
- •About the Author
- •Credits
- •How This Book Is Organized
- •Part I: Linux Basics
- •Part II: Installation
- •Part III: Configuration
- •Part IV: Administration
- •Part V: Maintaining the Linux System
- •How Each Chapter Is Structured
- •How to Use This Book
- •Conventions Used in This Book
- •What is Linux?
- •The origin of UNIX
- •Who started Linux?
- •Understanding Open Source
- •Understanding Closed Source
- •Understanding Artistic License
- •Is Freeware really free?
- •Is Shareware never free?
- •A comparison and contrast of licensing methods
- •The Growth of Linux
- •Linux on a Personal Computer
- •Graphical installation
- •Hardware detection
- •Graphical user interface
- •Linux limitations on the PC
- •Linux succeeds on the PC
- •Linux on workstations
- •Linux on servers
- •Summary
- •Assessment Questions
- •Scenarios
- •Answers to Chapter Questions
- •Assessment Questions
- •Scenarios
- •Linux Kernel
- •Kernel versions
- •Kernel availability
- •Linux Distributions
- •Beehive
- •BlueCat
- •Caldera OpenLinux
- •Debian
- •Corel
- •DragonLinux
- •Elfstone
- •Gentoo
- •Hard Hat Linux
- •KRUD
- •LinuxPPC
- •Mandrake
- •Phat Linux
- •Slackware
- •StormLinux
- •SuSE
- •TurboLinux
- •Yellow Dog Linux
- •Mini and Specialty Distributions
- •Astaro
- •KYZO
- •FlightLinux
- •NetMAX
- •Packages and Packaging Solutions
- •Red Hat Package Manager
- •Debian Package Management System
- •Tarball
- •Linux Resources
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Assessment Questions
- •Scenarios
- •Linux In the Real World
- •Word Processing
- •Spreadsheets and databases
- •Web browsing
- •File transfer
- •More, more, and more applications
- •The Server and DNS
- •A Linux Web server
- •Linux e-mail server
- •File servers
- •Proxy, news, and search servers
- •FTP servers
- •Firewalls
- •Determining Linux Roles and Services
- •Comparing Linux with other operating systems
- •Hardware compatibility
- •Summary
- •Assessment Questions
- •Scenarios
- •Answers to Chapter Questions
- •Assessment Questions
- •Scenarios
- •Installing Linux
- •Final Preparations for Installation
- •Verification
- •Package selection
- •Final hardware verification
- •Pre-installation partitioning planning
- •Installing Linux
- •Text or GUI installation
- •Basic setup of Linux
- •Selecting the machine type
- •Partitioning the hard disk drive
- •Installing a boot manager
- •Creating the Boot Diskette
- •Networking
- •Additional installation information
- •Accounts and passwords
- •Additional packages to install
- •GUI installation
- •Obtaining video card information
- •Configuring the X windows system
- •Selecting the windows manager or desktop environment
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Answers to Assessment Questions
- •Scenarios
- •Alternative to the GUI Installation
- •Command Line installation
- •Install the Linux system
- •Network installations of Linux
- •Review of a Linux Installation
- •Installation media
- •Initial selections
- •Installation type or class
- •Disk partitioning and formatting
- •Installing LILO
- •Network configuration
- •User accounts
- •Authentication methods
- •Package selection and installation
- •A Dual-Boot Installation of Linux
- •Linux with Microsoft Windows
- •Linux with Microsoft Windows NT and 2000
- •Linux and Solaris
- •Linux and other operating systems
- •Installing Additional Software with gzip and tar
- •Installing Additional Software with RPM
- •Removing software with RPM
- •Upgrading software with RPM
- •Query the RPM software
- •Verify the RPM software
- •Verify the package files
- •Upgrading the Kernel
- •Upgrading a Linux Kernel
- •System Log Files
- •The Final Test of the Installation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •What is the X Window System?
- •The X Window System
- •X Client and Server communications
- •X Window Manager
- •Configuring X Window Systems
- •Custom X Window System Programs
- •Manual Configuration of the X Window System
- •Documentation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Basic Network Services
- •TCP/IP Protocol Suite
- •Connection protocols needed
- •Other network protocols
- •Configuring Basic Network Services
- •Host name
- •IP addressing
- •DHCP
- •Netmask
- •Hardware resources
- •Routing and gateways
- •PPP, SLIP and PLIP connections
- •Server Tasks with
- •IP aliases for virtual hosts
- •Apache Web Server
- •Samba File Server
- •Home directories
- •Disk shares
- •Configuring Client Services
- •SMB/CIFS
- •NIS client configuration
- •NFS client configuration
- •Configuring Internet Services
- •Web browser
- •POP and SMTP
- •TFTP
- •SNMP
- •Remote Access
- •Rlogin
- •Telnet
- •OpenSSH
- •Documentation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Adding Hardware
- •Memory
- •Swap
- •Adding a hard drive
- •Video and monitor
- •Printers
- •Configuration files
- •Setting environment variables
- •BASH
- •Documentation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Basic User and Group Administration
- •What are users and groups?
- •Creating users
- •Change user information
- •Deleting users
- •Creating groups
- •Getting Around Linux
- •Navigating Linux
- •Common file and directory commands
- •Setting File and Directory Permissions
- •Mounting and Managing File Systems
- •Mount
- •Umount
- •Mounted file systems
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Multi-User Environment
- •The creation of Virtual Consoles
- •The Linux Terminal Server Project
- •Configurations for remote systems
- •Monitoring remote connections
- •Common Shell Commands
- •Basic shell scripts
- •Caution using root access
- •Navigating the GUI interface
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Linux Runlevels
- •init
- •Shutting down Linux
- •Managing Linux Services
- •Configuring Linux Printing
- •lpd daemon
- •/etc/printcap
- •Printing management
- •Using the vi Editor
- •vi operation modes
- •Editing text files
- •Using the
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Disk and File System Management
- •Repairing Partitions
- •System Automation and Scheduling
- •cron
- •Core Dumps
- •Analyzing core dumps
- •GNU Debugger
- •Managing Networking Interfaces
- •Installing System Packages and Patches
- •Compressed archive
- •Debian Package Installer
- •Slackware Package Installation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Linux Processes
- •Core services versus non-critical services
- •Process administration
- •Process control
- •Monitoring Log Files
- •Maintaining Documentation
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Linux Security
- •Securing the Environment
- •Location
- •Environment
- •System Security
- •System/user files
- •Permissions
- •Log auditing
- •Backups
- •Linux Security Best Practices
- •Network security
- •Firewall
- •System security
- •Securing a Web server
- •Securing an FTP server
- •FTP program version
- •FTP configuration files
- •Process security
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Disaster Recovery Planning
- •Types of data
- •Frequency and Scheduling
- •Storage and media types
- •Recovering data
- •Offsite storage
- •Linux Backup Tools and Commands
- •Third party tools
- •Tape devices
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Identifying the Problem
- •Methodology and Best Practices
- •Troubleshooting Resources
- •Documentation resources
- •Internet resources
- •System Log Files
- •Tools for Log Files
- •Output to another file
- •Locating files
- •Process Configuration and Management
- •Stopping, Starting, and Restarting Processes
- •Configuration Files
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Examining the Startup Process
- •Boot process steps
- •Analyzing Boot Process Errors
- •Common Boot Problems
- •Using System Status Tools
- •File System Check
- •System Resource Commands
- •Using the System Boot Disk
- •Types of boot disks
- •Creating a boot disk
- •Creating a rescue/utility disk
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Common User Problems
- •Login problems
- •File and directory permissions
- •Printing problems
- •Mail problems
- •Software Package Problems
- •Package dependencies
- •Software and version conflicts
- •Backup and Restore Errors
- •Backup hardware
- •Backup software
- •File restore errors
- •Application Failures
- •Log files
- •Process and daemon errors
- •Web server errors
- •Telnet
- •Mail services
- •Basic Networking Troubleshooting
- •Networking connectivity
- •Network hardware problems
- •Summary
- •Assessment Questions
- •Scenarios
- •Lab Exercises
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •Mainboard Components
- •BIOS
- •System memory
- •System Resources
- •I/O addresses
- •Direct memory access
- •Laptop Considerations
- •PCMCIA
- •Linux Peripheral Configuration
- •Installing and Configuring SCSI Devices
- •SCSI definitions
- •SCSI technologies
- •SCSI cabling and termination
- •SCSI device configuration
- •Linux SCSI devices
- •ATA/IDE Devices
- •IDE drive configuration
- •Linux ATA/IDE Drive configuration
- •Linux Support for Other Devices
- •IEEE 1394 (Firewire)
- •Summary
- •Assessment Questions
- •Scenarios
- •Answers to Chapter Questions
- •Chapter Pre-test
- •Assessment Questions
- •Scenarios
- •What’s on the CD-ROM
- •System Requirements
- •Using the CD with Microsoft Windows
- •Using the CD with Linux
- •Microsoft Windows applications
- •Linux applications
- •Troubleshooting
- •Sample Exam
- •Exam Questions
- •Exam Answers
- •Taking a CompTIA Exam
- •How to register for an exam
- •What to expect at the testing center
- •Your exam results
- •If you don’t receive a passing score
- •About the Linux + Exam
- •Preparing for the Linux+ Exam
- •For More Information
- •Preamble
- •No Warranty
- •Glossary
- •Index
Chapter 4 Installing Linux |
99 |
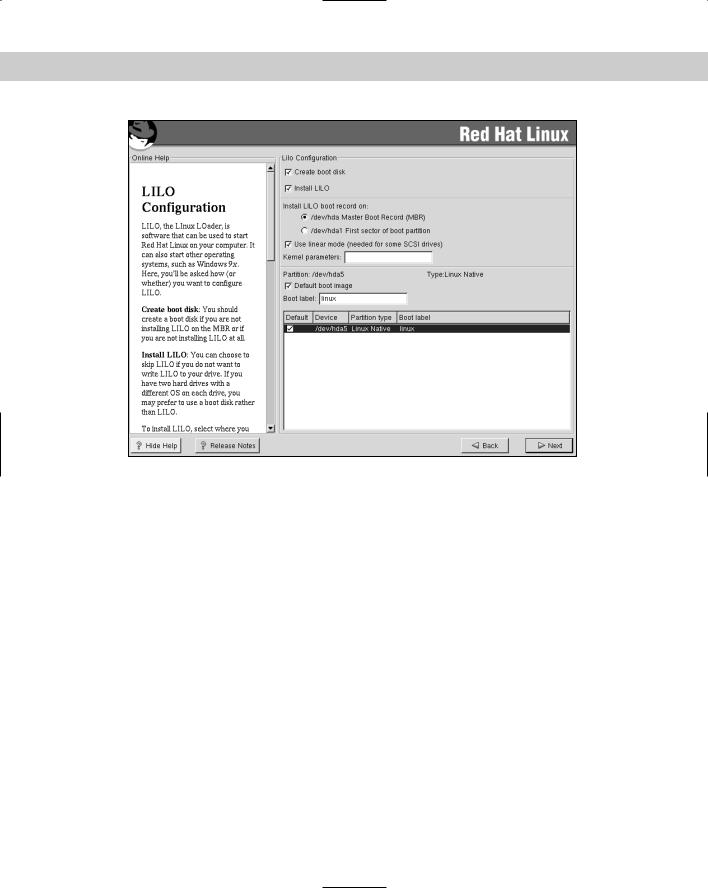
Installing a boot manager
2.16 Install boot loader (e.g., LILO, MBR vs. first sector of boot partition)
The next selection in the Red Hat Linux installation is to choose the type of boot loader and its location. A boot loader is used to boot the operating system into the intended operating system, which is achieved by loading a bootstrap onto the hard drive. This bootstrap then tells the computer system where to find the next part of the operating system to be loaded. Sometimes the bootstrap will reference a menu that allows the computer system to choose from several operating systems. LILO is the default boot loader on most Linux systems; however, GRUB is also an option. GRUB is a multi-system boot loader created by the GNU project. There are also commercial products that can provide this bootstrap and can be used as the boot loader or boot manager for a Linux system. LILO, or Linux Loader, is used to boot the system into Linux and also provides many tools for troubleshooting a system that does not boot properly. LILO can be used to boot backup copies or different versions of the operating system’s kernel, and it can, as previously stated, allow for a dual boot of the Linux operating system and another operating system. Using LILO to perform the duties of a boot loader is fairly straightforward, but be aware of a couple of notable points:
The location of the bootstrap can be placed in the Master Boot Record (MBR) or the first sector of the boot partition. The Master Boot Record is generally used, but on some systems that are running multiple operating systems, this may not be the best selection because LILO may not work properly with the other operating system.
Because Microsoft Windows NT and 2000 uses NTFS as the file system, LILO won’t be able to boot the Microsoft system. This is not true of Microsoft Windows NT installations that use FAT 16 partitions or Microsoft Windows 2000 installations that use Win98 FAT 32 partitions. In situations were LILO is not loaded in the Master Boot Record, the first boot block of the drive containing Linux is usually used.
When planning to Dual-Boot Linux with any other product, back up the data on the existing operating system before proceeding with the second operating system installation.
Figure 4-8 illustrates the screen that Red Hat uses to determine were LILO is loaded (if it is loaded at all). The installation of LILO can be bypassed if another boot loader is used, such as GRUB or a commercial product.
100 Part II Installation
Figure 4-8: The Red Hat LILO configuration screen
Creating the Boot Diskette
The next noticeable feature included with the Red Hat installation and in most distributions is the option to make a bootable diskette that can be used to recover a non-bootable system, or to boot the system if LILO is not installed in the Master Boot Record (MBR). Finally, the installer must select the default system to be booted. On a system that may have both Microsoft Windows 98 and Linux, LILO can be set to boot either system by default with the option to boot the other one. This is a useful tool for those who want to run Linux but have a desire or need to use Microsoft or other operating systems. After LILO, GRUB, or another boot manager has been determined and loaded, the system will be able to boot Linux or any other operating system.
Chapter 4 Installing Linux 101
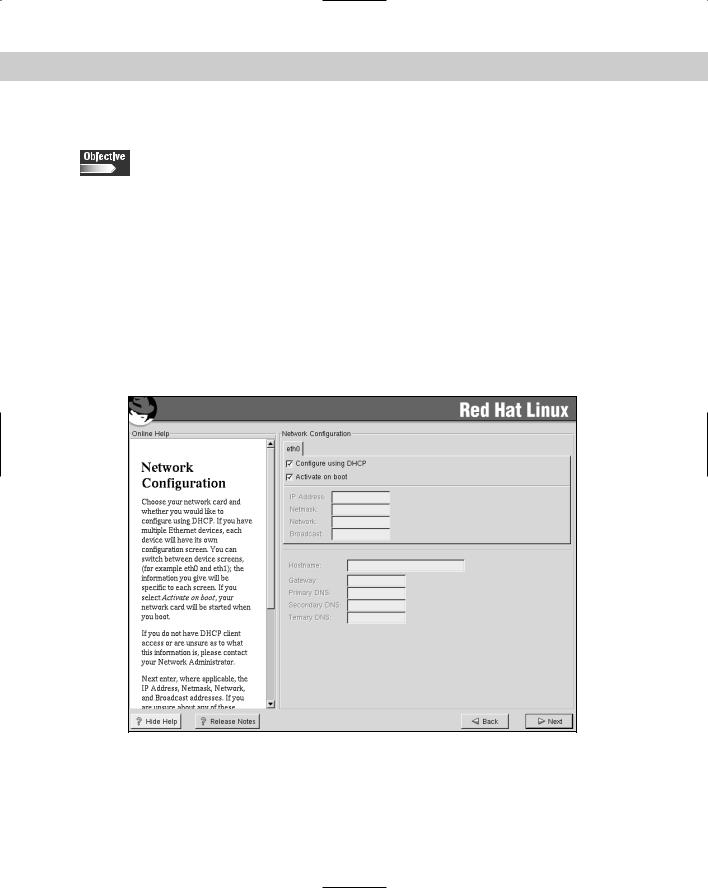
Networking
2.8 Select appropriate networking configuration and protocols (e.g., modems, Ethernet, Token-Ring)
At this point, the operating system is now bootable, so the next step in the Red Hat installation is to set up networking. Networking is what Linux was created to do; because Linux is a UNIX-like operating system, it has inherited the powerful TCP/IP features of UNIX and uses them by default. Although this isn’t the next step in every Linux distribution, the choices are all very similar to the Red Hat installation menus. Networking is detected during the initialization of the system and is therefore presented from the installer at this stage. The network card that is detected is given an interface name. In this case, the name is eth0, as shown in Figure 4-9, but it can also be given interface names that map to other protocols such as token ring, FDDI, or PPP (or PPPoE used with some xDSL cards) if using a modem or other device. Although this can be accomplished with a modem, not all Linux distributions configure modem networking during installation.
Figure 4-9: The Red Hat network configuration screen
102 Part II Installation
To configure the Ethernet card, the installer must have information about the availability of Dynamic Host Configuration Protocol, (DHCP), which allows the system to lease an IP address for a limited amount of time. The lease is renewed if the client requests an update before the lease expires and if the server approves the renewal. Therefore, if a DHCP server is available, this is usually the easiest and best option for configuring an Ethernet NIC, or network interface card. If a DHCP server is not available, then a static address must be used; otherwise, networking will not start. Usually, if static addresses are used, a network administrator controls which addresses are used and on what equipment. A request for an IP address from the network administrator will generally result in an IP address for the system. That IP address will have the format of 4 octets of information. This can be in binary, hex, or decimal form, but is usually in decimal and is seen when you ping an address. For this example, I use 192.168.0.50, which is part of a class C address and uses a subnet mask of 255.255.255.0 by default.
The subnet mask is used to break up groups of computers so that they can work more effectively on the network. After the IP and subnet mask have been input, the system will complete the network and broadcast sections. The installer will then need to input the Hostname of the system that will ID the system, the Gateway (usually a router) that will usually provide access to the Internet or intranet, and up to three DNS (domain name system) that will be used to resolve machine names to IP addresses. After all these networking items are configured, the system should be ready to work on the network. Although the networking is configured, the security of the networking is not complete until a firewall setting has been selected. This firewall setting is set to low, medium, or high; here is a breakdown of each setting:
Low security allows all services access to the machine and is usually only used in a closed environment or testing situations.
Medium security is the default and opens most of the known ports for operation. This is important, because if a required service is blocked, then the system may not be able to network correctly. For example, if DNS were blocked, then the system would not be able to resolve the Fully Qualified Domain Name, or FQDN (such as the server www.linux.org), and therefore, would not be able to reach the Web site. The medium setting is the default because it opens these services.
The high security level blocks all but a few services, such as DNS, and really isolates the system. This level of security is most appropriate on a server where access is limited to only the services that the system provides. If a server provides FTP services, then perhaps only these services that provide FTP should be open. This will prevent attacks on another service from affecting the FTP server.
Firewall services are now set up during installation and usually use a screen, as shown in Figure 4-10, to enable the configuration of the firewall.
