
20411B-ENU-TrainerHandbook
.pdf
|
|
|
|
Administering Windows Server® 2012 11-7 |
||||
|
|
|
|
|
|
|
|
|
|
|
Audit policy |
|
Description |
Default setting |
MCT |
||
|
|
setting |
|
|||||
|
|
|
|
|
||||
|
|
|
|
|
|
|
|
|
|
|
Audit Logon |
Creates an event when a user logs on interactively |
Successful logons are |
USE |
|||
|
|
Events |
(locally) to a computer or over the network |
audited. |
||||
|
|
|
|
(remotely). For example, if a workstation and a |
|
|||
|
|
|
|
server are configured to audit logon events, the |
|
|||
|
|
|
|
workstation audits a user logging on directly to that |
|
|||
|
|
|
|
workstation. When the user connects to a shared |
|
|||
|
|
|
|
folder on the server, the server logs that remote |
|
|||
|
|
|
|
|
|
|
|
|
|
|
|
|
logon. When a user logs on, the domain controller |
|
|
|
|
|
|
|
|
records a logon event because logon scripts and |
|
|
|
|
|
|
|
|
policies are retrieved from the domain controller. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit Account |
Audits events, including the creation, deletion, or |
Successful account |
ONLY |
|||
|
|
Management |
modification of user, group, or computer accounts, |
management activities |
||||
|
|
|
|
and the resetting of user passwords. |
are audited. |
|||
|
|
|
|
|
|
|||
|
|
|
|
|
|
|
|
|
|
|
Audit Directory |
Audits events that are specified in the system access |
Successful directory |
. |
|||
|
|
|
|
|
||||
|
|
Service Access |
control list (SACL), which is seen in an Active |
service access events are |
||||
|
|
|
|
Directory object’s Properties Advanced Security |
audited, but few |
|
|
|
|
|
|
|
Settings dialog box. In addition to defining the audit |
objects’ SACLs specify |
|
|
|
|
|
|
|
policy with this setting, you must also configure |
audit settings. |
|
|
|
|
|
|
|
auditing for the specific object or objects by using |
|
|
|
|
|
|
|
|
the SACL of the object or objects. This policy is |
|
|
|
|
|
|
|
|
similar to the Audit Object Access policy that you |
|
|
|
|
|
|
|
|
use to audit files and folders, but this policy applies |
|
|
|
|
|
|
|
|
to Active Directory objects. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit Policy |
Audits changes to user rights assignment policies, |
Successful policy |
|
|
|
|
|
|
Change |
audit policies, or trust policies. |
changes are audited. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit Privilege Use |
Audits the use of a privilege or user right. See the |
No auditing is |
STUDENT |
|||
|
|
|
|
explanatory text for this policy in the Group Policy |
performed by default. |
|||
|
|
|
|
Management Editor. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit System |
Audits system restart, shutdown, or changes that |
Successful system |
|
|
|
|
|
|
Events |
affect the system or security logs. |
events are audited. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit Process |
Audits events such as program activation and |
No events are audited. |
USE |
|||
|
|
Tracking |
process exit. See the explanatory text for this policy |
|
||||
|
|
|
|
|
|
|||
|
|
|
|
in the Group Policy Management Editor. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Audit Object |
Audits access to objects such as files, folders, |
No events are audited. |
|
|
|
|
|
|
Access |
registry keys, and printers that have their own |
|
|
|
|
|
|
|
|
|
SACLs. In addition to enabling this audit policy, you |
|
|
|
|
|
|
|
|
must configure the auditing entries in objects’ |
|
|
|
|
|
|
|
|
SACLs. |
|
|
|
|
Notice that most major Active Directory events are already audited by domain controllers, assuming thatPROHIBITED the events are successful. Therefore, the creation of a user, the resetting of a user’s password, the logon to
failed account logon events, you can expose malicious attempts to access the domain by repeatedly trying to log on as a domain user account without yet knowing the account’s password. Auditing failed account


Administering Windows Server® 2012 |
MCT |
|
11-9 |
|
|
Auditing entries directs Windows operating systems to audit the successful or failed activities of a security principal (user, group, or computer) to use a specific permission. Full Control includes all individual access levels, so this entry covers any type of access. For example, if you assign Full Control to the Consultant group, and if a Consultant group member attempts access of any kind and fails, this activity will be logged.
Typically, auditing entries reflect the permission entries for the object, but auditing entries and |
USE |
|
permissions entries may not always match. In the above scenario, keep in mind, that a member of the |
||
Consultants group can also belong to another group that does have permission to access the folder. |
||
|
Because that access will be successful, the activity is not logged. Therefore, if you are concerned about restricting folder access and ensuring that users do not access it in any way, you should monitor failed access attempts. However, you should also audit successful access to identify situations in which a user is accessing the folder through another group membership that is potentially incorrect.
|
Note: Audit logs can get large quite rapidly. Therefore, configure the bare minimum |
ONLY. |
|||
|
|||||
required to achieve your company’s security objective. When you specify to audit the successes |
|||||
and failures on an active data folder for the Everyone group by using Full Control (all |
|||||
|
|
||||
permissions), this generates enormous audit logs that could affect the performance of the server, |
|
|
|||
and can make locating a specific audit event almost impossible. |
|
|
|||
Enabling Audit Policy |
|
|
|||
Configuring auditing entries in the security |
|
|
|
||
|
STUDENT |
||||
descriptor of a file or folder does not, in itself, |
|
||||
enable auditing. Auditing must be enabled by |
|
||||
defining the appropriate Audit object access |
|
||||
policy setting within Group Policy. |
|
||||
After auditing is enabled, the security subsystem |
|
||||
begins to log access as directed by the audit |
|
|
|
||
settings. |
|
|
|
||
The policy setting must be applied to the server |
|
|
|
||
that contains the object that is being audited. |
|
|
|
||
You can configure the policy setting in the server’s |
|
|
|
||
|
USE |
||||
local Group Policy Object (GPO), or you can use a |
|||||
|
|
||||
GPO that is scoped to the server. |
|
|
|||
You can define the policy then to audit Success events, Failure events, or both. The policy setting must specify auditing of Success or Failure attempts that match the type of auditing entry in the object’s SACL. For example, to log a failed attempt by Consultants to access the Confidential Data folder, you must configure the Audit object access policy to audit failures, and you must configure the SACL of the Confidential Data folder to audit failures. If the audit policy audits successes only, the failure entries in the folder’s SACL will not trigger logging.
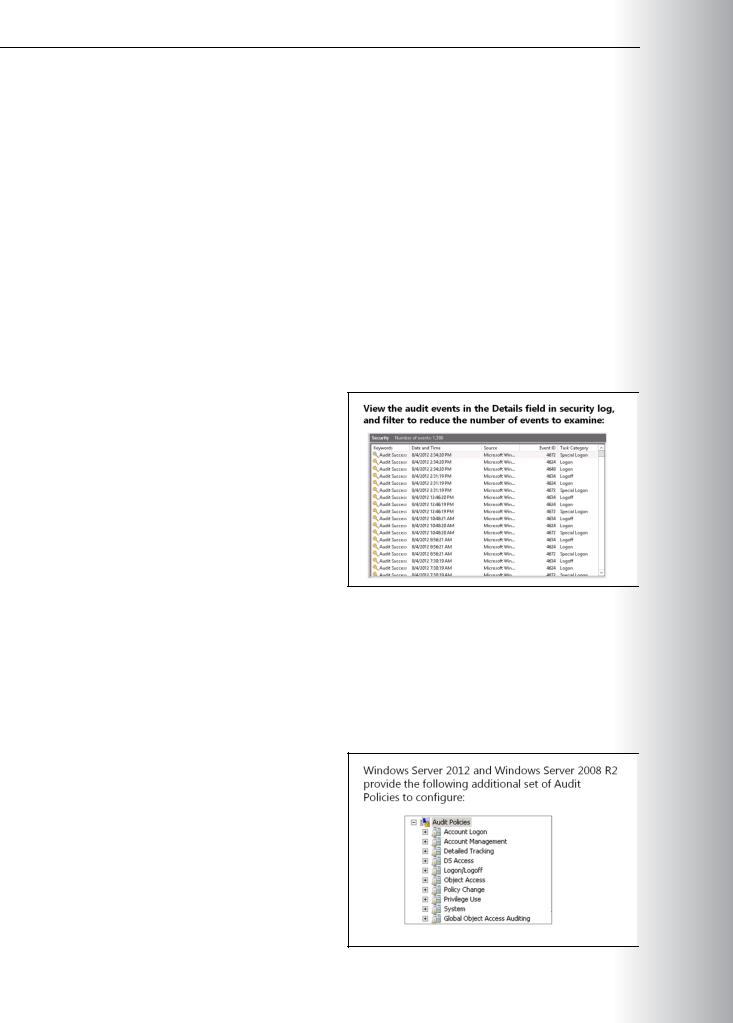
In Group Policy Management in AD DS, there is a group of standard settings in a GPO that control audit behavior. This set of audit policy settings is found under Computer Configuration, in the following node:
Windows Settings\Security\Local Policies\Audit Policy. The audit policy settings govern the following basic settings:
PROHIBITED
•Audit account logon events
•Audit account management

Administering Windows Server® 2012 |
MCT |
|
11-11 |
|
|
These security auditing enhancements can help your organization’s audit compliance with important |
|
|
business-related and security-related rules by tracking precisely defined activities, such as: |
|
|
•A group administrator who has modified settings or data on servers that contain finance information.
•An employee within a defined group who has accessed an important file. USE
•That the correct SACL is applied to every file and folder or registry key on a computer or file share, as a verifiable safeguard against undetected access.
Understanding Advanced Audit Policy Settings
•Account Logon. These settings enable auditing the validation of credentials, and other Kerberos- ONLY specific authentication and ticket operation events.
•Account Management. You can enable auditing for events relating to the modification of user
accounts, computer accounts, and groups with the Account Management group of settings. .
•Detailed Tracking. These settings control auditing of encryption events, Windows process creation and
•termination events, and remote procedure call (RPC) events. STUDENT DS Access. These audit settings involve access to Directory Services, including general access, changes,
and replication.
•Logon/Logoff. Standard logon and logoff events are audited by this group of settings. Other account specific activity, such as Internet Protocol security (IPsec), Network Policy Server, and other uncategorized logon and logoff events are also audited.
•Object Access. These settings enable auditing for any access to AD DS, registry, application, and file storage.
•Policy Change. When you configure these settings, internal changes to audit policy settings are audited.
•Privilege Use. Within the Windows environment, Windows Server 2012 audits attempts of privilege
use, when you configure these settings. USE
•System. System settings are used for auditing changes to the state of the security subsystem.
•Global Object Access Auditing. These settings are for controlling the SACL settings for all objects on one or more computers. When settings in this group are configured and applied with Group Policy,
SACL membership is determined by the configuration of the policy setting, and the SACLs are
configured directly on the server itself. You can configure SACLs for file system and registry access PROHIBITED under Global Object Access Auditing.


Administering Windows Server® 2012 11-13
Lab: Configuring Encryption and Advanced Auditing |
MCT |
|||
|
Scenario |
|
||
|
|
|
|
|
|
A. Datum is a global engineering and manufacturing company with head office based in London, United |
|||
|
Kingdom. An IT office and data center are located in London to support the London location and other |
USE |
||
|
locations. A. Datum has recently deployed a Windows Server 2012 server and client infrastructure. |
|||
|
|
|
||
|
You have been asked to configure the Windows Server 2012 environment to protect sensitive files, and to |
|||
|
ensure that access to files on the network is audited appropriately. You have also been asked to configure |
|||
|
auditing for the new server. |
|
.ONLY |
|
|
Objectives |
|
||
|
After completing this lab, you will be able to: |
|
||
|
• Encrypt and recover files by using EFS management tools. |
|||
|
• Configure advanced auditing. |
|
||
|
Lab Setup |
|
||
|
|
|
|
|
|
Estimated Time: 40 minutes |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Virtual Machines |
20411B-LON-DC1 |
|
|
|
|
20411B-LON-CL1 |
|
|
|
|
20411B-LON-SVR1 |
|
|
|
|
|
|
|
|
User Name |
Adatum\Administrator |
|
|
|
|
|
|
|
|
Password |
Pa$$w0rd |
STUDENT |
|
|
|
|
||
|
For this lab, you will use the available virtual machine environment. Before you begin the lab, you must |
|
|
|
complete the following steps:
1.On the host computer, click Start, point to Administrative Tools, and then click Hyper-V ManagerUSE.
2.In Hyper-V® Manager, click 20411B-LON-DC1, and in the Actions pane, click Start.
3.In the Actions pane, click Connect. Wait until the virtual machine starts.
4.Log on using the following credentials:
o User name: Adatum\Administrator PROHIBITED o Password: Pa$$w0rd
5.Perform steps 2 through 4 for 20411B-LON-CL1 and 20411B-LON-SVR1.


|
Administering Windows Server® 2012 |
MCT |
||
|
11-15 |
|
||
Task 4: Encrypt a file |
|
|
||
1. |
On LON-CL1, browse to \\LON-DC1\Mod11Share\Marketing. |
USE |
||
2. |
Open the properties of DougFile. |
|||
|
|
|||
3. |
Enable encryption in the advanced attributes for only the DougFile. |
|
|
|
4. |
Close Windows Explorer. |
|
|
|
5. |
Log off of LON-CL1. |
|
|
|
Task 5: Use the recovery agent to open the file
1.On LON-DC1, browse to E:\Labfiles\Mod11\Mod11Share\Marketing.
2.Open DougFile.txt, modify the contents, and then save the file.
Your manager has asked you to track all access to file shares that are stored on LON-SVR1. You also need to be aware of any time a user accesses a file on a removable storage device that is attached to the server. You have decided to implement the appropriate object access settings by using Advanced audit policy Configuration.
STUDENT .ONLY
1.Create a Group Policy Object (GPO) for advanced auditing.
2.Verify audit entries.
Task 1: Create a Group Policy Object (GPO) for advanced auditing
1.On LON-DC1, from Server Manager open Active Directory Users and Computers. USE
2.Create a new OU in Adatum.com named File Servers.
3.Move LON-SVR1 from the Computers container to the File Servers OU.
4.On LON-DC1, open Group Policy Management.
5.Create a new GPO called File Audit, and link it to the File Servers OU. PROHIBITED
6.Edit the File Audit GPO and under Computer Configuration, browse to the Advanced Audit Policy Configuration\Audit Policies\Object Access node.
7.Configure both the Audit Detailed File Share and Audit Removable Storage settings to record Success and Failure events.
8.Restart LON-SVR1 and log on as Adatum\Administrator with a password of Pa$$w0rd.



 PROHIBITED USE STUDENT .ONLY USE MCT
PROHIBITED USE STUDENT .ONLY USE MCT