
- •Foreword
- •Criminology Comes of Age
- •Rules That Commute
- •Environmental Criminology and the Path to Crime Control
- •Preface
- •The Author
- •Acknowledgments
- •Dedication
- •Table of Contents
- •List of Tables
- •List of Figures
- •Quotation
- •2.1 Serial Murder
- •2.1.1.1 Characteristics
- •2.1.2 Incidence, Population, and Growth
- •2.1.3 Theories
- •2.1.4 Victimology
- •2.2 Child Murder
- •2.3 Murder and Distance
- •3.1 Serial Rape
- •3.2 Serial Arson
- •4.2 Police Strategies
- •4.2.1 Linkage Analysis
- •4.2.1.1 Physical Evidence
- •4.2.1.2 Offender Description
- •4.2.1.3 Crime Scene Behaviour
- •4.2.2 Other Investigative Tactics
- •5.2 Organized and Disorganized Crime Scenes
- •5.4 Critiques
- •5.5 Evaluation Studies
- •5.7 Expert Testimony
- •6.1 Movement and Distance
- •6.2 Mental Maps
- •6.3 Awareness and Activity Spaces
- •6.3.1 Anchor Points
- •6.4 Centrography
- •6.5 Nearest Neighbour Analysis
- •7.1 Geography and Crime Studies
- •7.2 Environmental Criminology
- •7.2.1 Routine Activity Theory
- •7.2.2 Rational Choice Theory
- •7.2.3 Crime Pattern Theory
- •8.1 Target Patterns
- •8.1.1 Place and Space
- •8.1.2 Hunting Grounds
- •8.1.3 Target Backcloth
- •8.1.4 Crime Sites
- •8.1.5 Body Disposal
- •8.1.6 Learning and Displacement
- •8.1.7 Offender Type
- •8.2 Hunting Methods
- •8.2.1 Target Cues
- •8.2.2 Hunting Humans
- •8.2.3 Search and Attack
- •8.2.4 Predator Hunting Typology
- •9.1 Spatial Typologies
- •9.2 Geography of Serial Murder
- •9.2.1 Methodology
- •9.2.1.1 Serial Killer Data
- •9.2.1.2 Newspaper Sources
- •9.2.1.3 Offender, Victim, and Location Data
- •9.2.2 Serial Killer Characteristics
- •9.2.2.1 State Comparisons
- •9.2.3 Case Descriptions
- •9.2.3.1 Richard Chase
- •9.2.3.2 Albert DeSalvo
- •9.2.3.3 Clifford Olson
- •9.2.3.4 Angelo Buono and Kenneth Bianchi
- •9.2.3.5 Peter Sutcliffe
- •9.2.3.6 Richard Ramirez
- •9.2.3.7 David Berkowitz
- •9.2.3.8 Jeffrey Dahmer
- •9.2.3.9 Joel Rifkin
- •9.2.3.10 John Collins
- •9.2.3.11 Aileen Wuornos
- •9.2.3.12 Ian Brady and Myra Hindley
- •9.2.3.13 Jerry Brudos
- •9.4 Serial Murder Characteristics
- •9.4.1 Offenders
- •9.4.2 Victims
- •9.4.3 Locations
- •9.4.4 Crime Parsing
- •9.4.5 Clusters
- •9.4.6 Trip Distance Increase
- •10.1 Mapping and Crime Analysis
- •10.2 Geography and Crime Investigation
- •10.3 Offender Residence Prediction
- •10.3.1 Criminal Geographic Targeting
- •10.3.2 Performance
- •10.3.3 Validity, Reliability, and Utility
- •10.3.3.1 Validity
- •10.3.3.2 Reliability
- •10.3.3.3 Utility
- •10.4.2 Operational Procedures
- •10.4.2.1 Information Requirements
- •10.4.3 Understudy Training Program
- •10.4.4 The Rigel Computer System
- •11.1 Strategies and Tactics
- •11.1.1 Suspect Prioritization
- •11.1.2 Police Information Systems
- •11.1.3 Task Force Management
- •11.1.4 Sex Offender Registries
- •11.1.5 Government and Business Databases
- •11.1.6 Motor Vehicle Registrations
- •11.1.7 Patrol Saturation and Stakeouts
- •11.1.8 Response Plans
- •11.1.9 Mail Outs
- •11.1.10 Neighbourhood Canvasses
- •11.1.11 News Media
- •11.1.12 Bloodings
- •11.1.13 Peak-of-Tension Polygraphy
- •11.1.14 Fugitive Location
- •11.1.15 Missing Bodies
- •11.1.16 Trial Court Expert Evidence
- •11.2 Jack the Ripper
- •DATA CODING FORM #1: SERIAL MURDER OFFENDERS
- •DATA CODING FORM #2: SERIAL MURDER VICTIMS
- •DATA CODING FORM #3: SERIAL MURDER LOCATIONS
- •Glossary
- •Bibliography
4.2.1.3Crime Scene Behaviour
The behavioural analysis of crime scenes provides a third, and rapidly developing, methodology for offence comparison. Linking crimes behaviourally requires comparing similarities versus differences for both related and unrelated crimes (see Robertson & Vignaux, 1995). Like crimes should show more similarities than differences, and unlike crimes, more differences than similarities. These comparisons are usually assessed in terms of proximity in time and space between offences, comparable modus operandi (method of operation), and the presence of signature.
Crimes that take place close together in space and time are obviously more likely to be connected than those separated by significant distance and occurring years apart. This is not to say that some offenders do not travel great distances, change residences, or interrupt their criminal activity for personal, employment, or institutional reasons. It only means that geographic and temporal factors affect the probability of offence linkage, with those more proximate more likely to be connected.
Modus operandi (M.O.) involves the mechanics of the crime, and can be broken down into three chronologically-ordered stages comprising the methods used by an offender to: (1) hunt (find and attack the victim); (2) protect identity; and (3) escape from the scene. Modus operandi has also been defined as those actions used by the offender to: (1) commit the crime;
(2) commit the crime; and (3) escape from the scene. It has been our experience, however, that significant offender behaviour exists in the search and hunt for a victim, and therefore M.O. should include these activities. Protection of identity can also occur at any and all stages of the offence.
The matrix in Table 4.1 helps categorize modus operandi behaviour and can serve as a framework for comparative case analysis. It is based on the above three stages divided into aggressive (what is done to accomplish the crime) and defensive (what is done to protect the offender) actions:
Table 4.1 Modus Operandi Matrix
Action/Stage Hunt Crime Escape
Defensive
Offensive
Modus operandi is not constant, but rather varies and changes for a variety of reasons. Like all human behaviour, it is subject to individual deviation and random fluctuations. M.O. is responsive to environmental influences, such as victim reaction, the physical conditions of a crime setting, and ongoing police activities and media attention. Displacement may result from police activities, and can take the form of changes in the spatial, temporal,
© 2000 by CRC Press LLC
target, tactical, or functional characteristics of the crimes (Gabor, 1978; Reppetto, 1976). Over time, an offender’s method of operation often evolves as the result of education, maturity and experience; fantasy progression and development can also occur.
Unlike M.O.,“signature” is constant, though certain aspects of its expression may evolve and improve over time (Keppel, 1995; Keppel & Birnes, 1997). Signature is defined as behaviour that goes beyond the actions needed to commit the crime; it is a fantasy-based ritual or combinations of rituals that represent a unique and personal expression of the offender (Douglas & Munn, 1992). When present, it provides a useful method for establishing links between crimes and can indicate certain underlying needs of the offender (Homant, 1998).
Staging is another consideration when examining behaviour (Douglas & Munn, 1992). Staging occurs when the crime scene is purposely altered. This is usually done by the offender in an attempt to mislead the police and typically involves a criminal who knew the victim and hopes to create a convincing alternative scenario. Crime scenes have also been changed by family members to protect the victim from embarrassment (in cases of autoerotic fatalities, for example).
One of the functions of criminal profiling is the assessment of the likelihood that one or more crimes were committed by the same offender. In Projects Eclipse and Kayo, a team of profilers assessed several unsolved murders of prostitutes and young women in Vancouver and Edmonton, respectively, in the effort to establish possible connections between the crimes (MacKay, 1994). Geographical analysis can also help disentangle different series of crimes (see the discussion on parsing and crime sets in Chapter 9).
The reality, however, is that the ability of the police to link serial crimes is limited. Establishing offence connections is often a difficult exercise, especially so in busy urban environments characterized by high levels of crime. The backdrop of other, similar offences can interfere with the process, and such “background noise” can make it difficult to know who is responsible for what. Consistency and constancy are not characteristics of many criminal offenders, and when an analysis does indicate that certain crimes are connected, the links are usually referred to in terms of probabilities rather than certainties. This is made all the more difficult when multiple offenders are involved.
A further complication is that the links might be between different incident types. For example, in the case of a serial rapist who breaks into apartments to attack women, police must review not just other rapes and attempts, but also sexual assaults, residential burglaries, and prowlings. Correctly establishing a serial criminal’s pattern can involve analyzing hundreds or even thousands of crimes.
The major response to these problems has been the establishment of computer systems containing centralized investigative information networks.
© 2000 by CRC Press LLC
The idea of a national computer database to link murders originated with Pierce Brooks, a retired captain of detectives in the Los Angeles Police Department (LAPD) homicide unit (Brooks, 1984; Howlett, Hanfland, & Ressler, 1986). During his investigation of California serial killer Harvey Glatman in the late 1950s, Brooks found he had to resort to combing various newspaper files in order to locate murders that might fit the pattern from outside LAPD’s jurisdiction (Newton, 1998; Ressler & Shachtman, 1992). With input from the National Serial Murder Advisory Group, the Violent Criminal Apprehension Program (VICAP) Program was formed in the early 1980s (Keppel & Weis, 1994).
Under the auspices of the National Center for the Analysis of Violent Crime (NCAVC), VICAP went operational in 1985. It uses a standardized form containing a series of behaviourally-oriented questions concerning the crime, victim, and offender that allows for computerized matching of similar cases from a national database. As part of its protocol, VICAP identifies critical time and location factors, including the different types of scenes associated with a murder: (1) victim’s last known location; (2) site of offender’s initial contact with victim; (3) murder or major assault site; and
(4) body recovery site (Ressler et al., 1988). This allows for the calculation of time and distance relationships, the importance of which was stressed by the National Serial Murder Advisory Group (Keppel & Weis, 1994).
Britain and Europe have had modus operandi-based crime notification systems for series detection — the matching of crime with crime, and offence with offender — since 1907 (Brooks et al., 1987, 1988; Green & Whitmore, 1993; Rebscher & Rohrer, 1991). The British police developed a Crime Pattern Analysis (CPA) computerized database within the National Criminal Intelligence Service (NCIS) following the Yorkshire Ripper case. Currently, the Serious Crime Analysis Section (SCAS), National Crime Faculty, is mandated to conduct comparative case analysis for murders, rapes, and abductions.
Several states have also developed their own computerized crime linkage systems, some of which feed into VICAP. Examples of these programs include the Washington Homicide Investigation Tracking System (HITS) (also used in Oregon and Idaho); the New York Homicide Assessment and Lead Tracking (HALT) system; the Florida Violent Crime Investigation System (ViCIS); the Indiana Criminal Apprehension Assistance Program (ICAAP); the Iowa Sex Crimes Analysis System; the Michigan Sex Motivated Crime File; the Minnesota Sex Crimes Analysis Program (MN/SCAP); the New Jersey Homicide Evaluation and Assessment Tracking (HEAT) System; the North Carolina State Homicide and Assault Reporting (SHARE) system; the Oklahoma Sex Crime Analysis and Reporting System (SCARS); and the Pennsylvania ATAC Program (Cryan, 1988; Geberth, 1994; Keppel & Weis, 1993a, 1993b; Collins, Johnson, Choy, Davidson, & MacKay, 1998). Also, six Regional Information Sharing Systems
© 2000 by CRC Press LLC
(RISS) Programs now exist across the U.S. to provide multi-jurisdictional intelligence and investigative analysis networks (U.S. Department of Justice, 1998).
Sex offences are much more common than murder, and when these programs began to collect data on rapes and sexual assaults the power and usefulness of computerized crime linkage systems became readily apparent. Pattern recognition models for linking and predicting serial arsons, based on cluster analysis of variables related to location, time of day, day of week, and modus operandi, have also been developed (Icove, 1981; Icove & Crisman, 1975).
The Canadian Violent Crime Linkage Analysis System (ViCLAS), developed by the RCMP, went national in 1995 (Johnson, 1994). Since then, ViCLAS has achieved international recognition and has now been adopted for use by Austria, The Netherlands, Australia, Belgium, Germany, and Britain, along with certain American states including Indiana, New Jersey, and Tennessee (Collins et al., 1998; Kocsis & Davies, 1997). Several other countries are considering its introduction. Significant new versions of both VICAP and ViCLAS were introduced in 1999.
ViCLAS uses a relational database within a Windows environment. Terminals across the country communicate over a national wide-area network (WAN) to a central database in Ottawa, Ontario. Data transmission is encrypted on dedicated lines. There is also continual case tracking and auditing. In Ontario, ViCLAS reporting is mandatory as the result of one of the recommendations of the Campbell report, a judicial review into the investigation of the Paul Bernardo murder case. As of mid-1999, there are over 70,000 cases on ViCLAS.
A major difficulty with computerized linkage systems is low reporting rates. This causes a serious data shortage problem because case matches are an exponential function of reporting level.22 For example, if only 50% of the crimes are entered, then only 25% of the potential linkages can be identified; with a 20% reporting rate, the linkage ability drops to 4%. It is paradoxical that some police officers, who typically possess little faith in offender rehabilitation, fail to see the value in a comprehensive criminal tracking system.
One of the common reasons quoted for failure to report cases is the time it takes an investigator to complete the input forms, which can involve over 150 questions. Therefore, the choice of behaviours used in the analysis is critical. Both discrimination and utility are important. Certain offender
22 Generally, if x represents the reporting rate, and y the linkage rate (expressed as proportions of their potential totals), then: y = x1/2. This equation is an approximation because the exact relationship depends on the mean number of crimes in a series, and on how a series connection is defined (e.g., if 3 crimes out of a possible 10 are connected, does this qualify as a successful series identification?).
© 2000 by CRC Press LLC
actions are so common (e.g., vaginal intercourse) as to be poor discriminators. Other behaviours are so rare (e.g., the offender writes on the victim’s body) that they are unlikely to be encountered.23 Crime linkage is a holistic process and the questions must also provide a full understanding of events. System designers need to balance the requirement for parsimony with the necessity for a comprehensive assessment of crime scene behaviour.
An underlying assumption of linkage systems is that the analyzed behaviours are more or less consistent across offences. An examination of child abduction murders in the U.S. showed that victim gender and use of bindings were the most important and consistent linkage variables (Hanfland, Keppel, & Weis, 1997). Offender speech forms have been found consistent and useful in connecting rape cases (Dale & Davies, 1994a), and the London Metropolitan Police Sexual Assault Index analyses verbal themes as part of the process of linking crimes (Copson, 1993). However, FBI research on 108 serial rapists determined that 58% of the 119 behavioural variables they examined reflected zero or minimal consistency across crimes (Warren et al., 1995). Alone, such questions make a poor basis for a case linkage system; together, they may point to common underlying fantasies or behavioural themes.
The true strength of these systems therefore lies in their ability to make concurrent comparisons between multiple variables. A study of British serial rapists found that 28% of the offenders took steps to prevent their face from being seen by the victim (Davies & Dale, 1995b). In the FBI research, it was noted that 70% of the attacks took place indoors, and 60% within the victim’s home (Warren et al., 1995). These are not powerful discriminators separately, but assuming independence between questions, they can be combined in powerful ways. A burglary rapist who covers his face might only represent 17% of the offender population. Additional variables can help increase the focus. To facilitate this analytic process, the latest version of ViCLAS produces multivariate statistics upon demand.
The process of recognition — whether it be of faces, scenes, automobiles, voices, architecture — is based less on individual elements than on the relationships between them. Humans are much better than serial-processing computers at image and complex pattern recognition (Marshall & Zohar, 1997). As of today, most computerized case linkage systems are only designed to manage and search through large volumes of information, leaving the ultimate determination of case association to the analyst. As the volume of information collected by these databases increases, the need for expert system support becomes more crucial.
23 A question can be reversed and phrased in the negative (e.g., “Was the victim transported?” becomes “Did the crime take place at a single location?”); an inversion makes a common behaviour uncommon.
© 2000 by CRC Press LLC
Grubin, Kelly, and Ayis (1996) caution that because of “the softer and more fluid substance of behavioural ‘evidence’ … [the process of linking crimes] must be based on scientific principles rather than on a combination of intuition, experience and theory” (pp. 12, 20). They summarize the practical problems in using offender behaviour to link crimes as follows:
(1) consistent but common behaviours; (2) consistent but uncommon behaviours; (3) preciseness of behaviour description; (4) behaviour influenced by victim response; (5) weighting and relative importance of behaviours; (6) variation in behaviour consistency; (7) evolution of behaviour; and (8) interpretation of behaviours.
Grubin et al. (1996, 1997) examined how offender behaviours at crime scenes group and interact in an effort to link serious stranger sexual offences. Four domains — control, sex, escape, and style — were used to identify 30 dichotomous variables for cluster analysis. The research assessed consistency within a domain over a series of offences (vertical consistency), and the degree to which similar domain patterns occur within an offence (horizontal consistency). Behavioural consistency across offences was found, lending support to the efficacy of this approach. This method of looking for the emergence of constant patterns is similar to the process of DNA matching where genetic alleles are compared.
The concept that linked crimes should be interconnected provides one simple method for pattern determination. In other words, if crime A shows similarities to crime B, and crime B shows similarities to crime C, then crime C should also show similarities to crime A. If this is the case, then the probability of these crimes being connected increases.
Consider an example involving the investigation of five prostitute murders in which police want to establish which crimes are connected. The victims are Smith, Jones, Baker, Anderson, and Williams. Analysts have determined there are seven crime scene behaviours of interest. These are:
Variable 1 — victim strangled;
Variable 2 — victim found nude;
Variable 3 — bindings used;
Variable 4 — skid row prostitute;
Variable 5 — victim’s body concealed;
Variable 6 — victim decapitated; and
Variable 7 — victim stabbed.
Table 4.2 shows the case variable matrix for this example. Vn refers to the variable number, and Cn to the victim (crime) number. An X indicates the presence of that variable in a given murder. The results from the case variable matrix are then plotted in a case linkage chart. This diagram depicts
© 2000 by CRC Press LLC
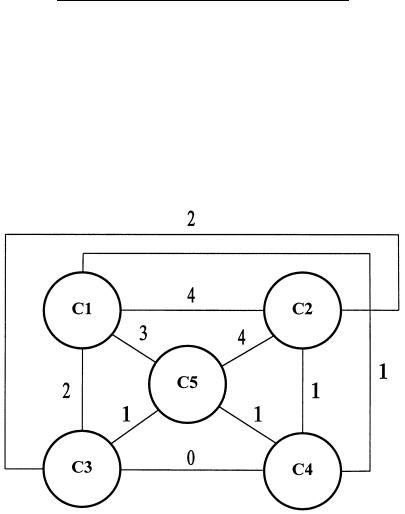
Table 4.2 Case Variable Matrix
Victim/Variable |
V1 |
V2 |
V3 |
V4 |
V5 |
V6 |
V7 |
|
|
|
|
|
|
|
|
|
|
C1 |
(Smith) |
X |
X |
X |
X |
|
|
|
C2 |
(Jones) |
X |
X |
X |
X |
X |
|
|
C3 |
(Baker) |
|
X |
|
X |
|
|
X |
C4 |
(Anderson) |
X |
|
|
|
|
X |
|
C5 |
(Williams) |
X |
|
X |
X |
X |
|
|
|
|
|
|
|
|
|
|
|
the strength of association, in terms of the behaviour variables of interest, between the different crimes. The proper selection and phrasing of crime behaviours are important parts of this analysis. Figure 4.1 shows the case linkage chart for this example.
Figure 4.1 Case linkage chart.
In this example, crimes 1, 2, and 5 (Smith, Jones, and Williams) show an interconnected pattern, suggesting that they were all committed by the same offender. This approach can be refined by weighting the importance of the variables under consideration. Variables that are less common (e.g., victim was decapitated) establish a stronger probability of connection than those more common (e.g., victim was strangled). This method is particularly useful when physical evidence exists establishing definitive links between some cases but not others. Behavioural interconnections can help determine the probable extent of the crime series. Such an approach was used in Lübeck,
© 2000 by CRC Press LLC
