
- •Introduction
- •Increasing Demand for Wireless QoS
- •Technical Approach
- •Outline
- •The Indoor Radio Channel
- •Time Variations of Channel Characteristics
- •Orthogonal Frequency Division Multiplexing
- •The 5 GHz Band
- •Interference Calculation
- •Error Probability Analysis
- •Results and Discussion
- •IEEE 802.11
- •IEEE 802.11 Reference Model
- •IEEE 802.11 Architecture and Services
- •Architecture
- •Services
- •802.11a Frame Format
- •Medium Access Control
- •Distributed Coordination Function
- •Collision Avoidance
- •Post-Backoff
- •Recovery Procedure and Retransmissions
- •Fragmentation
- •Hidden Stations and RTS/CTS
- •Synchronization and Beacons
- •Point Coordination Function
- •Contention Free Period and Superframes
- •QoS Support with PCF
- •The 802.11 Standards
- •IEEE 802.11
- •IEEE 802.11a
- •IEEE 802.11b
- •IEEE 802.11c
- •IEEE 802.11d
- •IEEE 802.11e
- •IEEE 802.11f
- •IEEE 802.11g
- •IEEE 802.11h
- •IEEE 802.11i
- •Overview and Introduction
- •Naming Conventions
- •Enhancements of the Legacy 802.11 MAC Protocol
- •Transmission Opportunity
- •Beacon Protection
- •Direct Link
- •Fragmentation
- •Traffic Differentiation, Access Categories, and Priorities
- •EDCF Parameter Sets per AC
- •Minimum Contention Window as Parameter per Access Category
- •Maximum TXOP Duration as Parameter per Access Category
- •Collisions of Frames
- •Other EDCF Parameters per AC that are not Part of 802.11e
- •Retry Counters as Parameter per Access Category
- •Persistence Factor as Parameter per Access Category
- •Traffic Streams
- •Default EDCF Parameter Set per Draft 4.0, Table 20.1
- •Hybrid Coordination Function, Controlled Channel Access
- •Controlled Access Period
- •Improved Efficiency
- •Throughput Improvement: Contention Free Bursts
- •Throughput Improvement: Block Acknowledgement
- •Delay Improvement: Controlled Contention
- •Maximum Achievable Throughput
- •System Saturation Throughput
- •Modifications of Bianchi’s Legacy 802.11 Model
- •Throughput Evaluation for Different EDCF Parameter Sets
- •Lower Priority AC Saturation Throughput
- •Higher Priority AC Saturation Throughput
- •Share of Capacity per Access Category
- •Calculation of Access Priorities from the EDCF Parameters
- •Markov Chain Analysis
- •The Priority Vector
- •Results and Discussion
- •QoS Support with EDCF Contending with Legacy DCF
- •1 EDCF Backoff Entity Against 1 DCF Station
- •Discussion
- •Summary
- •1 EDCF Backoff Entity Against 8 DCF Stations
- •Discussion
- •Summary
- •8 EDCF Backoff Entities Against 8 DCF Stations
- •Discussion
- •Summary
- •Contention Free Bursts
- •Contention Free Bursts and Link Adaptation
- •Simulation Scenario: two Overlapping QBSSs
- •Throughput Results with CFBs
- •Throughput Results with Static PHY mode 1
- •Delay Results with CFBs
- •Conclusion
- •Radio Resource Capture
- •Radio Resource Capture by Hidden Stations
- •Solution
- •Mutual Synchronization across QBSSs and Slotting
- •Evaluation
- •Simulation Results and Discussion
- •Conclusion
- •Prioritized Channel Access in Coexistence Scenarios
- •Saturation Throughput in Coexistence Scenarios
- •MSDU Delivery Delay in Coexistence Scenarios
- •Scenario
- •Simulation Results and Discussion
- •Conclusions about the HCF Controlled Channel Access
- •Summary and Conclusion
- •ETSI BRAN HiperLAN/2
- •Reference Model (Service Model)
- •System Architecture
- •Medium Access Control
- •Interworking Control of ETSI BRAN HiperLAN/2 and IEEE 802.11
- •CCHC Medium Access Control
- •CCHC Scenario
- •CCHC and Legacy 802.11
- •CCHC Working Principle
- •CCHC Frame Structure
- •Requirements for QoS Support
- •Coexistence Control of ETSI BRAN HiperLAN/2 and IEEE 802.11
- •Conventional Solutions to Support Coexistence of WLANs
- •Coexistence as a Game Problem
- •The Game Model
- •Overview
- •The Single Stage Game (SSG) Competition Model
- •The Superframe as SSG
- •Action, Action Space A, Requirements vs. Demands
- •Abstract Representation of QoS
- •Utility
- •Preference and Behavior
- •Payoff, Response and Equilibrium
- •The Multi Stage Game (MSG) Competition Model
- •Estimating the Demands of the Opponent Player
- •Description of the Estimation Method
- •Evaluation
- •Application and Improvements
- •Concluding Remark
- •The Superframe as Single Stage Game
- •The Markov Chain P
- •Illustration and Transition Probabilities
- •Definition of Corresponding States and Transitions
- •Solution of P
- •Collisions of Resource Allocation Attempts
- •Transition Probabilities Expressed with the QoS Demands
- •Average State Durations Expressed with the QoS Demands
- •Result
- •Evaluation
- •Conclusion
- •Definition and Objective of the Nash Equilibrium
- •Bargaining Domain
- •Core Behaviors
- •Available Behaviors
- •Strategies in MSGs
- •Payoff Calculation in the MSGs, Discounting and Patience
- •Static Strategies
- •Definition of Static Resource Allocation Strategies
- •Experimental Results
- •Scenario
- •Discussion
- •Persistent Behavior
- •Rational Behavior
- •Cooperative Behavior
- •Conclusion
- •Dynamic Strategies
- •Cooperation and Punishment
- •Condition for Cooperation
- •Experimental Results
- •Conclusion
- •Conclusions
- •Problem and Selected Method
- •Summary of Results
- •Contributions of this Thesis
- •Further Development and Motivation
- •IEEE 802.11a/e Simulation Tool “WARP2”
- •Model of Offered Traffic and Requirements
- •Table of Symbols
- •List of Figures
- •List of Tables
- •Abbreviations
- •Bibliography
102 |
5. Evaluation of IEEE 802.11e with the IEEE 802.11a Physical Layer |
5.3Radio Resource Capture
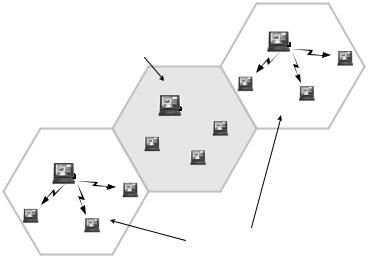
This section is based on Mangold et al. (2002c). Stations that are hidden to each other operate simultaneously, without mutually synchronized transmission, contention and CCA procedures. The contention-based channel access works only efficiently if all stations are in detection range of each other. There, if the channel gets idle at a specific point in time, the CCA processes of all stations indicate the channel idle. Then, stations will start their backoff procedures synchronously, and the backoff entity that first counts down its backoff counter determines the station which transmits next. The other backoff entities will defer from channel access. If this synchronized contention for channel access is not maintained owing to hidden stations, some stations may capture the radio channel for long time durations. This leads to problems in QoS support, as discussed in the following, where two scenarios are discussed. Note that the resource capture phenomenon exists with or without the 802.11e MAC enhancement.
5.3.1Radio Resource Capture by Hidden Stations
The resource capture by hidden stations was identified in Benveniste (2001; 2002), and there referred to as neighborhood capture. A station that is located in the detection range of other stations that are hidden to each other can only initiate a transmission if all of the hidden stations are idle.
BSS 2 may experience heavily loaded channel
BSS 3
|
BSS 2 |
BSS 1 |
BSS 1 and BSS 3 perform |
carrier sensing independently |
Figure 5.29: Scenario where two (Q)BSSs that are not in receive range of each other (BSS 1 and BSS 2) perform their CCA independently. Stations of (Q)BSS 2 may not detect an idle channel for undesirable long periods.
