
- •Contents
- •Preface to second edition
- •1 Introduction
- •1.2 Applying technology in an environment
- •1.3 The human role in systems
- •1.4 Ethical issues
- •1.7 Common practice and good practice
- •1.8 Bugs and emergent phenomena
- •1.10 Knowledge is a jigsaw puzzle
- •1.11 To the student
- •1.12 Some road-maps
- •2 System components
- •2.2 Handling hardware
- •2.3 Operating systems
- •2.4 Filesystems
- •2.5 Processes and job control
- •2.6 Networks
- •2.7 IPv4 networks
- •2.8 Address space in IPv4
- •2.9 IPv6 networks
- •3 Networked communities
- •3.1 Communities and enterprises
- •3.2 Policy blueprints
- •3.4 User behavior: socio-anthropology
- •3.5 Clients, servers and delegation
- •3.6 Host identities and name services
- •3.8 Local network orientation and analysis
- •4 Host management
- •4.1 Global view, local action
- •4.2 Physical considerations of server room
- •4.3 Computer startup and shutdown
- •4.5 Installing a Unix disk
- •4.6 Installation of the operating system
- •4.7 Software installation
- •4.8 Kernel customization
- •5 User management
- •5.1 Issues
- •5.2 User registration
- •5.3 Account policy
- •5.4 Login environment
- •5.5 User support services
- •5.6 Controlling user resources
- •5.7 Online user services
- •5.9 Ethical conduct of administrators and users
- •5.10 Computer usage policy
- •6 Models of network and system administration
- •6.5 Creating infrastructure
- •6.7 Competition, immunity and convergence
- •6.8 Policy and configuration automation
- •7.2 Methods: controlling causes and symptoms
- •7.4 Declarative languages
- •7.6 Common assumptions: clock synchronization
- •7.7 Human–computer job scheduling
- •7.9 Preventative host maintenance
- •7.10 SNMP tools
- •7.11 Cfengine
- •8 Diagnostics, fault and change management
- •8.1 Fault tolerance and propagation
- •8.2 Networks and small worlds
- •8.3 Causality and dependency
- •8.4 Defining the system
- •8.5 Faults
- •8.6 Cause trees
- •8.7 Probabilistic fault trees
- •8.9 Game-theoretical strategy selection
- •8.10 Monitoring
- •8.12 Principles of quality assurance
- •9 Application-level services
- •9.1 Application-level services
- •9.2 Proxies and agents
- •9.3 Installing a new service
- •9.4 Summoning daemons
- •9.5 Setting up the DNS nameservice
- •9.7 E-mail configuration
- •9.8 OpenLDAP directory service
- •9.10 Samba
- •9.11 The printer service
- •9.12 Java web and enterprise services
- •10 Network-level services
- •10.1 The Internet
- •10.2 A recap of networking concepts
- •10.3 Getting traffic to its destination
- •10.4 Alternative network transport technologies
- •10.5 Alternative network connection technologies
- •10.6 IP routing and forwarding
- •10.7 Multi-Protocol Label Switching (MPLS)
- •10.8 Quality of Service
- •10.9 Competition or cooperation for service?
- •10.10 Service Level Agreements
- •11 Principles of security
- •11.1 Four independent issues
- •11.2 Physical security
- •11.3 Trust relationships
- •11.7 Preventing and minimizing failure modes
- •12 Security implementation
- •12.2 The recovery plan
- •12.3 Data integrity and protection
- •12.5 Analyzing network security
- •12.6 VPNs: secure shell and FreeS/WAN
- •12.7 Role-based security and capabilities
- •12.8 WWW security
- •12.9 IPSec – secure IP
- •12.10 Ordered access control and policy conflicts
- •12.11 IP filtering for firewalls
- •12.12 Firewalls
- •12.13 Intrusion detection and forensics
- •13 Analytical system administration
- •13.1 Science vs technology
- •13.2 Studying complex systems
- •13.3 The purpose of observation
- •13.5 Evaluating a hierarchical system
- •13.6 Deterministic and stochastic behavior
- •13.7 Observational errors
- •13.8 Strategic analyses
- •13.9 Summary
- •14 Summary and outlook
- •14.3 Pervasive computing
- •B.1 Make
- •B.2 Perl
- •Bibliography
- •Index
2.8. ADDRESS SPACE IN IPv4 |
63 |
Hardware addresses are cached by each host on the network so that repeated calls to the service ARP translation service are not required. Addresses are checked later however, so that if an address from a host claiming to have a certain IP address originates from an incorrect hardware address (i.e. the packet does not agree with the information in the cache) then this is detected and a warning can be issued to the effect that two devices are trying to use the same IP address. ARP sends out packets on a local network asking the question ‘Who has IP address xxx.yyy.zzz.mmm?’ The host concerned replies with its hardware address.
For hosts which know their own IP address at boot-time these services only serve as confirmations of identity. Diskless clients (which have no place to store their IP address) do not have this information when they are first switched on and need to ask for it. All they know originally is the unique hardware (Ethernet) address which is burned into their network interface. In order to bring up and configure an Internet interface they must first use RARP to find out their IP addresses from a RARP server. Services like BOOTP or DHCP are used for this. Also the Unix file /etc/ethers and rarpd can be used. The ARP protocol has no authentication mechanism, and it is therefore easily poisoned with incorrect data. This can be used by malicious parties to reroute packets to a different destination.
2.8 Address space in IPv4
As we have seen, the current implementation of the Internet protocol has a number of problems. The model of classed Internet addresses was connected to the design of early routing protocols. This has proved to be a poor design decision, leading to a sparse usage of the available addresses.
It is straightforward to calculate that, because of the structure of the IP addresses, divided into class A, B and C networks, something under two percent of the possible addresses can actually be used in practice. A survey from Unix Review in March 1998 showed that, of the total numbers of addresses, these are already allocated:
|
Max possible |
Percent allocated |
Class A |
127 |
100% |
Class B |
16382 |
62% |
Class C |
2097150 |
36% |
Of course, this does not mean that all of the allocated addresses are in active use. After all, what organization has 65,535 hosts? In fact the survey showed that under two percent of these addresses were actually in use. This is an enormous wastage of IP addresses. Amongst the class C networks, where smaller companies would like address space, the available addresses are being used up quickly, but amongst the class A networks, the addresses will probably never be used. A new addressing structure is therefore required to solve this problem. Three solutions have been devised.

64 |
CHAPTER 2. SYSTEM COMPONENTS |
2.8.1Classless addresses (CIDR)
CIDR stands for Classless Inter-Domain Routing and is documented in RFCs 1517, 1518, 1519, and 1520. CIDR was introduced as an interim measure to combat the problems of IP address allocation as well as that of routing table overflow. It is also the strategy of choice for IPv6 addressing. The name refers to inter-domain routing because it provides not only an addressing solution, but also an improved model for routing packets, by defining routing domains (distinct from logical domains of the Domain Name Service).
The IPv4 address space has two problems:
•It is running out of address space, because many addresses are bound up in classes that make them unusable, with the class A,B,C scheme of IP addresses.
•Global routing tables are becoming too large, making routing slow and memory intensive.
In the early 1990s, the limit of routing table size was believed to be somewhere in the order of 100,000 routes. Beyond this, the time it would take for lookup would be longer than TCP/IP timeouts, and the Internet would fail to function. In fact we have already passed this mark [30], but the problem would have been much worse had it not been for classless addressing.
The solution to this problem was a straightforward extension of the idea used in subnetting: to allow the possibility to aggregate or join together smaller networks into larger ones, while at the same time being able to address individual elements within these conglomerates (see table 2.7).
Broadcast flood |
Routing table flood |
Local Area Net |
Wide Area Net |
Subnet mask |
CIDR mask |
Subnet address |
Aggregate network address |
Host address |
Autonomous system number |
(computer) |
(Routing domain) |
|
|
Table 2.7: Analogy between subnetting of hosts and super-netting of routing domains.
The classless IPv4 addresses are identical in concept to addresses and subnet masks. The main change is in notation. A ‘slash’ form is used to represent the number of network bits, instead of another address. This is more compact. For example, the network:
192.0.2.0 , 255.255.255.0 → 192.0.2.0/24
The number of bits that are ‘1’ in the netmask are simply written after the slash. This notation works across any class of address. It respects only power-of- two (bit) boundaries. Thus CIDR addresses no longer refer to any class of network,

2.8. ADDRESS SPACE IN IPv4 |
65 |
only a range of addresses. In order to make this work, new routing protocols were required (such as BGP-4) that did not rely on the simplifications inherent in the classed address scheme.
Address class |
IP prefix |
Network bits |
Hosts bits |
|
|
|
|
Class A |
1–126 |
8 bits |
24 bits |
|
|
|
|
Class B |
128–191 |
16 bits |
16 bits |
|
|
|
|
Class C |
192–224 |
24 bits |
8 bits |
|
|
|
|
Table 2.8: Summary of network classes, and numbers of bits used.
CIDR mask |
Equiv. class C |
Host addresses |
/27 |
1/8th |
32 |
/26 |
1/4th |
64 |
/25 |
1/2 |
128 |
/24 |
1 |
256 |
/23 |
2 |
512 |
/22 |
4 |
1,024 |
/21 |
8 |
2,048 |
/20 |
16 |
4,096 |
/19 |
32 |
8,192 |
/18 |
64 |
16,384 |
/17 |
128 |
32,768 |
/16 |
256 = 1 class B |
65,536 |
/15 |
512 |
131,072 |
/14 |
1,024 |
262,144 |
/13 |
2,048 |
524,288 |
|
|
|
Table 2.9: Examples of bit usage in generalized classless addresses.
Table 2.8 shows the bit usage of the original IPv4 address classes, and table 2.9 shows how the concept of network part and host part is generalized by the classless addressing scheme. Notice how, at this stage, this is nothing more than a change of notation. The importance of the change, however, lies in the ability to combine or aggregate addresses with a common prefix. Routing authorities that support CIDR are hierarchically organized. Each bit boundary that
66 |
CHAPTER 2. SYSTEM COMPONENTS |
distinguishes a different network must be responsible for its own administration, so that the level above can simply refer to all its IP sub-ranges in one table entry.
2.8.2Routing domains or Autonomous Systems
Having made a more general split between the network part and host part of an IP address, one can associate a general network prefix with all the hosts in a block of addresses, provided one refers to a block by a bit-boundary. It is now easier to make a generalized hierarchy of ‘containers within containers’, making each organization responsible for its own internal routing.
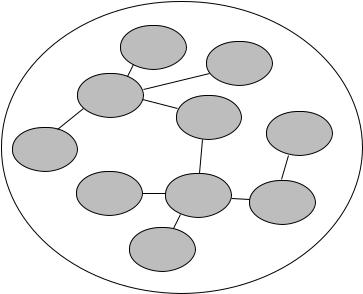
An Autonomous System (AS) (sometimes called a routing domain) is a set of routers under a single administrative umbrella, that is responsible for its own internal routing, but which needs to exchange data along exterior or border routes between itself and other autonomous systems. Within the AS, interior routing protocols are used; between ASs, border protocols are used, e.g. the Border Gateway Protocol (version 4 supports CIDR) (see figure 2.10).
AS4813
AS6
AS3266
AS4571
AS887
AS877
AS86 |
AS2 |
|
AS67 |
AS1
Figure 2.10: The Internet is made up of top-level autonomous systems. These are not necessarily related to the ‘Top Level Domains’, like .com and .net.
In routing tables, CIDR address boundaries are used to represent aggregated containers, i.e. the largest container that contains all of the hosts one is interested in. In general, this aggregate address boundary will also contain more than one is interested in, so there must be a way of restricting traffic to parts within the aggregate address. As with subnetting of hosts, the routers within the aggregate container only pay attention to data if they are addressed to them, using an ‘Autonomous System Number’ (ASN). The ASN of a routing domain is analogous to
2.8. ADDRESS SPACE IN IPv4 |
67 |
a ‘host’ address on a Local Area Network, and it requires that each border router knows its ASN identity.
Currently, blocks of addresses are assigned to the large Internet Service Providers (ISPs) who then allocate portions of their address blocks to their customers. These customers, who are often smaller ISPs themselves, then distribute portions of their address block to their customers. Because of the bit-structure in the top-level global routing tables all these different networks and hosts can be represented by the single Internet route entry for the largest container. In this way, the growth in the number of routing table entries at each level in the network hierarchy has been significantly reduced.
In the past, one would get a Class A, B or C address assignment directly from the appropriate Internet Registry (i.e. the InterNIC). Under this scenario, one ‘owned’ the address and could continue to use it even in the event of changing Internet Service Providers (ISPs). However, this would break the CIDR scheme that allows route aggregation. Thus the new model for address assignments is to obtain them from a ‘greater’ ISP in the hierarchy of which the system is a part.
At the time of writing, the global routing tables have approximately 120,000 entries. There are 22,000 assigned Autonomous Systems, of which about half are active.
2.8.3Network Address Translation
In order to provide a ‘quick fix’ for organizations that required only partial connectivity, Network Address Translation (NAT) was introduced by a number of router manufacturers [331]. In a NAT, a network is represented to the outside world by a single official IP address; it shields the remainder of its networked machines on a private network that (hopefully) uses non-routable addresses (usually 10.x.x.x). When one of these hosts on the private network attempts to contact an address on the Internet, the Network Address Translator creates the illusion that the request comes from the single representative address. The return data are, in turn, routed back to the particular host ‘as if by magic’ (see figure 2.11). NAT makes associations of this form:
(private IP, private port) <-> (public IP, public port)
It is important that the outside world (i.e. the true Internet) should not be able to see the private addresses behind a NAT. Using a private address in a public IP address is not just bad manners, it could quickly spoil routing protocols and preclude us from being able to send to the real owners of those addresses. NATs are often used in conjunction with a firewall.
Network address translation is a quick and cheap solution to giving many computers access to the Internet, but it has many problems. The most serious, perhaps, is that it breaks certain IP security mechanisms that rely on IP addresses, because IP addresses are essentially spoofed. Thus some network services will not run through a NAT, because the data stream looks as though it has been forged. Indeed, it has.
