
Advanced PHP Programming
.pdf


Caching in a Distributed Environment |
381 |
To achieve this, you can use Spread, a group communication toolkit designed at the Johns Hopkins University Center for Networking and Distributed Systems to provide an extremely efficient means of multicast communication between services in a cluster with robust ordering and reliability semantics. Spread is not a distributed application in itself; it is a toolkit (a messaging bus) that allows the construction of distributed applications.
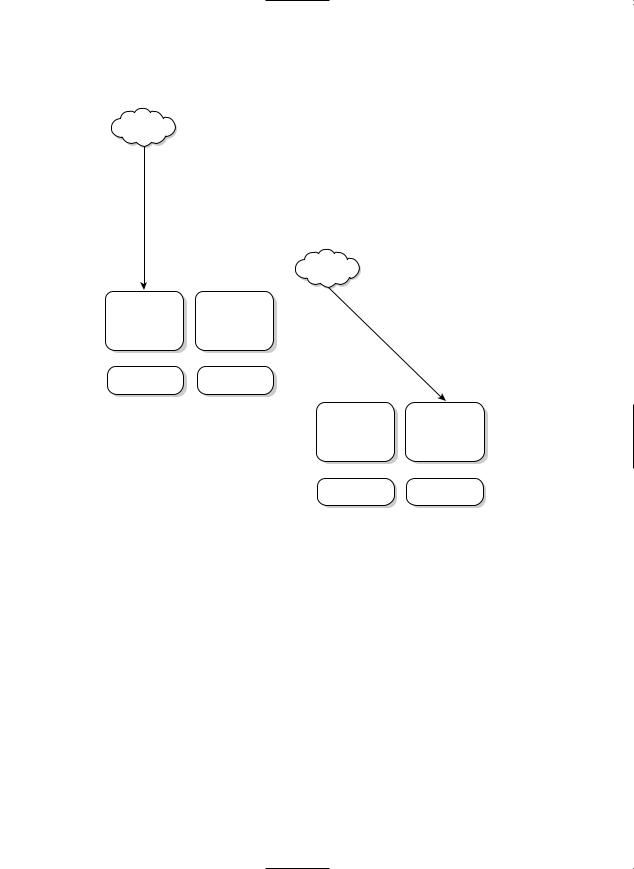
The basic architecture plan is shown in Figure 15.8. Cache files will be written in a nonversioned fashion locally on every machine.When an update to the cached data occurs, the updating application will send a message to the cache Spread group. On every machine, there is a daemon listening to that group.When a cache invalidation request comes in, the daemon will perform the cache invalidation on that local machine.
|
|
|
|
|
|
|
|
|
|
|
|
Figure 15.8 A simple Spread ring.
This methodology works well as long as there are no network partitions. A network partition event occurs whenever a machine joins or leaves the ring. Say, for example, that a machine crashes and is rebooted. During the time it was down, updates to cache entries may have changed. It is possible, although complicated, to build a system using Spread whereby changes could be reconciled on network rejoin. Fortunately for you, the nature of most cached information is that it is temporary and not terribly painful to re-create. You can use this assumption and simply destroy the cache on a Web server whenever the cache maintenance daemon is restarted.This measure, although draconian, allows you to easily prevent usage of stale data.

382 Chapter 15 Building a Distributed Environment
To implement this strategy, you need to install some tools.To start with, you need to download and install the Spread toolkit from www.spread.org. Next, you need to install the Spread wrapper from PEAR:
# pear install spread
The Spread wrapper library is written in C, so you need all the PHP development tools installed to compile it (these are installed when you build from source). So that you can avoid having to write your own protocol, you can use XML-RPC to encapsulate your purge requests.This might seem like overkill, but XML-RPC is actually an ideal choice: It is much lighter-weight than a protocol such as SOAP, yet it still provides a relatively extensible and “canned” format, which ensures that you can easily add clients in other languages if needed (for example, a standalone GUI to survey and purge cache files).
To start, you need to install an XML-RPC library.The PEAR XML-RPC library works well and can be installed with the PEAR installer, as follows:
# pear install XML_RPC
After you have installed all your tools, you need a client.You can augment the class by using a method that allows for purging data:
require_once ‘XML/RPC.php’;
class Cache_File_Spread extends File { private $spread;
Spread works by having clients attach to a network of servers, usually a single server per machine. If the daemon is running on the local machine, you can simply specify the port that it is running on, and a connection will be made over a Unix domain socket.The default Spread port is 4803:
private $spreadName = ‘4803’;
Spread clients join groups to send and receive messages on. If you are not joined to a group, you will not see any of the messages for it (although you can send messages to a group you are not joined to). Group names are arbitrary, and a group will be automatically created when the first client joins it.You can call your group xmlrpc:
private $spreadGroup = ‘xmlrpc’;
private $cachedir = ‘/cache/’;
public function _ _construct($filename, $expiration=false)
{
parent::_ _construct($filename, $expiration);
You create a new Spread object in order to have the connect performed for you automatically:
$this->spread = new Spread($this->spreadName);
}

Caching in a Distributed Environment |
383 |
Here’s the method that does your work.You create an XML-RPC message and then send it to the xmlrpc group with the multicast method:
function purge()
{
//We don’t need to perform this unlink,
//our local spread daemon will take care of it.
//unlink(“$this->cachedir/$this->filename”);
$params = array($this->filename);
$client = new XML_RPC_Message(“purgeCacheEntry”, $params); $this->spread->multicast($this->spreadGroup, $client->serialize());
}
}
}
Now, whenever you need to poison a cache file, you simply use this:
$cache->purge();
You also need an RPC server to receive these messages and process them:
require_once ‘XML/RPC/Server.php’; $CACHEBASE = ‘/cache/’; $serverName = ‘4803’;
$groupName = ‘xmlrpc’;
The function that performs the cache file removal is quite simple.You decode the file to be purged and then unlink it.The presence of the cache directory is a half-hearted attempt at security. A more robust solution would be to use chroot on it to connect it to the cache directory at startup. Because you’re using this purely internally, you can let this slide for now. Here is a simple cache removal function:
function purgeCacheEntry($message) {
global $CACHEBASE;
$val = $message->params[0];
$filename = $val->getval(); unlink(“$CACHEBASE/$filename”);
}
Now you need to do some XML-RPC setup, setting the dispatch array so that your server object knows what functions it should call:
$dispatches = array( ‘purgeCacheEntry’ =>
array(‘function’ => ‘purgeCacheEntry’));
$server = new XML_RPC_Server($dispatches, 0);
Now you get to the heart of your server.You connect to your local Spread daemon, join the xmlrpc group, and wait for messages.Whenever you receive a message, you call the server’s parseRequest method on it, which in turn calls the appropriate function (in this case, purgeCacheEntry):

384Chapter 15 Building a Distributed Environment
$spread = new Spread($serverName); $spread->join($groupName); while(1) {
$message = $spread->receive(); $server->parseRequest($data->message);
}
Scaling Databases
One of the most difficult challenges in building large-scale services is the scaling of databases.This applies not only to RDBMSs but to almost any kind of central data store.The obvious solution to scaling data stores is to approach them as you would any other service: partition and cluster. Unfortunately, RDBMSs are usually much more difficult to make work than other services.
Partitioning actually works wonderfully as a database scaling method.There are a number of degrees of portioning. On the most basic level, you can partition by breaking the data objects for separate services into distinct schemas. Assuming that a complete (or at least mostly complete) separation of the dependant data for the applications can be achieved, the schemas can be moved onto separate physical database instances with no problems.
Sometimes, however, you have a database-intensive application where a single schema sees so much DML (Data Modification Language—SQL that causes change in the database) that it needs to be scaled as well. Purchasing more powerful hardware is an easy way out and is not a bad option in this case. However, sometimes simply buying larger hardware is not an option:
nHardware pricing is not linear with capacity. High-powered machines can be very expensive.
nI/O bottlenecks are hard (read expensive) to overcome.
nCommercial applications often run on a per-processor licensing scale and, like hardware, scale nonlinearly with the number of processors. (Oracle, for instance, does not allow standard edition licensing on machines that can hold more than four processors.)
Common Bandwidth Problems
You saw in Chapter 12, “Interacting with Databases,” that selecting more rows than you actually need can result in your queries being slow because all that information needs to be pulled over the network from the RDBMS to the requesting host. In high-volume applications, it’s very easy for this query load to put a significant strain on your network. Consider this: If you request 100 rows to generate a page and your average row width is 1KB, then you are pulling 100KB of data across your local network per page. If that page is requested 100 times per second, then just for database data, you need to fetch 100KB × 100 = 10MB of data per second. That’s bytes, not bits. In bits, it is 80Mbps. That will effectively saturate a 100Mb Ethernet link.

Scaling Databases |
385 |
This example is a bit contrived. Pulling that much data over in a single request is a sure sign that you are doing something wrong—but it illustrates the point that it is easy to have back-end processes consume large amounts of bandwidth. Database queries aren’t the only actions that require bandwidth. These are some other traditional large consumers:
nNetworked file systems—Although most developers will quickly recognize that requesting 100KB of data per request from a database is a bad idea, many seemingly forget that requesting 100KB files over NFS or another network file system requires just as much bandwidth and puts a huge strain on the network.
nBackups—Backups have a particular knack for saturating networks. They have almost no computational overhead, so they are traditionally network bound. That means that a backup system will easily grab whatever bandwidth you have available.
For large systems, the solution to these ever-growing bandwidth demands is to separate out the large consumers so that they do not step on each other. The first step is often to dedicate separate networks to Web traffic and to database traffic. This involves putting multiple network cards in your servers. Many network switches support being divided into multiple logical networks (that is, virtual LANs [VLANs]). This is not technically necessary, but it is more efficient (and secure) to manage. You will want to conduct all Web traffic over one of these virtual networks and all database traffic over the other. Purely internal networks (such as your database network) should always use private network space. Many load balancers also support network address translation, meaning that you can have your Web traffic network on private address space as well, with only the load balancer bound to public addresses.
As systems grow, you should separate out functionality that is expensive. If you have a network-available backup system, putting in a dedicated network for hosts that will use it can be a big win. Some systems may eventually need to go to Gigabit Ethernet or trunked Ethernet. Backup systems, high-throughput NFS servers, and databases are common applications that end up being network bound on 100Mb Ethernet networks. Some Web systems, such as static image servers running high-speed Web servers such as Tux or thttpd can be network bound on Ethernet networks.
Finally, never forget that the first step in guaranteeing scalability is to be careful when executing expensive tasks. Use content compression to keep your Web bandwidth small. Keep your database queries small. Cache data that never changes on your local server. If you need to back up four different databases, stagger the backups so that they do not overlap.
There are two common solutions to this scenario: replication and object partitioning. Replication comes in the master/master and master/slave flavors. Despite what any
vendor might tell you to in order to sell its product, no master/master solution currently performs very well. Most require shared storage to operate properly, which means that I/O bottlenecks are not eliminated. In addition, there is overhead introduced in keeping the multiple instances in sync (so that you can provide consistent reads during updates).
The master/master schemes that do not use shared storage have to handle the overhead of synchronizing transactions and handling two-phase commits across a network (plus the read consistency issues).These solutions tend to be slow as well. (Slow here is a relative term. Many of these systems can be made blazingly fast, but not as fast as a

386 Chapter 15 Building a Distributed Environment
doubly powerful single system and often not as powerful as a equally powerful single system.)
The problem with master/master schemes is with write-intensive applications.When a database is bottlenecked doing writes, the overhead of a two-phase commit can be crippling.Two-phase commit guarantees consistency by breaking the commit into two phases:
n The promissory phase, where the database that the client is committing to requests all its peers to promise to perform the commit.
n The commit phase, where the commit actually occurs.
As you can probably guess, this process adds significant overhead to every write operation, which spells trouble if the application is already having trouble handling the volume of writes.
In the case of a severely CPU-bound database server (which is often an indication of poor SQL tuning anyway), it might be possible to see performance gains from clustered systems. In general, though, multimaster clustering will not yield the performance gains you might expect.This doesn’t mean that multimaster systems don’t have their uses.They are a great tool for crafting high-availability solutions.
That leaves us with master/slave replication. Master/slave replication poses fewer technical challenges than master/master replication and can yield good speed benefits. A critical difference between master/master and master/slave setups is that in master/master architectures, state needs to be globally synchronized. Every copy of the database must be in complete synchronization with each other. In master/slave replication, updates are often not even in real-time. For example, in both MySQL replication and Oracle’s snap- shot-based replication, updates are propagated asynchronously of the data change. Although in both cases the degree of staleness can be tightly regulated, the allowance for even slightly stale data radically improves the cost overhead involved.
The major constraint in dealing with master/slave databases is that you need to separate read-only from write operations.
Figure 15.9 shows a cluster of MySQL servers set up for master/slave replication.The application can read data from any of the slave servers but must make any updates to replicated tables to the master server.
MySQL does not have a corner on the replication market, of course. Many databases have built-in support for replicating entire databases or individual tables. In Oracle, for example, you can replicate tables individually by using snapshots, or materialized views. Consult your database documentation (or your friendly neighborhood database administrator) for details on how to implement replication in your RDBMS.
Master/slave replication relies on transmitting and applying all write operations across the interested machines. In applications with high-volume read and write concurrency, this can cause slowdowns (due to read consistency issues).Thus, master/slave replication is best applied in situations that have a higher read volume than write volume.

Scaling Databases |
387 |
|
|
|
|
|
|
|
|
|
Figure 15.9 Overview of MySQL master/slave replication.
Writing Applications to Use Master/Slave Setups
In MySQL version 4.1 or later, there are built-in functions to magically handle query distribution over a master/slave setup.This is implemented at the level of the MySQL client libraries, which means that it is extremely efficient.To utilize these functions in PHP, you need to be using the new mysqli extension, which breaks backward compatibility with the standard mysql extension and does not support MySQL prior to version 4.1.
If you’re feeling lucky, you can turn on completely automagical query dispatching, like this:
$dbh = mysqli_init();
mysqli_real_connect($dbh, $host, $user, $password, $dbname); mysqli_rpl_parse_enable($dbh);
// prepare and execute queries as per usual
The mysql_rpl_parse_enable() function instructs the client libraries to attempt to automatically determine whether a query can be dispatched to a slave or must be serviced by the master.
