
- •CCIE Security Written Exam Blueprint
- •General Networking Topics
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Networking Basics—The OSI Reference Model
- •Ethernet Overview
- •Internet Protocol
- •Variable-Length Subnet Masks
- •Classless Interdomain Routing
- •Transmission Control Protocol
- •TCP Services
- •Routing Protocols
- •ISDN
- •IP Multicast
- •Asynchronous Communications and Access Devices
- •Foundation Summary
- •Requirements for FastEther Channel
- •Scenario
- •Scenario 2-1: Routing IP on Cisco Routers
- •Scenario Answers
- •Scenario 2-1 Answers: Routing IP on Cisco Routers
- •Application Protocols
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Domain Name System
- •Trivial File Transfer Protocol
- •File Transfer Protocol
- •Hypertext Transfer Protocol
- •Secure Socket Layer
- •Simple Network Management Protocol
- •Simple Mail Transfer Protocol
- •Network Time Protocol
- •Secure Shell
- •Foundation Summary
- •Scenario
- •Scenario Answers
- •Scenario 3-1 Solutions
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Cisco Hardware
- •show and debug Commands
- •Password Recovery
- •Basic Security on Cisco Routers
- •IP Access Lists
- •Foundation Summary
- •Scenario
- •Scenario Answers
- •Security Protocols
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Authentication, Authorization, and Accounting (AAA)
- •Remote Authentication Dial-In User Service (RADIUS)
- •Kerberos
- •Virtual Private Dial-Up Networks (VPDN)
- •Encryption Technology Overview
- •Internet Key Exchange (IKE)
- •Foundation Summary
- •Scenario
- •Scenario 5-1: Configuring Cisco Routers for IPSec
- •Scenario Answers
- •Scenario 5-1 Solutions
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •UNIX
- •Microsoft NT Systems
- •Common Windows DOS Commands
- •Cisco Secure for Windows and UNIX
- •Cisco Secure Policy Manager
- •Cisco Secure Intrusion Detection System and Cisco Secure Scanner
- •Cisco Security Wheel
- •Foundation Summary
- •Scenarios
- •Scenario 6-1: NT File Permissions
- •Scenario 6-2: UNIX File Permissions
- •Scenario Answers
- •Scenario 6-1 Solution
- •Scenario 6-2 Solution
- •Security Technologies
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Advanced Security Concepts
- •Cisco Private Internet Exchange (PIX)
- •Cisco IOS Firewall Security Feature Set
- •Public Key Infrastructure
- •Virtual Private Networks
- •Foundation Summary
- •Scenario
- •Scenario Answer
- •Scenario 7-1 Solution
- •“Do I Know This Already?” Quiz
- •Foundation Topics
- •Network Security Policies
- •Standards Bodies and Incident Response Teams
- •Vulnerabilities, Attacks, and Common Exploits
- •Intrusion Detection System
- •Protecting Cisco IOS from Intrusion
- •Foundation Summary
- •Scenario
- •Scenario 8-1: Defining IOS Commands to View DoS Attacks in Real Time
- •Scenario Answer
- •Scenario 8-1 Solution

Simple Mail Transfer Protocol 127
The following example disables all versions of SNMP:
R1(config)# no snmp-server
The following example enables the router to send all traps to the host, host.cisco.com, using the community string public:
R1(config)# snmp-server enable traps
R1(config)# snmp-server host host.cisco.com public
In the following example, the BGP traps are enabled for all hosts, but only the ISDN traps are enabled to be sent to an actual host named simon:
R1(config)# snmp-server enable traps bgp
R1(config)# snmp-server host simon public isdn
The following example enables the router to send all inform requests to the host test.cisco.com using the community string publiC:
R1(config)# snmp-server enable traps
R1(config)# snmp-server host test.cisco.com informs publiC
Simple Mail Transfer Protocol
|
The Simple Mail Transfer Protocol (SMTP) mechanism is used for providing e-mail services |
|
to IP devices over the Internet. SMTP is defined in RFC 821. Typically, two mail servers will |
|
talk SMTP to exchange mails. After the mails are exchanged, the users can read/retrieve their |
|
mail from the mail server. This can be done using any mail client, such as Pine, Eudore, Outlook, |
|
and so on, which use different protocols, such as Post office protocol or POP3, to connect to the |
|
server. SMTP uses well-known ports TCP port 25 and UDP port 25. |
|
A process or daemon running on a server will use SMTP to send mail to clients. A program |
|
called Sendmail is a common tool used for SMTP mail transfer. Recently, a new release of |
|
SMTP, called Enhanced SMTP (ESMTP), was developed. You are not required to know this |
|
protocol for the written exam. |
|
|
NOTE |
The client and SMTP server send various commands when communicating. The most common |
|
command is HELO check. |
|
The HELO Check command introduces the calling machine to the receive machine; the client |
|
will advertise the mail server its host name. There are numerous other commands. A great resource |
|
if you are interested in further details on the Sendmail application is the book “Sendmail,” by |
|
Bryan Costales and Eric Allman (O’Reilly and Associates, ISBN 1-56592-839-3). |
|
To test if a remote host’s SNMP mail is operational and active, you can use Telnet with the |
|
defined HELO command. |
|
A summary of other useful SMTP commands is presented for your reference in case you are |
|
questioned on these commands during the exam: |
|
HELLO (HELO)—Identifies the sender. |
128 Chapter 3: Application Protocols
MAIL (MAIL)—Initiates a mail transaction in which the mail data is delivered to mailboxes.
RECIPIENT (RCPT)—Identifies an individual recipient of the mail data; multiple use of the command is needed for multiple users.
DATA (DATA)—The lines following the command are the mail data in ASCII character codes.
SEND (SEND)—Initiates a mail transaction in which the mail data is delivered to one or more terminals.
SEND OR MAIL (SOML)—Initiates a mail transaction in which the mail data is delivered to one or more terminals or mailboxes.
SEND AND MAIL (SAML)—Initiates a mail transaction in which the mail data is delivered to one or more terminals and mailboxes.
RESET (RSET)—The current mail transaction is to be aborted. Any stored sender, recipients, and mail data must be discarded, and all buffers and state tables cleared. The receiver must send an OK reply.
VERIFY (VRFY)—This is to verify if a user exists; a fully specified mailbox and name are returned.
NOOP (NOOP)—Specifies no action other than that the receiver sent an OK reply.
QUIT (QUIT)—The receiver must send an OK reply and then close the transmission channel.
Network Time Protocol
Network Time Protocol (NTP) is used for accurate time keeping and can reference atomic clocks that are present on the Internet, for example. NTP is capable of synchronizing clocks within milliseconds and is a useful protocol when reporting error logs (for instance, from Cisco routers).
For NTP, the defined ports are UDP port 123 and TCP 123. NTP can support a connectionorientated server (TCP guarantees delivery) or connectionless (UDP for non-critical applications).
An NTP network usually gets its time from an authoritative time source, such as a radio clock or an atomic clock attached to a time server. NTP then distributes this time across the network. NTP is extremely efficient; no more than one packet per minute is necessary to synchronize two machines to within a millisecond of one another.
NOTE NTP uses the concept of a stratum to describe how many NTP hops away a machine is from an authoritative time source. A stratum 1 time server has a radio or atomic clock directly attached; a stratum 2 time server receives its time via NTP from a stratum 1 time server, and so on. Cisco routers cannot support stratum 1 (in other words, you cannot connect a Cisco router to an atomic clock source) and need to derive an atomic clock source from the Internet. NTP can also authenticate sessions.
Network Time Protocol 129
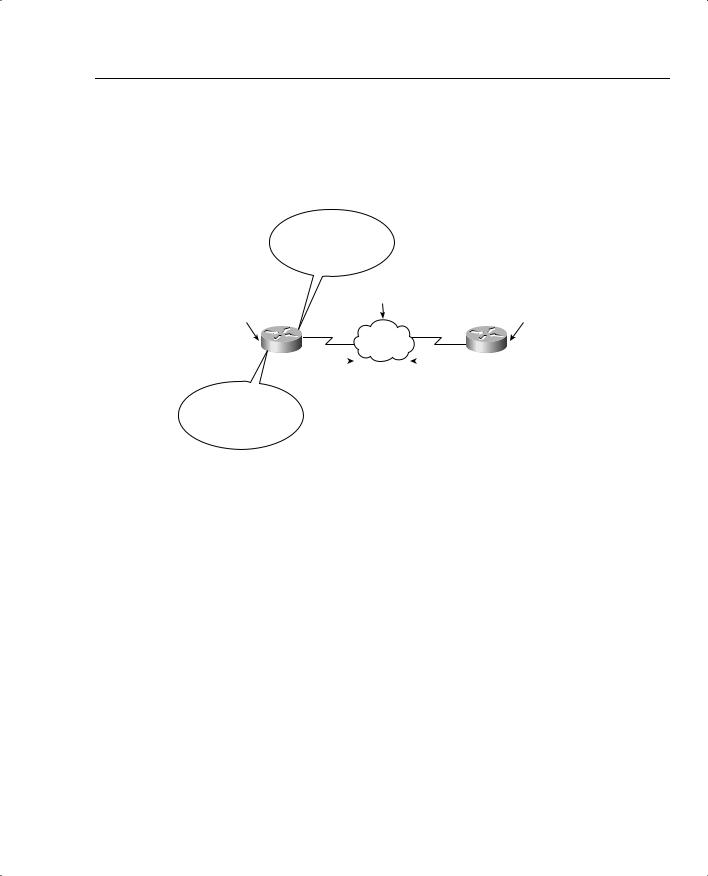
Figure 3-7 displays a simple two-router network where Router R1 will be configured to supply a clock source to the Router R2. In this example, you will configure authentication and ensure that the NTP peer between the two routers is secure.
Figure 3-7 NTP Sample Configuration
My clock is set to August 9, 2002, time 10:47:48 a.m.
Ethernet0/0 |
|
131.108.3.0/30 |
|
|
Ethernet0/0 |
|||||
NTP |
|
|
Frame Relay |
|
|
NTP |
||||
172.108.1.1/24 |
|
|
|
|
|
172.108.2.1/24 |
||||
Server |
|
|
|
|
|
Client |
||||
|
|
Send |
Receive |
|
|
|||||
|
|
R1 |
R2 |
|
|
|||||
|
|
|
|
|||||||
|
|
NTP |
|
|
|
NTP |
|
|
||
|
|
|
|
|||||||
|
|
|
Serial0/0.1 |
Serial0/0.2 |
|
|
|
|||
I have NTP atomic |
|
|
|
|
|
|
|
|
||
clock source; my stratum |
|
|
|
|
|
|
|
|
||
|
value is 2. |
|
|
|
|
|
|
|
|
|
The following steps are required when enabling NTP on a Cisco router:
1 Define the time zone with the following command:
clock timezone zone hours [minutes]
2Configure the master NTP router (this router will supply a clock to other routers) with the following command:
ntp master [stratum value]
The stratum value is 1 to 15, with 1 representing the best clock source.
3To configure a remote NTP peer to a Cisco router with a better stratum value, use the following IOS command:
ntp peer ip-address [version number] [key keyid] [source interface] [prefer]
Table 3-4 displays the required parameters for the ntp peer command.
4 To define NTP to authenticate the NTP session, use the following IOS commands:
ntp trusted-key key-number
The key-number is the authentication key to be trusted.
ntp authentication-key number md5 value
130 Chapter 3: Application Protocols
Table 3-4 |
ntp peer Command Defined |
|
|
|
|
|
Syntax |
Description |
|
|
|
|
ip-address |
IP address of the peer providing, or being provided, the clock |
|
|
|
|
version |
(Optional) Defines the Network Time Protocol (NTP) version number |
|
|
|
|
number |
(Optional) NTP version number (1 to 3) |
|
|
|
|
key |
(Optional) Defines the authentication key |
|
|
|
|
keyid |
(Optional) Authentication key to use when sending packets to this peer |
|
|
|
|
source |
(Optional) Names the interface |
|
|
|
|
interface |
(Optional) Name of the interface from which to pick the IP source address |
|
|
|
|
prefer |
(Optional) Makes this peer the preferred peer to provide synchronization |
|
|
|
To ensure that R1 sends R2 a clock source via NTP, R1 must be configured to send NTP traffic over the Frame Relay cloud with the command ntp broadcast. To specify that a specific interface should send NTP broadcast packets, use the ntp broadcast interface configuration command. Similarly, R2 must receive NTP traffic and is considered an NTP client with the IOS command ntp broadcast client.
R2’s Serial 0/0 interface is configured with the command ntp broadcast client.
Example 3-8 configures Router R1 in Figure 3-7 to supply a clock source to Router R2.
Example 3-8 NTP Configuration on R1
clock set 10:20:00 9 August 2002 clock timezone UTC 10 !Interface configuration interface serial0/0
ntp broadcast
!Global configuration
ntp authentication-key 1 md5 121A061E17 7 ntp authenticate
ntp trusted-key 1 ntp master 2
ntp peer 131.108.2.1 key 1
Notice that the router is set to the correct time first with the IOS command clock set.
The router is configured for the UTC time zone and 10 hours behind UTC time. The authentication key is set to 1.
Example 3-9 configures R2 to get the clock from R1 using the same MD5 password (set to ccie) from Example 3-8.

Network Time Protocol 131
Example 3-9 NTP Configuration on R2
interface serial0/0 ntp broadcast client !Global configuration
ntp authentication-key 1 md5 ccie ntp authenticate
ntp trusted-key 1 ntp trusted-key
ntp peer 131.108.1.1 key 1
Example 3-10 displays the two clocks on Routers R1 and R2 confirming that R1 is sending R2 the correct time via NTP.
Example 3-10 show clock on R1 and R2
R1#show clock
10:47:48.508 UTC Fri Aug 9 2002
R2#show clock
10:47:48.508 UTC Fri Aug 9 2002
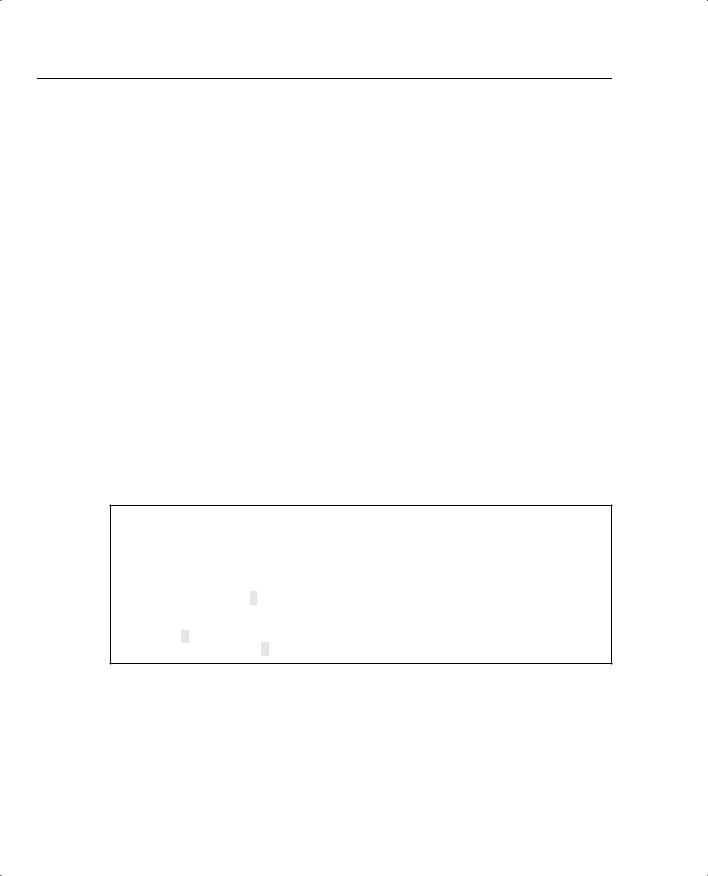
Example 3-11 confirms that NTP is authenticated (the remote stratum value is 2) by viewing the output of the IOS command show ntp associations detail.
Example 3-11 show ntp associations detail Command on R2
R2# show ntp associations detail |
|
|
|
|
|
|
|
|
|
|
|
||||
|
|
|
, selected, sane, |
valid, |
|
|
|
|
|||||||
131.108.1.1 configured, authenticated |
stratum 2 |
|
|
||||||||||||
|
|
ref ID .LOCL., time C0FD8D45.0B1C72E0 |
(10:37:25.043 UTC Fri Aug 9 2002) |
|
|
||||||||||
our mode active, peer mode passive, our poll intvl 64, |
peer poll intvl 64 |
||||||||||||||
root delay 0.00 msec, root disp 0.03, reach 1, sync dist 15878.372 |
|
|
|||||||||||||
delay 6.67 msec, offset |
297909193935.7106 msec, dispersion 15875.02 |
|
|
||||||||||||
precision 2**16, version 3 |
|
|
|
|
|
|
|
|
|
|
|
||||
org time C0FD8D45.BA55E231 (10:37:25.727 UTC Fri Aug |
9 |
2002) |
|
|
|
|
|||||||||
rcv time AF3BD17B.CBA5DDF0 (10:04:11.795 UTC Mon Mar |
1 |
1993) |
|
|
|
|
|||||||||
xmt time AF3BD17B.C9CB2BA2 (10:04:11.788 UTC Mon Mar |
1 |
1993) |
|
|
|
|
|||||||||
filtdelay = |
6.67 |
0.00 |
0.00 |
0.00 |
0.00 |
|
0.00 |
0.00 |
0.00 |
||||||
filtoffset = 2979091 |
0.00 |
0.00 |
0.00 |
0.00 |
|
0.00 |
0.00 |
0.00 |
|||||||
filterror = |
0.02 16000.0 16000.0 |
16000.0 |
16000.0 |
16000.0 16000.0 16000.0 |
|||||||||||
|
|
, sane, valid, |
|
|
|||||||||||
131.108.255.1 dynamic, authenticated, our_master |
stratum 2 |
||||||||||||||
|
ref ID .LOCL., time C0FD8D05.0AE0774C (10:36:21.042 |
UTC Fri Aug |
9 2002) |
|
|
||||||||||
our mode passive, peer mode active, our poll intvl 64, |
peer poll intvl 64 |
||||||||||||||
root delay 0.00 msec, root disp 0.03, reach 2, sync dist 1.007 |
|
|
|
|
|||||||||||
delay 0.00 msec, offset |
0.0000 msec, dispersion 16000.00 |
|
|
|
|
||||||||||
precision 2**16, version 3 |
|
|
|
|
|
|
|
|
|
|
|
||||
org time C0FD8D43.0B54AAFA (10:37:23.044 UTC Fri Aug |
9 |
2002) |
|
|
|
|
|||||||||
rcv time AF3BD179.1C9F231D (10:04:09.111 UTC Mon Mar |
1 |
1993) |
|
|
|
|
|||||||||
xmt time AF3BD186.C9CB3361 (10:04:22.788 UTC Mon Mar |
1 |
1993) |
|
|
|
|
|||||||||
filtdelay = |
0.00 |
0.00 |
0.00 |
0.00 |
0.00 |
|
0.00 |
0.00 |
0.00 |
||||||
filtoffset = |
0.00 |
0.00 |
0.00 |
0.00 |
0.00 |
|
0.00 |
0.00 |
0.00 |
||||||
filterror = |
16000.0 16000.0 16000.0 |
16000.0 16000.0 |
16000.0 16000.0 16000.0 |
||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
