
CCNP 642-811 BCMSN Exam Certification Guide - Cisco press
.pdf
This chapter covers the following topics that you need to master for the CCNP BCMSN exam:
■Virtual LANs—This section reviews VLANs, VLAN membership, and VLAN configuration on a Catalyst switch.
■VLAN Trunks—This section covers transporting multiple VLANs over single links and VLAN trunking with Ethernet.
■VLAN Trunk Configuration—This section outlines the Catalyst switch commands that configure VLAN trunks.
■Service Provider Tunneling—This section covers IEEE 802.1Q (Q-in-Q) and Layer 2 Protocol tunnels for transporting customer trunks across a service provider network.
■Ethernet over MPLS Tunneling—This section discusses tunneling Ethernet frames across an MPLS core network
■Troubleshooting VLANs and Trunks—
This section provides commands to use when a VLAN or trunk is not operating properly.
C H A P T E R 6
VLANs and Trunks
Switched campus networks can be broken up into distinct broadcast domains or virtual LANs (VLANs). A flat network topology, or a network with a single broadcast domain, can be simple to implement and manage. However, flat network topology is not scalable. Instead, the campus can be divided into segments using VLANs, while Layer 3 routing protocols manage interVLAN communication.
This chapter details the process of defining common workgroups within a group of switches. It covers switch configuration for VLANs, along with the method of identifying and transporting VLANs on various types of links.
”Do I Know This Already?” Quiz
The purpose of the “Do I Know This Already?” quiz is to help you decide if you need to read the entire chapter. If you already intend to read the entire chapter, you do not necessarily need to answer these questions now.
The 12-question quiz, derived from the major sections in the “Foundation Topics” portion of the chapter, helps you determine how to spend your limited study time.
Table 6-1 outlines the major topics discussed in this chapter and the “Do I Know This Already?” quiz questions that correspond to those topics.
Table 6-1 “Do I Know This Already?” Foundation Topics Section-to-Question Mapping
Foundation Topics Section |
Questions Covered in This Section |
|
|
Virtual LANs |
1–4 |
|
|
VLAN Trunks |
5-10 |
VLAN Trunk Configuration |
|
|
|
Q-in-Q Tunneling |
11-12 |
|
|
138 Chapter 6: VLANs and Trunks
CAUTION The goal of self-assessment is to gauge your mastery of the topics in this chapter. If you do not know the answer to a question or are only partially sure of the answer, you should mark this question wrong. Giving yourself credit for an answer you correctly guess skews your selfassessment results and might give you a false sense of security.
1.A VLAN is which of the following?
a.Collision domain
b.Spanning Tree domain
c.Broadcast domain
d.VTP domain
2.Switches provide VLAN connectivity at which layer of the OSI model?
a.Layer 1
b.Layer 2
c.Layer 3
d.Layer 4
3.Which one of the following is needed to pass data between two PCs, each connected to a different VLAN?
a.A Layer 2 switch
b.A Layer 3 switch
c.A trunk
d.A tunnel
4.Which switch command is used to assign a port to a VLAN?
a.access vlan vlan-id
b.switchport access vlan vlan-id
c.vlan vlan-id
d.set port vlan vlan-id

”Do I Know This Already?” Quiz 139
5.Which of the following is a standardized method of trunk encapsulation?
a.802.1d
b.802.1Q
c.802.3z
d.802.1a
6.What is the Cisco proprietary method for trunk encapsulation?
a.CDP
b.EIGRP
c.ISL
d.DSL
7.Which of these protocols dynamically negotiates trunking parameters?
a.PAgP
b.STP
c.CDP
d.DTP
8.How many different VLANs can an 802.1Q trunk support?
a.256
b.1024
c.4096
d.32,768
e.65,536
9.Which of the following incorrectly describes a native VLAN?
a.Frames are untagged on an 802.1Q trunk.
b.Frames are untagged on an ISL trunk.
c.Frames can be interpreted by a nontrunking host.
d.The native VLAN can be configured for each trunking port.

140Chapter 6: VLANs and Trunks
10.If two switches each support all types of trunk encapsulation on a link between them, which one will be negotiated?
a.ISL
b.802.1Q
c.DTP
d.VTP
11.Which answer gives the purpose of an 802.1Q tunnel?
a.Encrypting the data on an 802.1Q trunk
b.Passing an ISL trunk across an 802.1Q domain
c.Transporting an 802.1Q trunk across a service provider network
d.Transporting an 802.1Q trunk across an ISL domain
12.What types of protocols cannot be tunneled by a Layer 2 Protocol Tunnel?
a.TCP
b.CDP
c.STP
d.VTP
The answers to the quiz are found in Appendix A, “Answers to Chapter ‘Do I Know This Already?’ Quizzes and Q&A Sections.” The suggested choices for your next step are as follows:
■6 or less overall score—Read the entire chapter. This includes the “Foundation Topics,” “Foundation Summary,” and “Q&A” sections.
■7–9 overall score—Begin with the “Foundation Summary” section and then follow with the “Q&A” section at the end of the chapter.
■10 or more overall score—If you want more review on these topics, skip to the “Foundation Summary” section and then go to the “Q&A” section at the end of the chapter. Otherwise, move on to Chapter 7, “VLAN Trunking Protocol (VTP).”
Virtual LANs 141
Foundation Topics
Virtual LANs
Consider a network design that consists of Layer 2 devices only. For example, this design could be a single Ethernet segment, an Ethernet switch with many ports, or a network with several interconnected Ethernet switches. A full Layer 2-only switched network is referred to as a flat network topology. A flat network is a single broadcast domain, such that every connected device sees every broadcast packet that is transmitted. As the number of stations on the network increases, so does the number of broadcasts.
Due to the Layer 2 foundation, flat networks cannot contain redundant paths for load-balancing or fault tolerance. The reason for this is explained in Chapters 9 through 12. To gain any advantage from additional paths to a destination, Layer 3 routing functions must be introduced.
A switched environment offers the technology to overcome flat network limitations. Switched networks can be subdivided into VLANs. By definition, a VLAN is a single broadcast domain. All devices connected to the VLAN receive broadcasts from other VLAN members. However, devices connected to a different VLAN will not receive those same broadcasts. (Naturally, VLAN members also receive unicast packets directed toward them from other VLAN members.)
A VLAN consists of defined members communicating as a logical network segment. In contrast, a physical segment consists of devices that must be connected to a physical cable segment. A VLAN can have connected members located anywhere in the campus network, as long as VLAN connectivity is provided between all members. Layer 2 switches are configured with a VLAN mapping and provide the logical connectivity between the VLAN members.
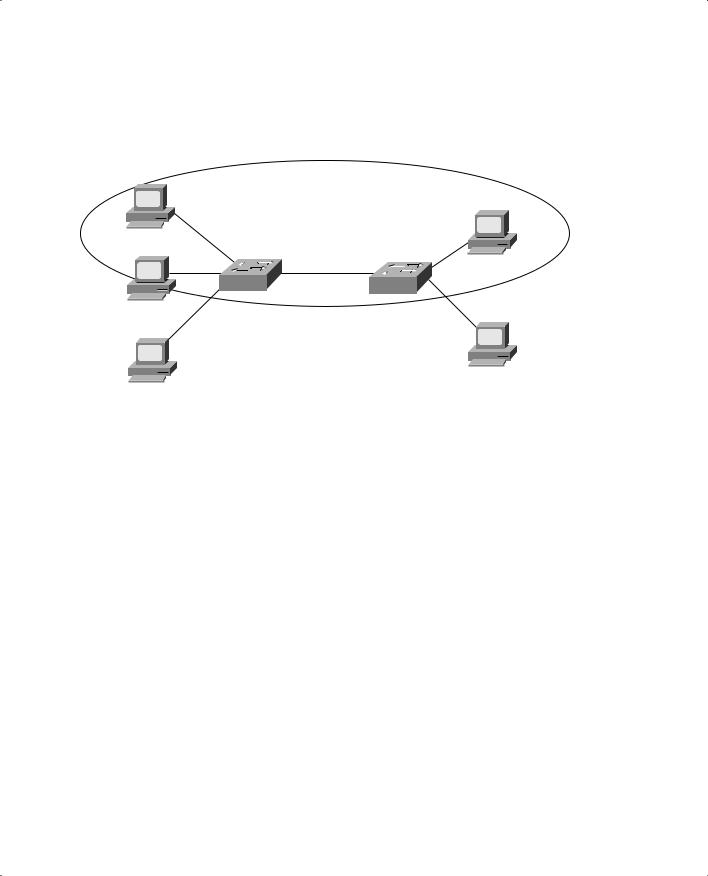
Figure 6-1 shows how a VLAN can provide logical connectivity between switch ports. Two workstations on the left Catalyst switch are assigned to VLAN 1, while a third workstation is assigned to VLAN 100. In this example, no communication can occur between VLAN 1 and VLAN 100. Both ends of the link between the Catalysts are assigned to VLAN 1. One workstation on the right Catalyst is also assigned to VLAN 1. Because there is end-to-end connectivity of VLAN 1, any of the workstations on VLAN 1 can communicate as if they were connected to a physical network segment.
142 Chapter 6: VLANs and Trunks
Figure 6-1 VLAN Functionality
VLAN 1 connectivity
VLAN 1
VLAN 1
VLAN 1
VLAN 1
VLAN 200
VLAN 100
VLAN Membership
When a VLAN is provided at an access layer switch, an end user must have some means to gain membership to it. Two membership methods exist on Cisco Catalyst switches:
■Static VLAN Configuration
■Dynamic VLAN Assignment
Static VLANs
Static VLANs offer port-based membership, where switch ports are assigned to specific VLANs. End user devices become members in a VLAN based on the physical switch port to which they are connected. No handshaking or unique VLAN membership protocol is needed for the end devices; they automatically assume VLAN connectivity when they connect to a port. Normally, the end device is not even aware that the VLAN exists. The switch port and its VLAN are simply viewed and used as any other network segment, with other “locally attached” members on the wire.
Switch ports are assigned to VLANs by the manual intervention of the network administrator, hence the static nature. Each port receives a Port VLAN ID (PVID) that associates it with a VLAN number. The ports on a single switch can be assigned and grouped into many VLANs. Even though two devices are connected to the same switch, traffic will not pass between them if they are connected to ports on different VLANs. To perform this function, you could use either a Layer 3 device to route packets or an external Layer 2 device to bridge packets between the two VLANs.
Virtual LANs 143
The static port-to-VLAN membership is normally handled in hardware with application-specific integrated circuits (ASICs) in the switch. This membership provides good performance because all port mappings are done at the hardware level with no complex table lookups needed.
Configuring Static VLANs
This section describes the switch commands needed to configure static VLANs. By default, all switch ports are assigned to VLAN 1, are set to be a VLAN type of Ethernet, and have a maximum transmission unit (MTU) size of 1500 bytes.
First, the VLAN must be created on the switch, if it does not already exist. Then, the VLAN must be assigned to specific switch ports.
To configure static VLANs, you can first define the VLAN with the following command in global configuration mode:
Switch(config)# vlan vlan-num
Switch(config-vlan)# name vlan-name
The VLAN is created and stored in a database, along with its number and a descriptive name. The VLAN database is automatically stored in a special vlan.dat file in Flash memory, separate from the switch configuration.
Next, you should assign one or more switch ports to the VLAN. Use the following configuration commands:
Switch(config)# interface type module/number
Switch(config-if)# switchport mode access
Switch(config-if)# switchport access vlan vlan-num
The switchport access vlan command configures the port for static VLAN membership, according to the VLAN number given by vlan-num (1 to 1005). The range of VLAN numbers can be 1 to 4094 if the switch is configured in VTP transparent mode. To verify VLAN configuration, use the show vlan command to output a list of all VLANs defined in the switch, in addition to the ports assigned to each VLAN. Example 6-1 shows some sample output from the show vlan command.
Example 6-1 Verifying VLAN Configuration with show vlan Command
Switch# show vlan |
|
|
|
|
VLAN |
Name |
Status |
Ports |
|
---- |
-------------------------------- |
--------- |
------------------------------- |
|
1 |
default |
active |
Gi1/1, Gi1/2, Gi3/20, Gi4/20 |
|
2 |
Engineering |
active |
Gi4/2, Gi4/3, Gi4/4, Gi4/5 |
|
|
|
|
Gi4/6, Gi4/7, Gi4/8, Gi4/9 |
|
|
|
|
Gi4/10, Gi4/11, |
Gi4/12 |
continues
144 Chapter 6: VLANs and Trunks
Example 6-1 Verifying VLAN Configuration with show vlan Command (Continued)
101 Marketing |
active |
Gi2/5, Gi2/6, Gi2/7, Gi2/8 |
Gi2/9, Gi2/10, Gi2/11, Gi2/12
Gi2/13, Gi2/14, Gi2/15, Gi2/16
Gi2/17, Gi2/18
Dynamic VLANs
Dynamic VLANs provide membership based on the MAC address of an end user device. When a device is connected to a switch port, the switch must, in effect, query a database to establish VLAN membership. A network administrator must assign the user’s MAC address to a VLAN in the database of a VLAN Membership Policy Server (VMPS).
With Cisco switches, dynamic VLANs are created and managed using network management tools such as CiscoWorks 2000. Dynamic VLANs allow a great deal of flexibility and mobility for end users but require more administrative overhead.
NOTE Dynamic VLANs are not covered in this text or in the BCMSN course or exam (at press time). For more information, refer to “Configuring VMPS” at
www.cisco.com/univercd/cc/td/doc/product/lan/c3550/12112cea/3550scg/swvlan.htm#xtocid35.
Deploying VLANs
To implement VLANs, you must consider the number of VLANs you need and how best to place them. As usual, the number of VLANs will be dependent on traffic patterns, application types, segmenting common workgroups, and network management requirements.
An important factor to consider is the relationship between VLANs and the IP addressing schemes used. Cisco recommends a one-to-one correspondence between VLANs and IP subnets. This recommendation means that if a subnet with a 24-bit mask is used for a VLAN, no more than
254 devices should be in the VLAN. In addition, VLANs not extending beyond the Layer 2 domain of the distribution switch is recommended. In other words, the VLAN should not reach across a network’s core and into another switch block. The idea again is to keep broadcasts and unnecessary traffic movement out of the core block.
VLANs can be scaled in the switch block by using two basic methods:
■End-to-end VLANs
■Local VLANs

Virtual LANs 145
End-to-End VLANs
End-to-end VLANs, also called campus-wide VLANs, span the entire switch fabric of a network. They are positioned to support maximum flexibility and mobility of end devices. Users are assigned to VLANs regardless of physical location. As a user moves around the campus, that user’s VLAN membership stays the same. This means that each VLAN must be made available at the access layer in every switch block.
End-to-end VLANs should group users according to common requirements. All users in a VLAN should have roughly the same traffic flow patterns, following the 80/20 rule. Recall that this rule estimates that 80 percent of user traffic stays within the local workgroup, while 20 percent is destined for a remote resource in the campus network. Although only 20 percent of the traffic in a VLAN is expected to cross the network core, end-to-end VLANs make it possible for all traffic within a single VLAN to cross the core.
Because all VLANs must be available at each access layer switch, VLAN trunking must be used to carry all VLANs between the access and distribution layer switches.
NOTE End-to-end VLANs are not recommended in an enterprise network, unless there is a good reason. Broadcast traffic must be carried over a VLAN from one end of the network to the other. For this reason, a broadcast storm or Layer 2 bridging loop can also spread across the extent of a VLAN, exhausting the bandwidth of distribution and core layer links, as well as switch CPU resources. When such a problem occurs, troubleshooting becomes more difficult. In other words, the risks of end-to-end VLANs outweigh the convenience and benefits.
Local VLANs
Because most enterprise networks have moved toward the 20/80 rule (where server and intranet/ Internet resources are centralized), end-to-end VLANs have become cumbersome and difficult to maintain. The 20/80 rule reverses the traffic pattern of the end-to-end VLAN—only 20 percent of traffic is local, while 80 percent is destined to a remote resource across the core layer. End users require access to central resources outside their VLAN. Users must cross into the network core more frequently. In this type of network, VLANs are designed to contain user communities based on geographic boundaries, with little regard to the amount of traffic leaving the VLAN.
Local or geographic VLANs range in size from a single switch in a wiring closet to an entire building. Arranging VLANs in this fashion enables the Layer 3 function in the campus network to intelligently handle the interVLAN traffic loads. This scenario provides maximum availability by using multiple paths to destinations, maximum scalability by keeping the VLAN within a switch block, and maximum manageability.
