (such as 10.1.1.1 in the example) has the IP address it uses inside the network, and it needs an IP address to represent it in the outside network. So, because the host essentially needs two different addresses to represent it, you need two terms. Cisco calls the private IP address used in the “inside” network the inside local address and the address used to represent the host to the rest of the Internet the inside global address. (Although Cisco doesn’t use these exact terms, sometimes substituting “private” for “local” and “public” for “global” makes a little more sense to many people. Just keep all terms in mind for the exam.)
Figure 8-4 repeats the same example, with some of the terminology shown.
Figure 8-4 Static NAT Terminology
|
|
SA 10.1.1.1 |
|
|
|
SA 200.1.1.1 |
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Server |
|||||
10.1.1.1 |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Internet |
|
|
|
|
|
|
|
||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
NAT |
|
|
|
|
|
|
|
|||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
170.1.1.1 |
||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
10.1.1.2 |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
Inside |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Outside |
|||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||||||
|
|
DA 10.1.1.1 |
|
|
|
|
|
|
DA 200.1.1.1 |
|
|
|
|
|
|
|
|
|
|
|||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Inside Local |
|
|
|
|
Inside Global |
|
|
|
|
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
|
10.1.1.1 |
|
|
200.1.1.1 |
|
|
|
|
|
|
|
|
|
|
|
|
||||||||||
|
|
|
|
10.1.1.2 |
|
|
200.1.1.2 |
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|

Scaling the IP Address Space for the Internet 263
Most typical NAT features change only the IP address of “inside” hosts. Therefore, the current NAT table shown in Figure 8-4 shows the inside local and corresponding inside global registered addresses. However, the outside host IP address can also be changed with NAT. When that occurs, the terms outside local and outside global are used to denote the IP address used to represent that host in the inside network and the outside network, respectively. An example later in this section explains more about translating outside addresses. Table 8-3 summarizes the terminology and meanings.
Table 8-3 NAT Addressing Terms
Term |
Meaning |
|
|
Inside local |
In a typical NAT design, the term “inside” refers to an address used for a |
|
host inside an enterprise. An inside local is the actual IP address assigned to a |
|
host in the private enterprise network. A more descriptive term might be |
|
“inside private,” because when using RFC 1918 addresses in an enterprise, |
|
the inside local represents the host inside the enterprise, and it is a private |
|
RFC 1918 address. |
|
|
Inside global |
In a typical NAT design, the term “inside” refers to an address used for a |
|
host inside an enterprise. NAT uses an inside global address to represent the |
|
inside host as the packet is sent through the outside network, typically the |
|
Internet. A NAT router changes the source IP address of a packet sent by an |
|
inside host from an inside local address to an inside global address as the |
|
packet goes from the inside to the outside network. |
|
A more descriptive term might be “inside public,” because when using RFC |
|
1918 addresses in an enterprise, the inside global represents the inside host |
|
with a public IP address that can be used for routing in the public Internet. |
|
|
Outside global |
In a typical NAT design, the term “outside” refers to an address used for a |
|
host outside an enterprise—in other words, in the Internet. An outside global |
|
is the actual IP address assigned to a host that resides in the outside network, |
|
typically the Internet. A more descriptive term might be “outside public,” |
|
because the outside global represents the outside host with a public IP |
|
address that can be used for routing in the public Internet. |
|
|
Outside local |
In a typical NAT design, the term “outside” refers to an address used for a |
|
host outside an enterprise—in other words, in the Internet. NAT uses an |
|
outside local address to represent the outside host as the packet is sent |
|
through the private enterprise network (inside network). A NAT router |
|
changes a packet’s destination IP address, sent from an inside host to the |
|
outside global address, as the packet goes from the inside to the outside |
|
network. A more descriptive term might be “outside private,” because when |
|
using RFC 1918 addresses in an enterprise, the outside local represents the |
|
outside host with a private IP address from RFC 1918. |
|
|
