
- •Acknowledgments
- •Introduction
- •Assessment Test
- •Answers to Assessment Test
- •Service Provider Networks
- •Scalability
- •Traffic Engineering
- •Quality of Service
- •MPLS Label Stack
- •Shim Header
- •MPLS Architecture
- •Control
- •Forwarding
- •MPLS Label Switching
- •MPLS Network Components
- •Device Output
- •Label-Switched Paths
- •MPLS Applications
- •MPLS and ATM
- •Overlay
- •Quality of Service
- •Traffic Engineering
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •Routing Review
- •Frame-Mode MPLS Working Example
- •Network Routing Protocol Examples
- •MPLS Step by Step
- •Label Distribution
- •Assigning Labels
- •Troubleshooting and Verification
- •Device Configuration
- •IGP Verification
- •CEF Verification
- •MPLS Verification
- •Label Distribution and Bindings
- •Binding Verification
- •Troubleshooting the Network
- •Hiding Service Provider Devices
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •Frame-Mode MPLS and ATM
- •Frame-Mode MPLS and ATM Configuration
- •Cell-Mode MPLS
- •Label Binding with ATM
- •Cell-Mode Label Switching
- •VC Merge
- •Loop Prevention
- •Cell-Mode MPLS Configuration
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •VPNs 101
- •Point-to-Point Connections
- •Virtual Private Networks
- •Categories of VPNs
- •VPN Routing
- •Peer-to-Peer VPNs
- •Optimal Routing
- •Peer-to-Peer Security
- •Peer-to-Peer VPN Routing
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •Service Provider Configuration
- •MPLS VPNs
- •Virtual Router
- •Virtual Routing and Forwarding Tables
- •MPLS Operational Overview
- •MP-BGP Configuration
- •An MPLS VPN Example
- •Route Distinguisher
- •MP-IBGP Configuration Example
- •Initial Network Configuration
- •MP-IBGP Configuration
- •Verification
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •A Review of VPNs
- •Configuring a Simple MPLS VPN
- •Configuring VRF Interfaces
- •Running RIP in an MPLS VPN
- •Configuring RIPv2 with Address-Family ipv4
- •Configuring Redistribution
- •Route Targets
- •Configuring Route Targets
- •A Review of Simple VPN Configuration
- •Configuring MPLS in the Service Provider Network
- •Simple VPN Configuration
- •Configuring the PE-CE Routing Protocol
- •Lab: Configuring an MPLS VPN
- •Configuring POP Routers
- •VPN Configuration
- •Raleigh Running-Config
- •Atlanta Running-Config
- •Peer 1 Running-Config
- •Peer 2 Running-Config
- •Verification with Ping
- •Routing Table Isolation
- •Verifying VRF Routes
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •MP-BGP and OSPF
- •A Review of OSPF
- •OSPF Router Types
- •Link State Advertisements
- •OSPF for MPLS VPNs
- •OSPF Super-Backbone
- •Preventing Routing Loops
- •Path Selection
- •MPLS VPN OSPF Lab
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •Static Routing
- •Device Configuration
- •VPN Configuration
- •Raleigh Running-Config
- •Atlanta Running-Config
- •Peer Router Configuration
- •Verification with Ping
- •Verifying Static VRF Routes
- •E-BGP and MPLS VPNs
- •Device Configuration
- •E-BGP Operation
- •AS-Override
- •VPN Configuration
- •Raleigh Running-Config
- •Atlanta Running-Config
- •Peer Router Configuration
- •Peer 1 Running-Config
- •Peer 2 Running-Config
- •Verification with Ping
- •Advanced MPLS VPN Topologies
- •Simple VPNs
- •Central Services MPLS VPN Topology
- •Overlay MPLS VPN Topology
- •Summary
- •Exam Essentials
- •Key Terms
- •Review Questions
- •Answers to Review Questions
- •Challenge Lab 1
- •MPLS
- •MP-IBGP
- •Answer to Lab 1.1
- •Answer to Lab 1.2
- •Answer to Lab 1.3
- •Challenge Lab 2
- •Tag Switching
- •MP-IBGP
- •Answer to Lab 2.1
- •Answer to Lab 2.2
- •Answer to Lab 2.3
- •Challenge Lab 3
- •VRF Configuration
- •RIPv2
- •Redistribution
- •Answer to Lab 3.1
- •Answer to Lab 3.2
- •Answer to Lab 3.3
- •Challenge Lab 4
- •VRF Configuration
- •OSPF
- •Redistribution
- •Answer to Lab 4.1
- •Answer to Lab 4.2
- •Answer to Lab 4.3
- •Challenge Lab 5
- •VRF Configuration
- •Static Routes and Redistribution
- •Answer to Lab 5.1
- •Answer to Lab 5.2
- •Challenge Lab 6
- •VRF Configuration
- •E-BGP Configuration
- •Answer to Lab 6.1
- •Answer to Lab 6.2
- •Service Provider Network Configuration with OSPF
- •Router Configuration
- •Routing Tables
- •Tags
- •Service Provider Network Configuration with IS-IS
- •Router Configuration
- •Routing Tables
- •Tag Switching Forwarding Tables
- •Glossary
152 Chapter 4 VPNs: An Overview
Answers to Review Questions
1.A. Point-to-point connections are expensive. VPNs emerged as a cheaper alternative with the same security and privacy.
2.D. The major overlay VPN topologies are full-mesh, partial-mesh, and hub-and-spoke.
3.C. Since most financial organizations have centralized resources that need to be accessed by remote branch offices, a hub-and-spoke topology is usually used for their networks.
4.A. To ensure optimal routing between sites, a full-mesh topology is the best alternative.
5.B. With overlay VPNs, a customer router is not aware of the service provider infrastructure.
6.C. Hands down, peer-to-peer VPNs require the most management to implement proper security.
7.A. With peer-to-peer VPNs, customer routers are aware of the service provider infrastructure because they peer with the service provider routers.
8.B. A shared router peer-to-peer VPN has the most security problems because different customers connect to the same router.
9.A. A peer-to-peer VPN ensures optimal traffic flow. To implement optimal traffic flow between sites with an overlay VPN, a full-mesh topology is required.
10.C. A hub-and-spoke topology, with the least number of VCs, is the least expensive of all overlay VPNs to implement.
11.C. IPSec and GRE are Layer 3 VPN technologies.
12.D. ISDN is a Layer 1 VPN technology. Other technologies at Layer 1 are E1, T1, and SONET.
13.A. In an intranet, sites from the same company or organization are connected in a single network.
14.B. An extranet is when sites from different companies or organizations are connected.
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
Answers to Review Questions 153
15.B. Frame Relay and ATM are Layer 2 VPN technologies. An additional technology at Layer 2 is X.25.
16.A. If you have the money, nothing beats a full-mesh topology for redundancy.
17.A. A dedicated router peer-to-peer VPN requires that each VPN have its own dedicated router used only for that VPN. Dedicated router peer-to-peer VPNs are the most expensive to implement.
18.C. A hub-and-spoke topology is often used by financial organizations because they usually have centralized resources that need to be accessed by remote branch offices.
19.B. In a peer-to-peer VPN, the service provider becomes responsible for routing protocol convergence.
20.A, D. The two ways to implement peer-to-peer VPNs are dedicated router and shared router.
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
Chapter
5
MPLS VPNs
CCIP MPLS EXAM TOPICS COVERED IN THIS CHAPTER:
Describe the major architectural blocks of MPLS VPN.
Describe the MPLS VPN routing model and packet forwarding.
Identify the IOS commands and their proper syntax used to configure virtual routing and forwarding tables.
Identify the IOS commands and their proper syntax used to configure Multi-Protocol BGP in MPLS VPN backbone.
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |

Here in Chapter 5, I’ll begin to pull together all the information you’ve learned so far. This chapter starts with a walk-through of the configuration tasks required to configure an IGP, BGP between edge routers, and MPLS. MPLS VPNs are discussed from a 35,000-foot view. You’ll learn about the virtual routing and forwarding tables and about route distinguishers. You will also learn the ins and outs of their configuration.
There is a great deal of configuration required to make MPLS VPNs work. This chapter describes only the basic configuration required to get the network set up to support MPLS VPNs. What you learn in this chapter will be complemented by a discussion in Chapter 6, “MPLS VPNs and RIP,” of routing inside MPLS VPNs and several configuration exercises.
Pay close attention to the configuration commands for MPLS, MP-BGP, and MPLS VPNs discussed in this chapter. Take things slow. This chapter gets you ready for the full-blown end-to-end service provider implementation described in Chapter 6.
Service Provider Configuration
Before talking about MPLS VPNs, let’s put all the pieces together.
MPLS VPNs are an add-on service to an already-up-and-functioning MPLS network.
To start with, you’ve already been exposed to everything necessary to configure a simple network for MPLS support. You may remember a few things from previous chapters. The service provider network runs an IGP (such as OSPF or IS-IS) on all provider devices. BGP is configured only on the network’s edge.
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
Service Provider Configuration 157
The reason you’re doing all the configuration in this chapter is so that you’re aware of all the technologies running in the background that make an MPLS network really work. The next section of this chapter talks about configuring MPLS VPNs in a service provider network where MPLS is already set up.
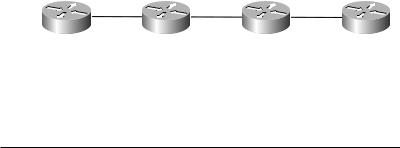
So, let’s get to the service provider network configuration. Figure 5.1 illustrates a simple network with just the service provider devices.
F I G U R E 5 . 1 A simple service provider network
Serial |
0/0 |
Serial |
0/0 |
Serial |
0/1 |
Serial |
0/0 |
Serial |
0/1 |
Serial |
0/0 |
|
|
|
|
|
|
PE1 P1 P2 PE2
Table 5.1 lists the IP addresses and interfaces of all the service provider devices in Figure 5.1.
T A B L E 5 . 1 Service Provider IP Addressing
Device |
Serial 0/0 |
Serial 0/1 |
Loopback 0 |
|
|
|
|
PE1 |
192.168.1.10 |
|
192.168.1.1 |
P1 |
192.168.1.9 |
192.168.1.14 |
192.168.1.2 |
P2 |
192.168.1.13 |
192.168.1.18 |
192.168.1.3 |
PE2 |
192.168.1.17 |
|
192.168.1.4 |
|
|
|
|
Assuming that you already know how to configure hostnames, bring interfaces up, assign IP addresses, and the like, the first task is to configure all the routing protocols. To avoid confusion with basic IGP routing, let’s use RIPv2 in this configuration example.
On router PE1, you configure RIPv2 with the following commands:
PE1#config t
PE1(config)#router rip
PE1(config-router)#version 2
PE1(config-router)#network 192.168.1.0
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
158 Chapter 5 MPLS VPNs
On router P1, you configure RIPv2 with the following commands:
P1#config t
P1(config)#router rip
P1(config-router)#version 2
P1(config-router)#network 192.168.1.0
On router P2, you configure RIPv2 with the following commands:
P2#config t
P2(config)#router rip
P2(config-router)#version 2
P2(config-router)#network 192.168.1.0
On router PE2, you configure RIPv2 with the following commands:
PE2#config t
PE2(config)#router rip
PE2(config-router)#version 2
PE2(config-router)#network 192.168.1.0
Now that you have an IGP up and running, the next thing you need to do is configure BGP on the PE routers.
On router PE1, you configure BGP with the following commands:
PE1#config t
PE1(config)#router bgp 1 PE1(config-router)#no synchronization
PE1(config-router)#network 192.168.1.1 mask 255.255.255.255 PE1(config-router)#neighbor 192.168.1.4 remote-as 1 PE1(config-router)#neighbor 192.168.1.4 update-source Loopback0
PE1(config-router)#no auto summary PE1(config-router)#redistribute static
On router PE2, you configure BGP with the following commands:
PE2#config t
PE2(config)#router bgp 1 PE2(config-router)#no synchronization
PE2(config-router)#network 192.168.1.4 mask 255.255.255.255 PE2(config-router)#neighbor 192.168.1.1 remote-as 1 PE2(config-router)#neighbor 192.168.1.1 update-source Loopback0
PE2(config-router)#no auto summary PE2(config-router)#redistribute static
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
Service Provider Configuration 159
Now that all the routing protocols are in place, the final task is to enable MPLS on PE1, P1, P2, and PE2.
On PE1, you configure MPLS for Serial 0/0 only with the following commands:
PE1#config t
PE1(config)#ip cef
PE1(config)#mpls ip
PE1(config-if)#interface serial 0/0
PE1(config-if)#mpls ip
On P1, you configure MPLS for both Serial 0/0 and Serial 0/1 with the following commands:
P1#config t
P1(config)#ip cef
P1(config)#mpls ip
P1(config-if)#interface serial 0/0
P1(config-if)#mpls ip
P1(config-if)#exit
P1(config)#interface serial 0/1
P1(config-if)#mpls ip
On P2, you configure MPLS for both Serial 0/0 and Serial 0/1 with the following commands:
P2#config t
P2(config)#ip cef
P2(config)#mpls ip
P2(config-if)#interface serial 0/0
P2(config-if)#mpls ip
P2(config-if)#exit
P2(config)#interface serial 0/1
P2(config-if)#mpls ip
On PE2, you configure MPLS for Serial 0/0 only with the following commands:
PE2#config t
PE2(config)#ip cef
PE2(config)#mpls ip
PE2(config-if)#interface serial 0/0
PE2(config-if)#mpls ip
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
160 Chapter 5 MPLS VPNs
So you can see from these sets of commands that setting up MPLS is pretty easy: an IGP on all routers, BGP on the edge routers, and MPLS configured globally and then specified for an interface. Piece of cake, eh?
If you want to configure tag switching, you configure an IGP, BGP, and then tag switching on the same device. The commands to configure tag switching are described in the next few paragraphs.
On PE1, you configure tag switching for Serial 0/0 only with the following commands:
PE1#config t
PE1(config)#ip cef
PE1(config)#tag-switching advertise tags
PE1(config-if)#interface serial 0/0
PE1(config-if)#tag-switching ip
On P1, you configure tag switching for both Serial 0/0 and Serial 0/1 with the following commands:
P1#config t
P1(config)#ip cef
P1(config)#tag-switching advertise tags
P1(config-if)#interface serial 0/0
P1(config-if)#tag-switching ip
P1(config-if)#exit
P1(config)#interface serial 0/1
P1(config-if)#tag-switching ip
On P2, you configure tag switching for both Serial 0/0 and Serial 0/1 with the following commands:
P2#config t
P2(config)#ip cef
P2(config)#tag-switching advertise tags
P2(config-if)#interface serial 0/0
P2(config-if)#tag-switching ip
P2(config-if)#exit
P2(config)#interface serial 0/1
P2(config-if)#tag-switching ip
On PE2, you configure tag switching for Serial 0/0 only with the following commands:
PE1#config t
PE1(config)#ip cef
Copyright ©2002 SYBEX, Inc., Alameda, CA |
www.sybex.com |
