
- •Icons Used in This Book
- •Network Security
- •Vulnerabilities
- •Threats
- •Types of Attacks
- •Network Security Policy
- •AVVID and SAFE
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Firewall Technologies
- •Cisco PIX Firewall
- •Foundation Summary
- •The Cisco Secure PIX Firewall
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of the Cisco PIX Firewall
- •Cisco PIX Firewall Models and Features
- •Foundation Summary
- •System Maintenance
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Accessing the Cisco PIX Firewall
- •Installing a New Operating System
- •Upgrading the Cisco PIX OS
- •Creating a Boothelper Diskette Using a Windows PC
- •Auto Update Support
- •Password Recovery
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •How the PIX Firewall Handles Traffic
- •Address Translation
- •Translation Versus Connection
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Access Modes
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •TurboACL
- •Object Grouping
- •Advanced Protocol Handling
- •Foundation Summary
- •Syslog
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •How Syslog Works
- •How Log Messages Are Organized
- •How to Read System Log Messages
- •Disabling Syslog Messages
- •Foundation Summary
- •Cisco PIX Firewall Failover
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •What Causes a Failover Event
- •What Is Required for a Failover Configuration
- •Failover Monitoring
- •Stateful Failover
- •LAN-Based Failover
- •Foundation Summary
- •Virtual Private Networks
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of VPN Technologies
- •Cisco VPN Client
- •PPPoE Support
- •Foundation Summary
- •Scenario
- •Completed PIX Configurations
- •PIX Device Manager
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •PDM Overview
- •PIX Firewall Requirements to Run PDM
- •Foundation Summary
- •Content Filtering with the Cisco PIX Firewall
- •“Do I Know This Already?” Quiz
- •Filtering Java Applets
- •Filtering ActiveX Objects
- •Filtering URLs
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Overview of AAA and the Cisco PIX Firewall
- •Cisco Secure Access Control Server (CSACS)
- •Foundation Summary
- •How to Best Use This Chapter
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Specifying Your AAA Servers
- •Troubleshooting Your AAA Setup
- •Foundation Summary
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Multimedia Support on the Cisco PIX Firewall
- •Attack Guards
- •PIX Firewall’s Intrusion Detection Feature
- •ip verify reverse-path Command
- •Foundation Summary
- •Answers to the “Do I Know This Already?” Quizzes and Q&A Questions
- •Chapter 1
- •Chapter 2
- •Chapter 3
- •Chapter 4
- •Chapter 5
- •Chapter 6
- •Chapter 7
- •Chapter 8
- •Chapter 9
- •Chapter 10
- •Chapter 11
- •Chapter 12
- •Chapter 13
- •Chapter 14
- •Chapter 15
- •Appendix B
- •What’s Wrong with This Picture?
148 Chapter 9: Cisco PIX Firewall Failover
Stateful Failover
In stateful failover mode, more information is shared about the connections that have been established with the standby unit by the active unit. The active unit shares per-connection state information with the standby unit. If and when an active unit fails over to the standby unit, an application does not reinitiate its connection. This is because stateful information from the active unit updates the standby unit.
NOTE |
Some applications are latency-sensitive. In some cases, the application times out before the |
|
failover sequence is completed. In these cases, the application must reestablish the session. |
|
|
|
Replicated state information includes the following: |
•
•
•
•
TCP connection table, including timeout information for each connection
Translation (xlate) table and status
Negotiated H.323 UDP ports
Port allocation table bitmap for PAT
Because failover cannot be prescheduled, the state update for the connection is packetbased. This means that every packet passes through the PIX and changes a connection’s state, which might trigger a state update.
However, some state information does not get updated to the standby unit in a stateful failover:
•
•
•
•
The user authentication (uauth) table
ISAKMP and the IPSec SA table
ARP table
Routing information
Most UDP state tables are not transferred, with the exception of dynamically opened ports corresponding to multichannel protocols such as H.323.
In addition to the failover cable, stateful failover setup requires a 100-Mbps or Gigabit Ethernet interface to be used exclusively for passing state information between the active and standby units. IP protocol 105 is used to pass data over this interface.
The stateful failover interface can be connected to any of the following:
•Category 5 crossover cable directly connecting the primary unit to the secondary unit
•1000BASE-TX half-duplex switch using straight Category 5 cables
•100BASE-TX full duplex on a dedicated switch or a switch’s dedicated VLAN
•1000BASE-TX full duplex on a switch’s dedicated VLAN
LAN-Based Failover 149
NOTE A Cisco PIX Firewall with two FDDI cards cannot use stateful failover, because an additional Ethernet interface with FDDI is not supported in stateful failover.
LAN-Based Failover
The distance restriction of 6 feet of serial cable between two PIX devices in a failover configuration is no longer a limitation starting with PIX version 6.2. LAN-based failover is a new feature (available only on PIX 6.2) that extends PIX failover functionality to operate through a dedicated LAN interface without the serial failover cable. This feature provides for a choice of configuration when it comes to failover configuration on the PIX.
The obvious benefit of LAN-based failover is removing the 6-foot distance limitation from the PIX devices in a failover configuration. However, another benefit is not so obvious. It provides an alternative path for stateful information if the failover interface goes down. For example, if the failover interface goes down, the PIX informs the peer through the other interfaces of the active PIX’s status. To configure LAN-based failover, you need a dedicated switch or hub (or VLAN) to connect the PIX failover pair so that the secondary unit can detect the failure of the primary unit’s dedicated LAN failover interface and become active.
The weakness of LAN-based failover is the delayed detection of its peer power loss, consequently causing a relatively longer period for failover to occur.
NOTE Crossover Ethernet cables cannot be used to connect the LAN-based failover interface. Additionally, it is recommended that you dedicate a LAN interface for LAN-based failover, but the interface can be shared with stateful failover under lightly loaded configurations.
Cisco PIX Firewall software version 6.2 enhances failover functionality so that the standby unit in a PIX failover pair can be configured to use a virtual MAC address. This eliminates potential “stale” ARP entry issues for devices connected to the PIX failover pair in the unlikely event that both firewalls in a failover pair fail at the same time and only the standby unit remains operational.

150 Chapter 9: Cisco PIX Firewall Failover
Configuring Failover
Now for the fun stuff! To configure failover, you need to become familiar with a few key commands. Table 9-1 shows the commands used to configure and verify failover.
Table 9-1 |
Configuring and Verifying Failover |
|
|
|
|
|
Command |
Description |
|
|
|
|
failover |
The failover command without an argument enables |
|
|
the failover function on the PIX. Use this command |
|
|
after you connect the failover cable between the |
|
|
primary and secondary unit. Use the no failover |
|
|
command to disable the failover feature. |
|
|
|
|
failover active |
Makes the PIX unit it is issued on the active unit. This |
|
|
command is usually used to make the primary unit |
|
|
active again after repairs have been made to it. |
|
|
|
|
failover ip address if_name ip_address |
Issued on the primary unit to configure the standby unit’s |
|
|
IP address. This is the IP address that the standby |
|
|
interface uses to communicate with the active unit. |
|
|
Therefore, it has the same subnet as the system address*. |
|
|
The if_name argument is for the interface name, such |
|
|
as outside. The ip_address is the interface name’s IP |
|
|
address. |
|
|
|
|
failover link stateful_if_name |
Enables stateful failover on the specified interface. |
|
|
|
|
show failover |
This popular command displays the status of the |
|
|
failover configuration. |
|
|
|
|
failover poll seconds |
Specifies how long failover waits before sending |
|
|
special hello packets between the primary and |
|
|
secondary units. The default is 15 seconds. The |
|
|
minimum is 3 seconds, and the maximum is 15 |
|
|
seconds. |
|
|
|
|
failover reset |
Can be entered from either unit (active or standby), |
|
|
preferably the active unit. This forces the units back to |
|
|
their state and is used after repairs have been made. |
|
|
|
|
write standby |
Enter the write standby command from the active |
|
|
unit to synchronize the current configuration to the |
|
|
Flash memory on the standby unit. |
|
|
|
|
failover lan interface interface_name |
Configures LAN-based failover. |
|
|
|
|
failover lan unit primary | secondary |
Specifies the primary or secondary PIX to use for |
|
|
LAN-based failover. |
|
|
|
|
failover replicate http |
Allows the stateful replication of HTTP sessions in a |
|
|
stateful failover environment. |
|
|
|
*The system address is the same address as the active unit IP address. When the active unit fails, the standby assumes the system address so that there is no need for the network devices to be reconfigured for a different firewall address.
Configuring Failover 151
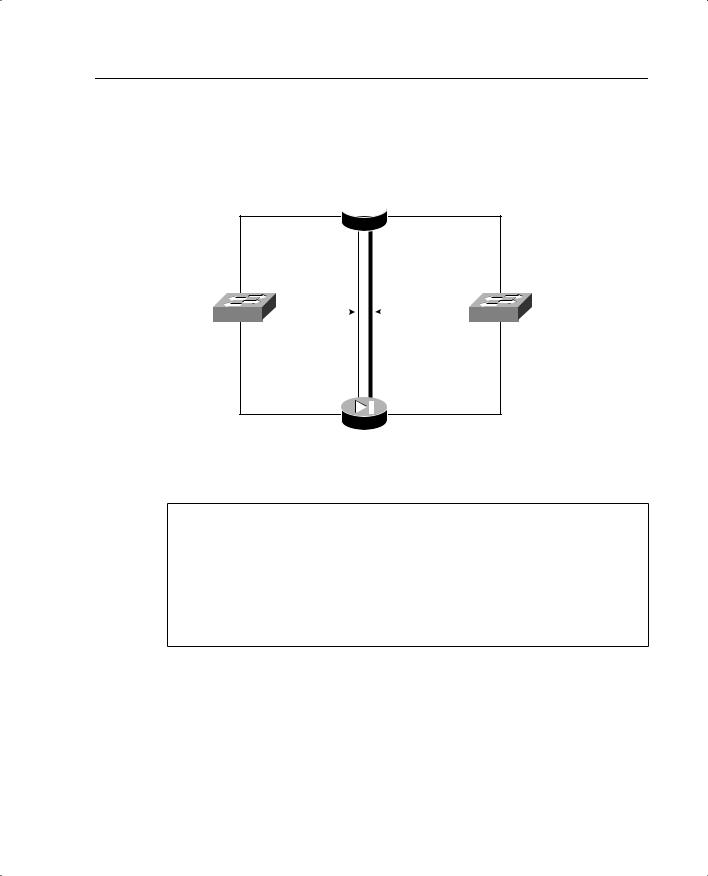
Figure 9-1 shows two PIX units in a failover configuration. Example 9-1 shows the steps required to configure failover and stateful failover on the PIX Firewall.
Figure 9-1 Network Diagram of Failover Configuration
Primary_PIX 10.10.10.1  192.168.1.1
192.168.1.1
172.16.1.1
Inside |
Stateful |
|
|
|
Serial |
Outside |
Network |
|
|
|
Failover |
Network |
|
Connection |
|
|||||
|
|
Cable |
|
|||
|
|
|
|
|
|
|
172.16.1.2
10.10.10.2  192.168.1.2 Secondary_PIX
192.168.1.2 Secondary_PIX
Example 9-1 Sample Configuration for primary-PIX
hostname primary-PIX
nameif ethernet0 outside security0 nameif ethernet1 inside security100 nameif ethernet2 failover security10 interface ethernet0 10baset interface ethernet1 10baset interface ethernet2 100full
ip address outside 192.168.1.1 255.255.255.224 ip address inside 10.10.10.1 255.255.255.0
global (outside) 1 192.168.1.15-192.168.1.40 netmask 255.255.255.224 nat (inside) 1 0.0.0.0 0.0.0.0 0 0
Before beginning the failover configuration, be sure that you connect the failover cable to the units correctly. Also be sure that the standby unit is not powered on.
Step 1 Enable failover:
Primary-pix (config)# failover
Step 2 Assign interface ethernet2 a name for stateful failover:
Primary-pix (config)# nameif ethernet2 failover

152 Chapter 9: Cisco PIX Firewall Failover
Step 3 Set the interface speed:
Primary-pix (config)# interface ethernet2 100full
Step 4 Assign an IP address to the interface:
Primary-pix (config)# ip address failover 172.16.1.1 255.255.255.240
Step 5 Verify your failover configuration:
Primary-pix (config)# show failover
Step 6 Configure the secondary unit IP address from the primary unit by the failover ip address command. Add the failover ip address command for all interfaces, including the one for the dedicated failover interface and any unused interfaces:
Primary-pix (config)# failover ip address outside 192.168.1.2
Primary-pix (config)# failover ip address inside 10.10.10.2
Primary-pix (config)# failover ip address failover 172.16.1.2
Step 7 Save your configuration:
Primary-pix (config)# write memory
Step 8 Use the show ip address command to view the addresses you specified:
Primary-pix (config)# show ip address
System IP Addresses:
ip |
address outside |
192.168.1.1 |
255.255.255.0 |
ip |
address inside 10.10.10.1 255.255.255.0 |
||
ip |
address failover 172.16.1.1 |
255.255.255.240 |
|
Current |
IP Addresses: |
|
|
ip |
address outside |
192.168.1.1 |
255.255.255.0 |
ip |
address inside 10.10.10.1 255.255.255.0 |
||
ip |
addressfailover |
172.16.1.2 255.255.255.240 |
|
The Current IP Addresses are the same as the System IP Addresses on the failover active unit. When the primary unit fails, the Current IP Addresses become those of the standby unit.
Step 9 Enable stateful failover:
Primary-pix (config)# failover link failover
Step 10 Power up the secondary unit. At this point, the primary unit starts replicating the configuration to the secondary.
Step 11 Verify your failover configuration:
Primary-pix (config)# show failover
Failover On
Cable status: Normal
Reconnect timeout 0:00:00

Configuring Failover 153
Poll frequency 15 seconds
This host: primary - Active
Active time: 240 (sec)
Interface st_failover (172.16.1.1): Normal
Interface outside (192.168.1.1): Normal
Interface inside (10.10.10.1): Normal
Other host: secondary - Standby
Active time: 0 (sec)
Interface st_failover (172.16.1.1): Normal
Interface outside (192.168.1.1): Normal
Interface inside (10.10.10.1): Normal
Stateful Failover Logical Update Statistics |
|
|
||
Link : failover |
|
|
|
|
Stateful Obj |
xmit |
xerr |
rcv |
rerr |
General |
2701 |
0 |
0 |
0 |
sys cmd |
2653 |
0 |
0 |
0 |
up time |
0 |
0 |
0 |
0 |
xlate |
0 |
0 |
0 |
0 |
tcp conn |
0 |
0 |
0 |
0 |
udp conn |
0 |
0 |
0 |
0 |
ARP tbl |
0 |
0 |
0 |
0 |
RIP Tbl |
0 |
0 |
0 |
0 |
Logical Update Queue Information |
|
|||
|
|
Cur |
Max |
Total |
Recv |
Q: |
0 |
0 |
0 |
Xmit |
Q: |
0 |
0 |
2701 |
The first part of the show failover command output describes the cable status. Each interface on the PIX unit has one of the following values:
—Normal—The active unit is working, and the standby unit is ready.
—Waiting—Monitoring of the other unit’s network interfaces has not yet started.
—Failed—The PIX Firewall has failed.
—Shutdown—The interface is turned off.
The second part of the show failover command describes the status of the stateful failover configuration. Each row is for a particular static object count:
—General—The sum of all stateful objects.
—Sys cmd—Refers to logical update system commands, such as login and stay alive.

154Chapter 9: Cisco PIX Firewall Failover
—Up time—The value for PIX up time that the active PIX unit passes on to the standby unit.
—Xlate—The PIX translation information.
—Tcp conn—The PIX dynamic TCP connection information.
—Udp conn—The PIX dynamic UDP connection information.
—ARP tbl—The PIX dynamic ARP table information.
—RIF tbl—The dynamic router table information.
The Stateful Obj has these values:
—Xmit—Indicates the number of packets transmitted.
—Xerr—Indicates the number of transmit errors.
—Rcv—Indicates the number of packets received.
—rerr—Indicates the number of receive errors.
Step 12 Enter the write standby command from the active unit to synchronize the current configuration to the Flash memory on the standby unit.
