
Cisco Secure VPN Exam Certification Guide - Cisco press
.pdf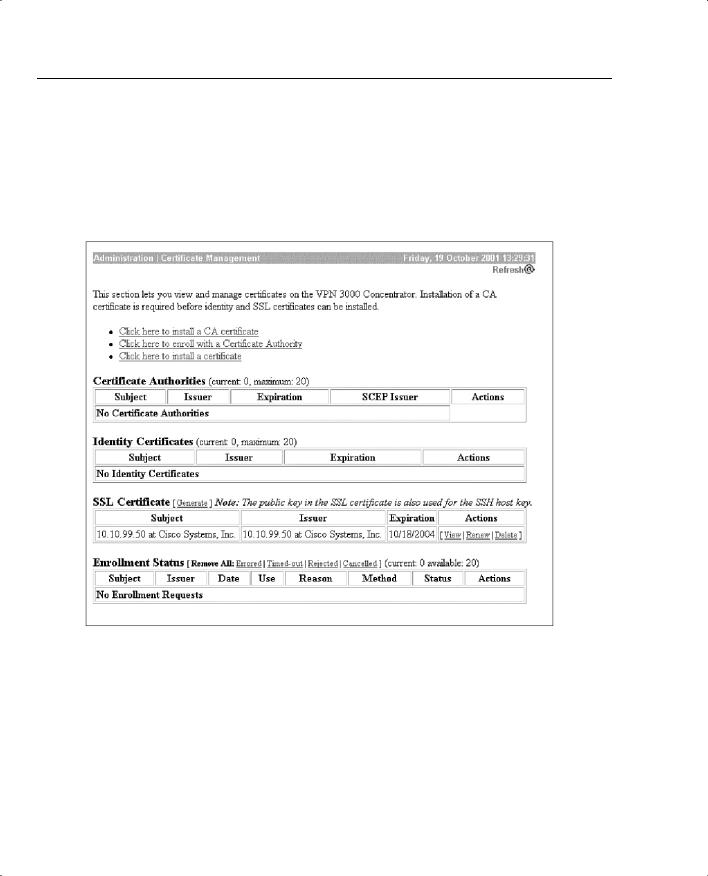
458 Chapter 10: Cisco VPN 3000 LAN-to-LAN with Preshared Keys
Check the Administration | Certificate Management screen to ensure that the certificate appears (see Figure 10-10). This might take a few minutes before being listed, so you might need to refresh the screen a number of times before it will appear. If the certificate does not get listed, make sure that there is connectivity to the server and that you have the correct permissions to access the DLL. Clicking the Click here to install a certificate option will install the certificate.
Figure 10-10 Administration | Certificate Management
Identity Certificate Installation Via SCEP
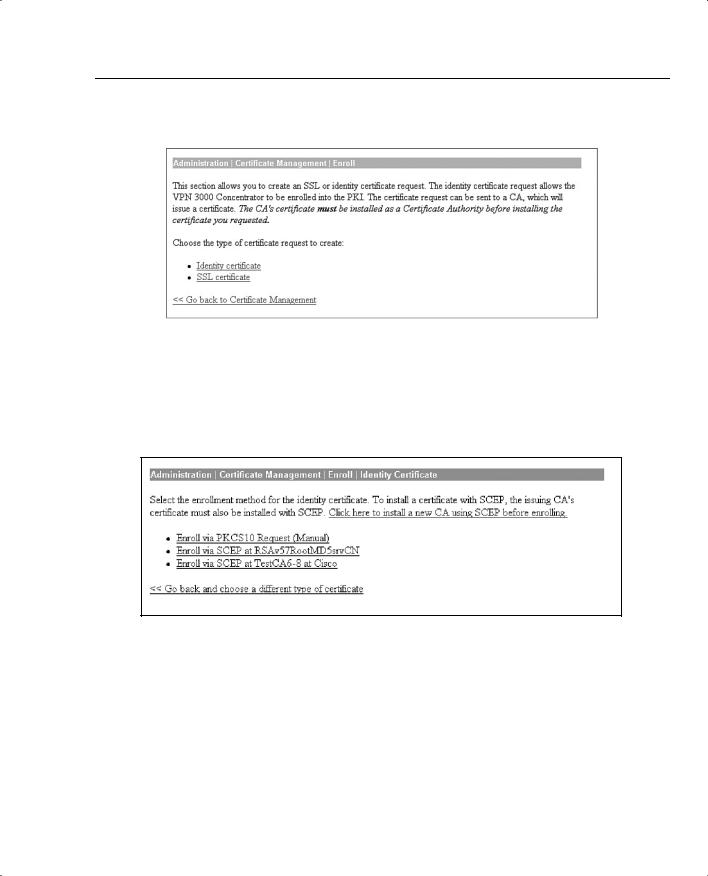
While on the Administration | Certificate Management screen, choose Click here to enroll a with Certificate Authority. You will be transferred to the Administration | Certificate Management | Enroll screen. Choose Identity certificate. As shown in Figure 10-11, this is also where you will go should you choose to use an SSL certificate.
SCEP Overview 459
Figure 10-11 Administration | Certificate Management | Enroll
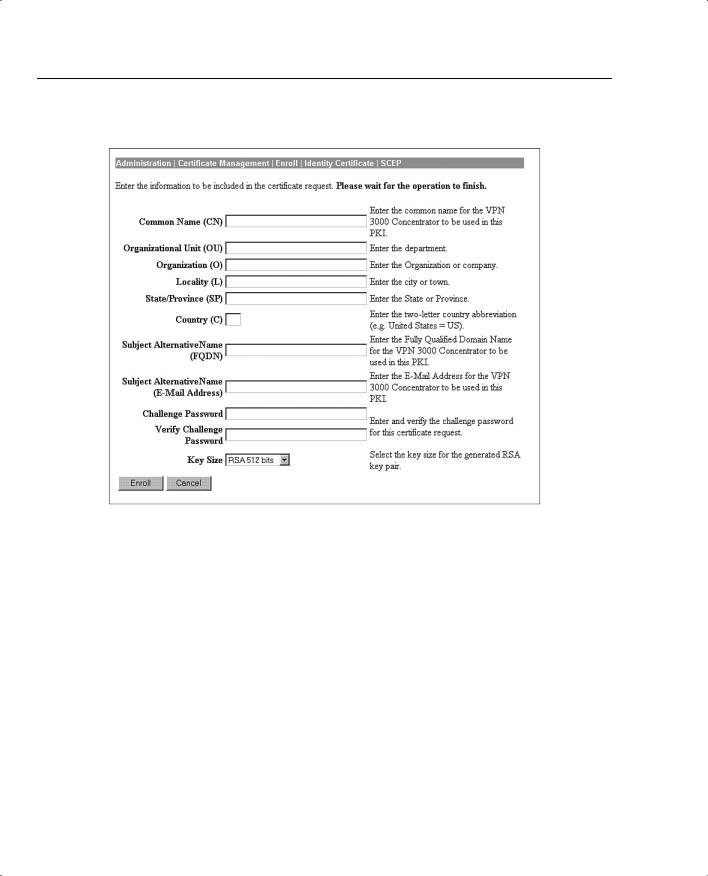
The Administration | Certificate Management | Enroll | Identity Certificate screen is next, shown in Figure 10-12. The title links shown in this screen are dependant upon the text entered in the previous screen. This screen will list all the SCEP certificates obtained. Choose the CA you want to install. This brings you to the Identity Certificate Screen.
Figure 10-12 Administration | Certificate Management | Enroll | Identity Certificate
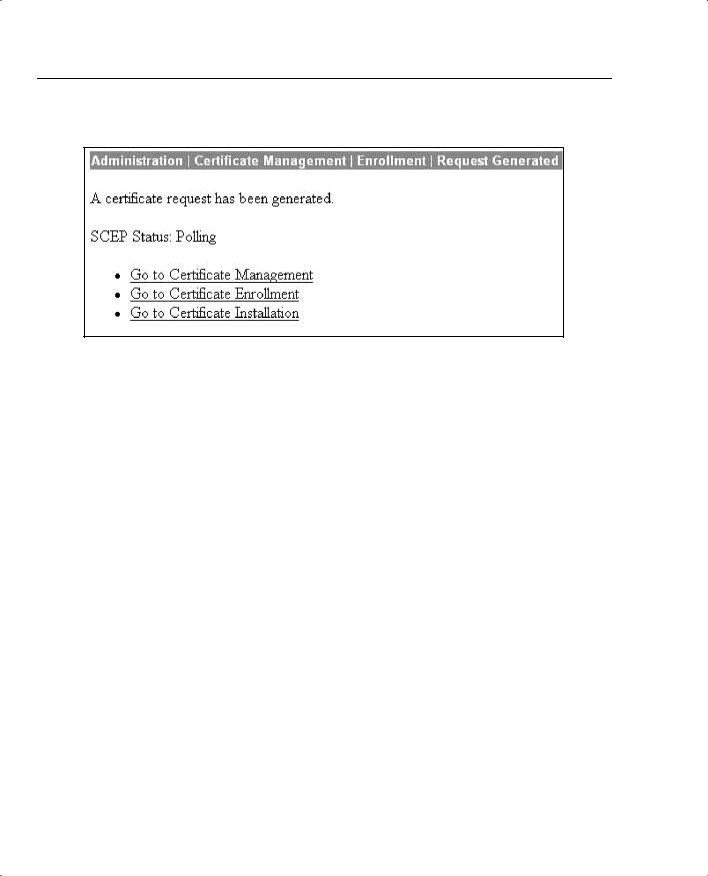
First, fill out the enrollment screen. As shown in Figure 10-13, a large number of variables exist. Table 10-3 addresses these variables.
460 Chapter 10: Cisco VPN 3000 LAN-to-LAN with Preshared Keys
Figure 10-13 Administration | Certificate Management | Enroll | Identity Certificate | SCEP
Table 10-3 Enrollment Variables
Field |
Explanation |
|
|
Common Name (CN) |
The identity associated with the certificate. This is a |
|
mandatory field. If you are using an SSL certificate, the |
|
IP address or domain name used to connect to the VPN |
|
Concentrator is entered. |
|
|
Organizational Unit (OU) |
The OU should match the IPSec group name. Using a |
|
different name than the IPSec group will mean that the |
|
IPSec group used will not have any access. |
|
|
Organization (O) |
Usually the organization’s well-known and common |
|
name. Examples: Cisco Press and Widget Corporation |
|
of America. |
|
|
Locality (L) |
Where the VPN is physically located. Although there is |
|
not a specific requirement, by convention, the city name |
|
where the concentrator is located is entered. Example: |
|
London. |
|
|

|
|
|
SCEP Overview 461 |
|
|
|
|
Table 10-3 Enrollment Variables (Continued) |
|
|
|
|
|
|
|
|
Field |
Explanation |
|
|
|
|
|
|
State/Province (SP) |
The state or province. You should spell out the entire |
|
|
|
state name. |
|
|
|
|
|
|
Country (C) |
The country is entered here. The two-character country |
|
|
|
code must conform to the ISO 3166 country codes. |
|
|
|
|
|
|
Subject Alternative Name (FQDN) |
Enter the FQDN (Fully Qualified Domain Name) here. |
|
|
|
For example: vpn3000.ciscopress.com. |
|
|
|
|
|
|
Subject Alternative Name (E-mail Address) |
Generally used for contacting the system administrator. |
|
|
|
This field is also used for connecting between the |
|
|
|
concentrator and a Cisco router or PIX firewall. |
|
|
|
|
|
|
Challenge Password |
Used when the certificate issuer requires a challenge |
|
|
|
password. |
|
|
|
|
|
|
Verify Challenge Password |
The password is entered twice to ensure that is was |
|
|
|
entered correctly. |
|
|
|
|
|
|
Key Size |
Sets the size of the key used by RSA with SCEP. |
|
|
|
Possible values are |
|
|
|
• |
RSA 512 bits |
|
|
• |
RSA 768 bits |
|
|
• |
RSA 1024 bits |
|
|
• |
RSA 2048 bits |
|
|
The key sizes when using DSA are |
|
|
|
• |
DSA 512 bits |
|
|
• |
DSA 768 bits |
|
|
• |
DSA 1024 bits |
|
|
|
|
Your concentrator will go into a polling state, waiting for the CA server to issue the certificate, as shown in Figure 10-14. On most certificate servers, issuing a certificate is a manual process. Therefore, contact the administrator for the certificate server and request that the certificate be issued.
After the certificate administrator has issued the certificate, check the Administration | Certificate Management screen. The certificate will appear under the Identity Certificates section.
SCEP Overview 463
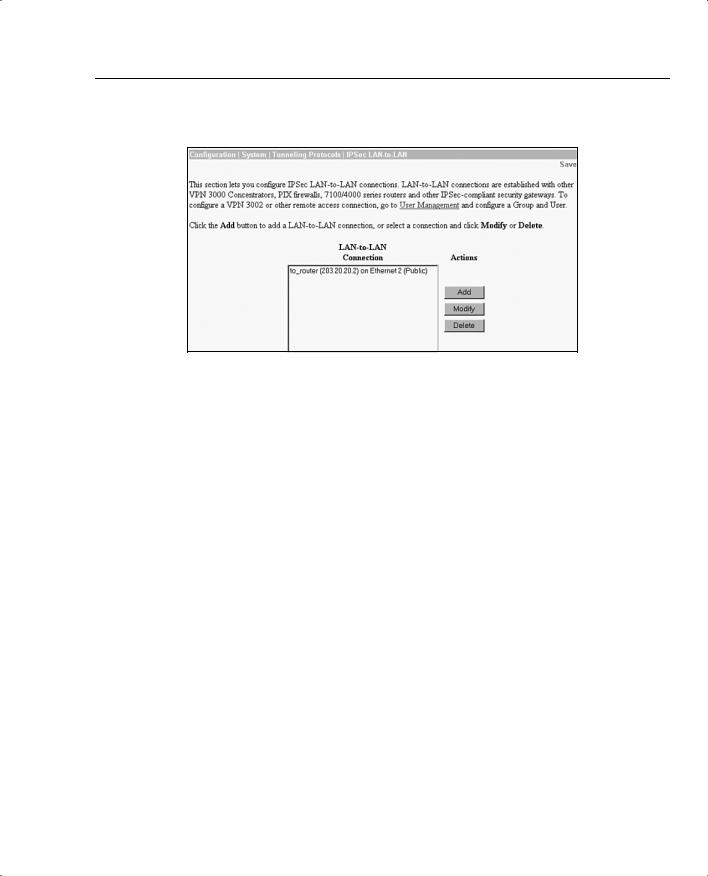
Figure 10-15 Configuration | System | Tunneling Protocols | IPSec LAN-to-LAN
You are taken to the Configuration | System | Tunneling Protocols | IPSec LAN-to-LAN >Modify screen. In this screen, you click the Digital Certificate drop-down menu and choose digital certificate.
On the Certificate Transmission option, you have a choice. If you want to send only the Identity Certificate to the peer, choose Identity certificate only. Choosing Entire certificate chain sends the root and any subordinate certificates to the peer.
Click the IKE Proposal drop-down menu. You will receive a list of all the active IKE proposals. Choose the appropriate proposal. Click the Modify (or Add) button. You will be returned to the Configuration | System | Tunneling Protocols | IPSec LAN-to-LAN screen, as previously shown in Figure 10-15.
You are now using digital certificates for our LAN-to-LAN connection.

464 Chapter 10: Cisco VPN 3000 LAN-to-LAN with Preshared Keys
Foundation Summary
The Foundation Summary is a collection of tables and figures that provides a convenient review of many key concepts in this chapter. For those who are already comfortable with the topics in this chapter, this summary could help you recall a few details. For those who just read this chapter, this review should help solidify some key facts. For anyone doing final preparation before the exam, these tables and figures are a convenient way to review the day before the exam.
Maximum Certificates
Table 10-4 shows the maximum number of certificates allowed.
Table 10-4 Maximum Certificates
Model |
Certificate Limits |
|
|
3005 |
Total of 6 root or subordinate certificates. |
|
Total of 2 identity certificates. |
|
Only a single SSL can be installed. |
|
|
Other models |
Total of 20 root or subordinate certificates. |
|
Total of 20 Identity Certificates. |
|
Only a single SSL can be installed. |
|
|
Enrollment Variables
Table 10-5 explains the enrollment variables that you will see in the Enrollment screen.
Table 10-5 Enrollment Variables
Field |
Explanation |
|
|
Common Name (CN) |
The identity associated with the certificate. This is a |
|
mandatory field. If you are using an SSL certificate, the |
|
IP address or domain name used to connect to the VPN |
|
Concentrator is entered. |
|
|
Organizational Unit (OU) |
The OU should match the IPSec group name. Using a |
|
different name than the IPSec group will mean that the |
|
IPSec group used will not have any access. |
|
|
Organization (O) |
Usually the organization’s well-known and common |
|
name. Examples: Cisco Press and Widget Corporation of |
|
America. |
|
|

|
|
|
Enrollment Variables 465 |
|
|
|
|
Table 10-5 Enrollment Variables (Continued) |
|
|
|
|
|
|
|
|
Field |
Explanation |
|
|
|
|
|
|
Locality (L) |
Where the VPN is physically located. Although there is |
|
|
|
not a specific requirement, by convention, the city name |
|
|
|
where the concentrator is located is entered. Example: |
|
|
|
London. |
|
|
|
|
|
|
State/Province (SP) |
The state or province. You should spell out the entire state |
|
|
|
name. |
|
|
|
|
|
|
Country (C) |
The country is entered here. The two-character country |
|
|
|
code must conform to the ISO 3166 country codes. |
|
|
|
|
|
|
Subject Alternative Name (FQDN) |
Enter the FQDN (Fully Qualified Domain Name) here. |
|
|
|
For example: vpn3000.ciscopress.com. |
|
|
|
|
|
|
Subject Alternative Name (Email Address) |
Generally used for contacting the system administrator. |
|
|
|
This field is also used for connecting between the |
|
|
|
concentrator and A Cisco router or PIX firewall. |
|
|
|
|
|
|
Challenge Password |
Used when the certificate issuer requires a challenge |
|
|
|
password. |
|
|
|
|
|
|
Verify Challenge Password |
The password is entered twice in order to ensure that is |
|
|
|
was entered correctly. |
|
|
|
|
|
|
Key Size |
Sets the size of the key used by RSA. Possible values are |
|
|
|
• |
RSA 512 bits |
|
|
• |
RSA 768 bits |
|
|
• |
RSA 1024 bits |
|
|
• |
RSA 2048 bits |
|
|
The key sizes when using DSA are |
|
|
|
• |
DSA 512 bits |
|
|
• |
DSA 768 bits |
|
|
• |
DSA 1024 bits |
|
|
|
|

466 Chapter 10: Cisco VPN 3000 LAN-to-LAN with Preshared Keys
Chapter Glossary
The following term was introduced in this chapter or has special significance to the topics within this chapter.
Network Autodiscovery A process used on VPN Concentrators to discover networks connected to the remote concentrator. Network Autodiscovery relies on RIP to discover networks.
Q&A 467
Q&A
As mentioned in Chapter 1, these questions are more difficult than what you should experience on the CCSP exam. The questions do not attempt to cover more breadth or depth than the exam; however, the questions are designed to make sure you know the answer. Rather than allowing you to derive the answer from clues hidden inside the question itself, your understanding and recall of the subject are challenged. Questions from the “Do I Know This Already?” quiz from the beginning of the chapter are repeated here to ensure that you have mastered the chapter’s topic areas. Hopefully, these questions will help limit the number of exam questions on which you narrow your choices to two options and guess!
1What is a LAN-to-LAN connection?
2What equipment is required for a LAN-to-LAN connection?
3Where can a LAN-to-LAN connection be used?
4When setting up network lists, how should the lists at each side of the LAN-to-LAN connection relate to each other?
5You attempted to configure a LAN-to-LAN connection, but cannot see a specific network on one side of the connection. What is the most likely problem?
