
- •CCIE Security Written Exam Blueprint
- •General Networking Topics
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Networking Basics—The OSI Reference Model
- •Ethernet Overview
- •Internet Protocol
- •Variable-Length Subnet Masks
- •Classless Interdomain Routing
- •Transmission Control Protocol
- •TCP Services
- •Routing Protocols
- •ISDN
- •IP Multicast
- •Asynchronous Communications and Access Devices
- •Foundation Summary
- •Requirements for FastEther Channel
- •Scenario
- •Scenario 2-1: Routing IP on Cisco Routers
- •Scenario Answers
- •Scenario 2-1 Answers: Routing IP on Cisco Routers
- •Application Protocols
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Domain Name System
- •Trivial File Transfer Protocol
- •File Transfer Protocol
- •Hypertext Transfer Protocol
- •Secure Socket Layer
- •Simple Network Management Protocol
- •Simple Mail Transfer Protocol
- •Network Time Protocol
- •Secure Shell
- •Foundation Summary
- •Scenario
- •Scenario Answers
- •Scenario 3-1 Solutions
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Cisco Hardware
- •show and debug Commands
- •Password Recovery
- •Basic Security on Cisco Routers
- •IP Access Lists
- •Foundation Summary
- •Scenario
- •Scenario Answers
- •Security Protocols
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Authentication, Authorization, and Accounting (AAA)
- •Remote Authentication Dial-In User Service (RADIUS)
- •Kerberos
- •Virtual Private Dial-Up Networks (VPDN)
- •Encryption Technology Overview
- •Internet Key Exchange (IKE)
- •Foundation Summary
- •Scenario
- •Scenario 5-1: Configuring Cisco Routers for IPSec
- •Scenario Answers
- •Scenario 5-1 Solutions
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •UNIX
- •Microsoft NT Systems
- •Common Windows DOS Commands
- •Cisco Secure for Windows and UNIX
- •Cisco Secure Policy Manager
- •Cisco Secure Intrusion Detection System and Cisco Secure Scanner
- •Cisco Security Wheel
- •Foundation Summary
- •Scenarios
- •Scenario 6-1: NT File Permissions
- •Scenario 6-2: UNIX File Permissions
- •Scenario Answers
- •Scenario 6-1 Solution
- •Scenario 6-2 Solution
- •Security Technologies
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Advanced Security Concepts
- •Cisco Private Internet Exchange (PIX)
- •Cisco IOS Firewall Security Feature Set
- •Public Key Infrastructure
- •Virtual Private Networks
- •Foundation Summary
- •Scenario
- •Scenario Answer
- •Scenario 7-1 Solution
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Network Security Policies
- •Standards Bodies and Incident Response Teams
- •Vulnerabilities, Attacks, and Common Exploits
- •Intrusion Detection System
- •Protecting Cisco IOS from Intrusion
- •Foundation Summary
- •Scenario
- •Scenario 8-1: Defining IOS Commands to View DoS Attacks in Real Time
- •Scenario Answer
- •Scenario 8-1 Solution

ISDN 79
5Then prefer the route with the shortest AS Path.
6If this is equal, prefer the route with origin set to originated (via BGP); IGP is preferred to EGP and then incomplete.
7If the origin codes are the same, prefer the route with the lowest MED.
8If the MED is the same, prefer EBGP over IBGP.
9Then prefer the path that is the closest.
10Finally, if all else is equal, prefer the path with the lowest BGP router ID.
Configuring BGP
To start the BGP process on a Cisco router requires the following command:
router bgp autonomous-system-number
To define networks to be advertised, apply the following command:
network network-number mask network-mask
You must be aware that the network command is not used the same way you apply networks in OSPF or EIGRP. With BGP, the network command advertises networks that are originated from the router and should be advertised via BGP. For more Cisco IOS examples of BGP, please visit Chapter 9, “CCIE Security Self-Study Lab.”
To identify peer routers, apply the following command:
neighbor {ip-address | peer-group name} remote-as autonomous-system-number
NOTE Route redistribution allows routing information discovered through one routing protocol to be distributed in the update messages of another routing protocol. Whenever redistribution is configured on Cisco routers, the routing metric must also be converted. For example, with redistribution from a RIP domain into OSPF, the RIP network inserted into OSPF requires an OSPF cost metric.
ISDN
Integrated Services Digital Network (ISDN) is a digital service that enables network users to send and receive data, voice, and video transmissions over a network. ISDN offers a variety of link speeds, ranging from 64 kbps to 2.048 Mbps. Many smalland medium-sized companies find that ISDN is a viable network solution.
80 Chapter 2: General Networking Topics
Basic Rate and Primary Rate Interfaces
ISDN can be supplied by a carrier in two main forms: Basic Rate Interface (BRI) and Primary Rate Interface (PRI). An ISDN BRI consists of two 64-kbps services (B channels) and one 16-kbps signaling channel (D channel). An ISDN PRI consists of 23 B or 30 B channels, depending on the country. In North America and Japan, a PRI service consists of 23 B channels. In Europe and Australia, a PRI service consists of 30 B channels. A signaling channel (or D channel) is used in a PRI service and is a dedicated 64-kbps channel. The B channel sends data and the D channel primarily controls signaling.
NOTE The effective throughput of a PRI service with 23 channels is 1.472 Mbps (23 × 64 kbps). With 30 B channels, the effective throughput is 1.920 Mbps (30 × 64 kbps). The International Telecommunications Union (ITU) defines the standards for ISDN. The specified standard is ITU-T Q.921.
ISDN Framing and Frame Format
The ISDN physical layer provides the ability to send outbound traffic and receive inbound traffic by transmitting binary bits over the physical media. The ISDN data link layer provides signaling, which ensures that data is sent and received correctly. The signaling protocol used in ISDN is called the Link Access Procedure on the D channel (LAPD).
ISDN Layer 2 Protocols
ISDN can use a number of Layer 2 encapsulation types. Point-to-Point Protocol (PPP) and high-level data link control (HDLC) are the only methods tested in the qualification exam.
NOTE X.25 is not tested in the CCIE Security written exam.
HDLC
High-level data link control is a WAN protocol encapsulation method that allows point-to-point connections between two remote sites. Typically, HDLC is used in a leased-line setup. HDLC is a connectionless protocol that relies on upper layers to recover any frames that have encountered errors across a WAN link. HDLC is the default encapsulation on Cisco serial interfaces.
Cisco routers use HDLC encapsulation, which is proprietary. Cisco added an address field in the HDLC frame, which is not present in the HDLC standard. This field is used by Cisco devices to indicate the type of payload (protocol). Cisco routers use the address field in an
ISDN 81
HDLC frame to indicate a payload type, but other routers or manufacturers that implement the HDLC standard do not use the address field. HDLC cannot be used to connect a Cisco router with another vendor.
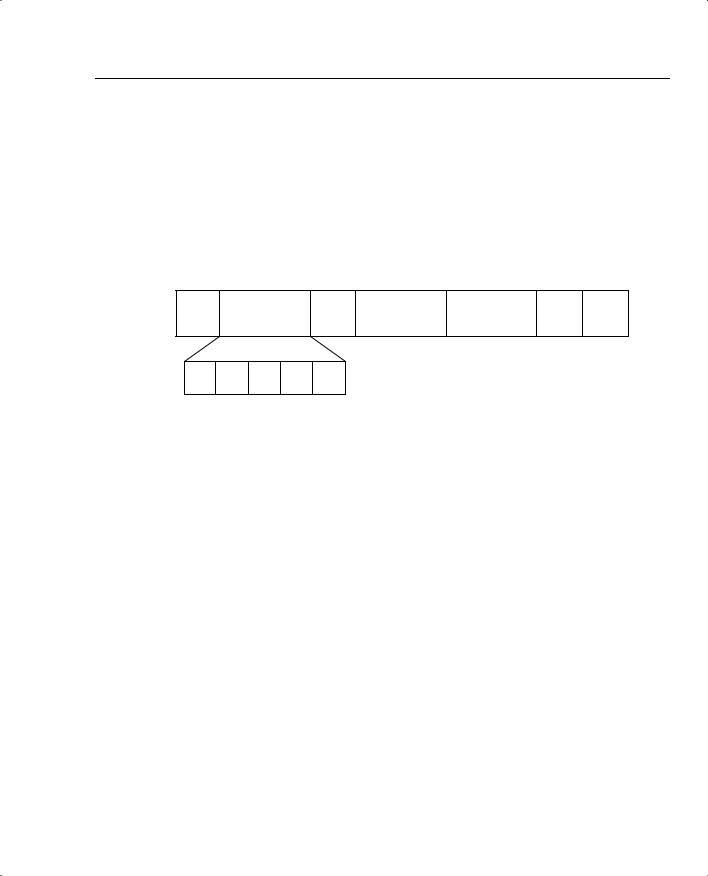
Figure 2-18 displays the HDLC frame format, which shares a common format with the PPP frame format discussed in the next section.
Figure 2-18 HDLC Frame Format
Field Length |
|
|
|
|
|
|
in Bytes |
|
|
|
|
|
|
1 |
2 |
1 |
2 |
Variable |
1 |
1 |
Flag |
Address |
Control |
Protocol |
Data |
FCS |
Flag |
SAPI C/R EA TEI EA
SAPI - Service Access Point Identifier
C/R - Command/Response
EA - Extended Address
TEI - Terminal Endpoint Identifier (All 1s indicate a broadcast.)
Point-to-Point Protocol (PPP)
PPP was designed to transport user information between two WAN devices (also referred to as point-to-point links). PPP was designed as an improvement over Serial Line Internet Protocol (SLIP). When PPP encapsulation is configured on a Cisco WAN interface, the network administrator can carry protocols such as IP and IPX, as well as many others. Cisco routers support PPP over asynchronous lines, High-Speed Serial Interfaces (HSSIs), ISDN lines, and synchronous serial ports. PPP has the added function of allowing authentication to take place before any end user data is sent across the link.
The following three phases occur in any PPP session:
•Link establishment—Link Control Protocol (LCP) packets are sent to configure and test the link.
•Authentication (optional)—After the link is established, authentication can ensure that link security is maintained.
•Network layers—In this phase, Network Control Protocol (NCP) packets determine which protocols are used across the PPP link. An interesting aspect of PPP is that each protocol (IP, IPX, and so on) supported in this phase is documented in a separate RFC that discusses how it operates over PPP.

82 Chapter 2: General Networking Topics
Figure 2-19 displays the PPP frame format, which is similar to the HDLC frame format in Figure 2-18.
Figure 2-19 PPP Frame Format
Field Length |
|
|
|
|
|
|
|
|
|
|
|
in Bytes |
|
|
|
|
|
|
|
|
|
|
|
1 |
1 |
|
1 |
1 |
Variable |
2 or 4 |
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
Flag |
|
Address |
Control |
Protocol |
Data |
FCS |
||||
|
01111110 |
11111111 |
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Address |
|
Identifies |
|
Frame |
||||
|
|
not used. |
|
Payload |
|
Check Sequence |
|||||
Set to all 1s.
LCP
LPC is used to establish, configure, and test the link between two devices, such as Cisco routers. LCP provides the necessary negotiations between end devices to activate the link. After the link is activated, but while no data is yet flowing, the next phase(s) of the PPP session can take place—authentication (if configured) and the NCP.
Authentication
PPP supports authentication through Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP), with CHAP providing a more secure method of authentication. CHAP passwords are encrypted and safe from intruders because they are never actually transmitted on the wire. This technique, known as shared secrets, means that both devices know the secret (password), but they never talk about it directly. PAP passwords are sent in clear text; they are clearly visible on the wire.
NCP
PPP uses NCP packets to allow multiple network layer protocol types to transfer across WANs from point to point. IP Control Program (IPCP) allows IP connectivity, and IPXCP allows IPX connectivity.
Cisco IOS ISDN Commands
Cisco routers support ISDN. The commands most often used to enable data and voice communications over ISDN are listed in Table 2-15.
