
- •Icons Used in This Book
- •Network Security
- •Vulnerabilities
- •Threats
- •Types of Attacks
- •Network Security Policy
- •AVVID and SAFE
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Firewall Technologies
- •Cisco PIX Firewall
- •Foundation Summary
- •The Cisco Secure PIX Firewall
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of the Cisco PIX Firewall
- •Cisco PIX Firewall Models and Features
- •Foundation Summary
- •System Maintenance
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Accessing the Cisco PIX Firewall
- •Installing a New Operating System
- •Upgrading the Cisco PIX OS
- •Creating a Boothelper Diskette Using a Windows PC
- •Auto Update Support
- •Password Recovery
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •How the PIX Firewall Handles Traffic
- •Address Translation
- •Translation Versus Connection
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Access Modes
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •TurboACL
- •Object Grouping
- •Advanced Protocol Handling
- •Foundation Summary
- •Syslog
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •How Syslog Works
- •How Log Messages Are Organized
- •How to Read System Log Messages
- •Disabling Syslog Messages
- •Foundation Summary
- •Cisco PIX Firewall Failover
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •What Causes a Failover Event
- •What Is Required for a Failover Configuration
- •Failover Monitoring
- •Stateful Failover
- •LAN-Based Failover
- •Foundation Summary
- •Virtual Private Networks
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of VPN Technologies
- •Cisco VPN Client
- •PPPoE Support
- •Foundation Summary
- •Scenario
- •Completed PIX Configurations
- •PIX Device Manager
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •PDM Overview
- •PIX Firewall Requirements to Run PDM
- •Foundation Summary
- •Content Filtering with the Cisco PIX Firewall
- •“Do I Know This Already?” Quiz
- •Filtering Java Applets
- •Filtering ActiveX Objects
- •Filtering URLs
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of AAA and the Cisco PIX Firewall
- •Cisco Secure Access Control Server (CSACS)
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Specifying Your AAA Servers
- •Troubleshooting Your AAA Setup
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Multimedia Support on the Cisco PIX Firewall
- •Attack Guards
- •PIX Firewall’s Intrusion Detection Feature
- •ip verify reverse-path Command
- •Foundation Summary
- •Answers to the “Do I Know This Already?” Quizzes and Q&A Questions
- •Chapter 1
- •Chapter 2
- •Chapter 3
- •Chapter 4
- •Chapter 5
- •Chapter 6
- •Chapter 7
- •Chapter 8
- •Chapter 9
- •Chapter 10
- •Chapter 11
- •Chapter 12
- •Chapter 13
- •Chapter 14
- •Chapter 15
- •Appendix B
- •What’s Wrong with This Picture?
Foundation Summary 269
Foundation Summary
Authentication, authorization, and accounting are three separate functions performed by AAA servers to allow access to resources. Each of these functions has a specific goal. No one is granted access of any kind until he or she is authenticated.
•
•
•
Authentication—Identifies the entity (user).
Authorization—Gives the user access based on his or her profile.
Accounting—Maintains a record of user access.
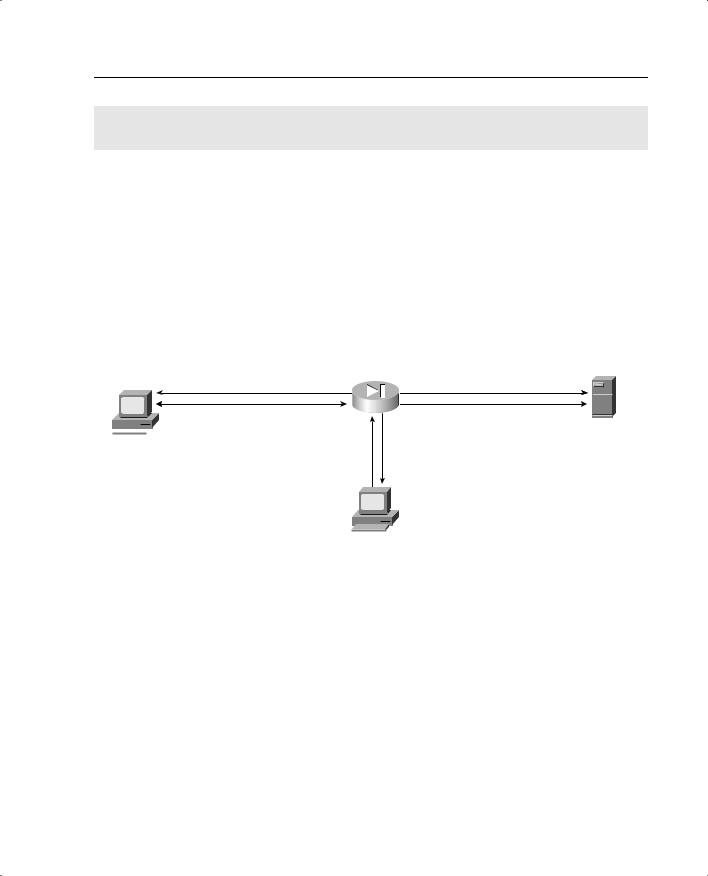
The Cisco PIX Firewall can maintain an internal user database or connect to an external AAA server. The PIX supports both RADIUS and TACACS+ technologies. Figure 13-14 shows the steps that the AAA server takes during the entire AAA process.
Figure 13-14 AAA Server Steps
Step 1: User initiates connection to Web server and is prompted for username/password.
Step 2: NAS forwards user
 information to AAA for User authentication.
information to AAA for User authentication.
Workstation
Step 3: AAA server returns authentication and authorization to NAS.
Step 5: The firewall allows the connection.
Internal
Web Server
Step 4: AAA server logs the |
|
connection (by user). |
AAA Server |
CSACS is available for both Windows NT/2000 Server and UNIX and can be configured for TACACS+ and RADIUS. The CSACS installation on Windows 2000 is an easy step- by-step (Install Wizard) installation.

270 Chapter 13: Overview of AAA and the Cisco PIX Firewall
Q&A
As mentioned in the Introduction, the questions in this book are more difficult than what you should experience on the exam. The questions do not attempt to cover more breadth or depth than the exam; however, they are designed to make sure that you know the answer. Hopefully, these questions will help limit the number of exam questions on which you narrow your choices to two options and then guess. Be sure to use the CD and take the simulated exams.
The answers to these questions can be found in Appendix A.
1What platforms does CSACS support?
A Windows XP Professional
BUNIX
CWindows NT Workstation
DWindows 2000 Professional
2Why is it important to do accounting on your network?
3What options are available to authenticate users on a PIX Firewall?
A Local user database
B Remote RADIUS server
C Remote TACACS+ server
D All of the above
4What two technologies does the CSACS support?
5True or false: Cut-through proxy authenticates users and then allows them to connect to
anything.
6True or false: The CSACS installation on Windows NT/2000 Server is a relatively simple Installation Wizard.
7Which of the following are not connection types for authenticating to a PIX Firewall? (Select all that apply.)
ATelnet
BSSH
CFTP
DHTTPS

This chapter covers the following exam topics for the Secure PIX Firewall Advanced Exam (CSPFA 9E0-111):
29. Overview of AAA
20. Installation of CSACS for Windows NT/2000
31.Authentication configuration
32.Downloadable ACLs
