
Hackers Beware
.pdf•Have a strong password policy
•Implement SYSKEY security enhancement
•Use one-time passwords
•Use Biometric authentication
•Audit access to key files
•Scan for cracking tools
•Keep inventory of active accounts
•Limit who has domain administrator access
The best recommendation for protecting against attacks is to implement as many defenses as possible. Your administrator should not only pick one method, but all that apply. My recommendation is to implement most of these security measures, but only implement SYSKEY if you have extreme circumstances and really know what you are doing. This is explained further in the section, “Implement SYSKEY”. Remember, the more security measures you have in place, the better.
Disable LAN Manager Authentication
Based on how quickly someone can crack a password, most people’s first reaction is to disable LAN Manager authentication and increase the time it takes to brute force a password. As logical as this sounds, there are some down sides. The first is that if you have clients who are running an operating system that uses LAN Manager authentication and you disable it, they will not be able to connect to the system. Some operating systems that use LAN Manager authentication are Windows 95 and 3.1. However, if this is not an issue and all your systems have Windows 98 or NT, then this problem will not impact your system. The key factor to remember is: Think and plan before you act. So many companies, when it comes to security, have knee-jerk reactions that cause a number of unnecessary issues. The old saying “measure twice, cut once” goes a long way, not only for having a secure system, but also for having a robust system.
I had a client call me on a Monday and say that some of his users could not connect to the network. I asked the usual questions: “Did you change anything, and is there a pattern to who can and cannot log on?” What made this hard to diagnosis was that I received the typical response: “No we did not change anything, and there is no logic to who cannot log on to the network.” After going on site and performing some investigation, I noticed that none of the NT users were having problems, but all the Windows 95 users could not connect. It turned out that an administrator read a document stating that turning off LAN Manager authentication would strengthen security, so he reconfigured the registry on all the domain controllers. The administrator was partially correct that it would improve security, but he failed to realize the negative aspect that certain clients would not be able to authenticate to the domain.
“Hackers Beware “ New Riders Publishing |
380 |
My recommendation is to upgrade all your clients to either NT or Windows 98, so you can disable the LAN Manager authentication and increase your security. The main reason to do this is based on the concept of following the path of least resistance. Remember, an attacker is always going to find the easiest way into a network and use that as his attack point. In this case, LAN Manager is the long pole in the tent. As you have seen, in a worst-case scenario, LAN Manager hashes can be cracked in a couple of weeks. On the other hand, according to Microsoft Knowledge Base Articles, because NT authentication or NTLM uses all 14 characters and upper and lowercase characters, it would take, on average, 2,200 years to find the keys, and 5,500 years to find the password, using a 200 Mhz Pentium Pro computer. Even with putting 1,000 computers together, it would take 5.5 years to find the passwords. I don’t know about you, but I like several years or several hundred years over several days or weeks.
For additional details on disabling LAN Manager authentication, see Microsoft Knowledge Base Article Q147706, which can be found at www.microsoft.com by clicking Knowledge Base, which is located under Support. The Microsoft Knowledge Base can also be found by going to http://search.support.microsoft.com/kb/. We cover an overview of the registry keys that need to be modified in Chapter 11, “Fundamentals of Microsoft NT,” but for a detailed description, see the Knowledge Base Article. Microsoft does a great job in its Knowledge Base Articles documenting issues and explaining how to fix problems.
One word of caution: Be extremely careful whenever you modify the registry. If you accidentally modify or delete a key, you could render NT inoperable, and the only way to fix it would be to reload the operating system. My suggestion is if you’ve never modified the registry before, have someone with experience watch you or walk you through the process the first couple of times.
For clarification, the following information is taken from Microsoft Knowledge Base Article Q147706. For disabling LAN Manager authentication and controlling the NTLM security, you would modify the following key:
HKEY_LOCAL_MACHINE\System\Current ControlSet\control\LSA
For maximum control, there are various levels of authentication to choose from. The following is the key information and different levels:
Value: LMCompatibilityLevel
Value Type: REG_DWORD - Number
Valid Range: 0-5
Default: 0
“Hackers Beware “ New Riders Publishing |
381 |
Description: This parameter specifies the type of authentication to be
used.
Level 0 - Send LM response and NTLM response; never use NTLMv2 session
security
Level 1 - Use NTLMv2 session security if negotiated Level 2 - Send NTLM authenication only
Level 3 - Send NTLMv2 authentication only Level 4 - DC refuses LM authentication
Level 5 - DC refuses LM and NTLM authenication (accepts only NTLMv2)
You can also set the minimum security negotiated for applications. That is done through the following registry key:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\control\LSA\MSV1_0 The following are the values for this key:
Value: NtlmMinClientSec
Value Type: REG_DWORD - Number
Valid Range: the logical 'or' of any of the following values:: 0x00000010
0x00000020
0x00080000
0x20000000 Default: 0
Value: NtlmMinServerSec
Value Type: REG_DWORD - Number
Valid Range: same as NtlmMinClientSec Default: 0
Description: This parameter specifies the minimum security to be used.
0x00000010 Message integrity
0x00000020 Message confidentiality
0x00080000 NTLMv2 session security
0x20000000 128 bit encryption
To disable LAN Manager authentication, you need to be running Service Pack 4 (SP4) or higher. If you are not sure about the impact disabling LAN Manager authentication can have on your system, you can start at a lower level and work your way up to Level 4 or Level 5. Also, it is always recommended that before you make any change to a production system, you should implement it first on a test system.
“Hackers Beware “ New Riders Publishing |
382 |
Enforce Strong Passwords
In an ideal world, it would be beneficial if we could tell everyone to obey the law and tell users to have strong passwords. Unfortunately, that is not reality; in most cases, there needs to be some level of enforcement. When it comes to passwords, mechanisms should be put in place to enforce the policy and make sure people follow it. You will never be able to enforce it one hundred percent, but there are some things you can do to make it harder for someone to have a weak password.
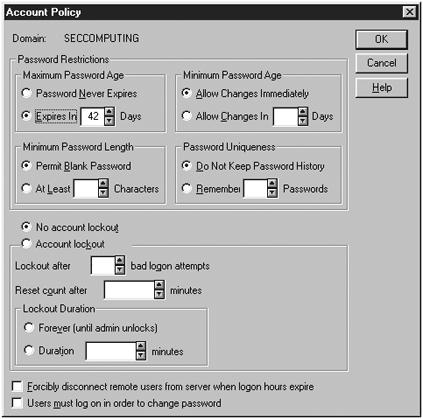
By default, Microsoft NT has some mechanisms in place to enforce strong passwords. The most important mechanism is account policies, which is located under User Manager, as shown in Figure 9.7.
Figure 9.7. Account Policy window used to set password restrictions.
The Account Policies window enables you to determine how often a password expires, the minimum/maximum age of a password, the minimum length of a password, password uniqueness, and account lockout. These are important features and a good starting point, but it is not enough. Even if a password has to be 8 characters long and changed everyday, a user could still have an extremely weak password. In would be nice to have an additional mechanism that forces users to have letters, numbers, and special characters at a minimum.
“Hackers Beware “ New Riders Publishing |
383 |
With Service Pack 2, NT 4.0 introduced a password filter called passfilt.dll, which enforces the following policy:
•Minimum length of password is 6 characters
•Password must contain 3 of the following: uppercase, lowercase, numbers, and special characters.
•Password cannot contain the user ID
One important point is that if the account policy states a required password length of more than 8 characters, and the passfilt states a length of 6 characters, whichever one is longer will be enforced. Using passfilt is better, but it still has some limitations. For example, a password could have uppercase, lowercase, and a number, which would pass passfilt, but would still be weak. The important point is that at least with passfilt the passwords are stronger than they were before. One negative aspect of passfilt is that the settings are hard coded into the dll and can be changed only if you know how to go in and rewrite the dll code. If you want to do that, Microsoft has templates you can follow.
Another way to enforce strong passwords is by using passprop, which comes with NT Server Resource Kit. Passprop enforces the same restrictions as passfilt, but it is easier to setup and more user friendly. To install passprop, run the executable and reboot. The message displayed to the user, if his password does not follow the policy, is more straightforward and easier to understand with passprop than with passfilt. My recommendation is if you are going to use one of these, pick passprop.
If you do want to use passfilt.dll, you have to go in and modify the registry. Remember, whenever you modify the registry, you have to be extremely careful because you can crash NT by one slip of the finger. Before making any changes to the registry, it should be backed up with a tool, such as regback, which is included with the NT Resource Kit.
The following are the changes that have to be made to install passfilt.dll on your NT server:
1.Install the latest Windows NT Server 4.0 Service Pack.
2.Make sure that Passfilt.dll is located in the %SYSTEMROOT%\SYSTEM32 folder.
3.Start regedt32.exe
4.Navigate to the following key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa
5.If it is not already there, add the value Notification Packages of type REG_MULTI_SZ:
1.Select the LSA key.
2.Select the Edit menu, and select Add Value.... (An Add Value dialog box appears.)
“Hackers Beware “ New Riders Publishing |
384 |
3.Type Notification Packages in the Value Name text box, select REG_MULTI_SZ from the Data Type drop-down list box, and click OK. (The Multi-String Editor dialog box appears.)
4.Type PASSFILT in the Data box, and click OK.
6.Exit the registry.
7.Shut down and restart the computer running Windows NT Server.
The passfilt.dll must be loaded on the PDC and all backup domain controllers in the domain.
One mistake that I have seen a lot of people make is that they only install it on the PDC or one of the backup domain controllers. A symptom of this is when only certain users are prompted for strong passwords, while others are not. If this occurs, you know that you missed a domain controller.
Have a Strong Password Policy
This might seem obvious, but this is an area that most companies miss. My recommendation for a password policy is the following:
•A minimum password length of 8, ideally 10 characters long
•Passwords change every 45 days
•Accounts locked after 3 failed logon attempts in 5 hours, and lock it for 3 hours.
•All password must contain at least one alpha, one number, and one special character.
•Cannot reuse previous 5 passwords
•Passwords should not contain birthdays, names, sports team, and so forth.
The following is a tip for picking a good password:
•Use a phrase, and not a word, and then use the first letter of each word in the phrase.
•Example—When I stub my toe, I say !@#$% 5 times.
•Password—WismtIS !@#$%5t
It is important to remember that based on the environment you are working in, a different password policy might be necessary. For example, some companies in highly secure environments might prefer to increase the password length or decrease the password change interval.
Implement SYSKEY
SYSKEY is provided with Service Pack 3, and it allows 128-bit strong encryption of the SAM. SYSKEY should be installed on all domain
“Hackers Beware “ New Riders Publishing |
385 |
controllers. Once again, if you only install it on certain domain controllers, you will experience problems. Microsoft Knowledge Base Article Q143475 contains a thorough discussion of SYSKEY. The following is some of the key information taken from this article.
“The Windows NT Server 4.0 System Key hotfix provides the capability to use strong encryption techniques to increase protection of account password information stored in the registry by the Security Account Manager (SAM). Windows NT Server stores user account information, including a derivative of the user account password, in a secure portion of the Registry protected by access control and encryption. The account information in the Registry is only accessible to members of the Administrators group. Windows NT Server, like other operating systems, allows privileged users who are administrator’s access to all resources in the system. For installations that want enhanced security, strong encryption of account password derivative information provides an additional level of security to prevent Administrators from intentionally or unintentionally accessing password derivatives using registry programming interfaces. If SYSKEY is implemented, L0phtcrack can no longer extract the password hashes.
The strong encryption capability with the Windows NT 4.0 System Key hotfix is an optional feature. Administrators may choose to implement strong encryption by defining a System Key for Windows NT. Strong encryption protects private account information by encrypting the password data using a 128-bit cryptographically random key, known as a password encryption key.
Only the private password information is strongly encrypted in the database, not the entire account database. Every system using the strong encryption option will have a unique password encryption key. The password encryption key is itself encrypted with a System Key. Strong password encryption may be used on both Windows NT Server and Workstation where account information is stored. Using strong encryption of account passwords adds additional protection for the contents of the SAM portion of the registry and subsequent backup copies of the registry information in the %systemroot%\repair directory created using the RDISK command and on system backup tapes.”
The System Key is defined using the command syskey.exe. Only members of the administrators group can run the syskey.exe command. This utility is used to initialize or change the System Key. The System Key is the “master key” used to protect the password encryption key and, therefore, protection of the System Key is a critical system security operation.
“Hackers Beware “ New Riders Publishing |
386 |
The only negative aspect of SYSKEY, and the reason why I would not recommend it, is that there is no uninstall option. After it is installed, the only way to remove it is to reinstall the operating system. For this reason, unless you are 100 percent sure of the consequences of using this program, do not install it. I know so many clients who installed SYSKEY on their domain controllers when it first came out, and then their programs that used third-party authentication stopped working. They realized that it was because the encryption scheme changed, so they figured they would just go in and uninstall SYSKEY. Guess what? They ended up having to reinstall all of their servers. I have done that, and it is not something I would recommend.
Use One-Time Passwords
One-time passwords are very effective against password guessing because the passwords change each time the user logs on. In other words, there are really no passwords to guess. If you want to overcome the passwordguessing problem, then the ideal way is to use one-time passwords. The drawbacks are implementation costs, complexities, and on-going operating costs. The most common form of one-time passwords are smart cards. This is a device that the user must carry around with her whenever she wants to log on to the system. The device is time-triggered, so the password changes every minute. When the user wants to logon, she reads the current password off the display and types it in as the password.
A huge liability with smart cards is replacement of the cards when they are lost or stolen. Think of how often employees loose or forget their badge or the keys to their office. Because smart cards are a lot more expensive, a company could have considerable, increased costs based on the number of cards it has to replace. I know several companies that implemented smart cards and stopped using them because they forgot to account for lost cards, and based on that, they severely ran over their budget.
Many companies implement one-time passwords in addition to regular passwords. For example, while an employee is at a company facility, she would use her regular password to authenticate. Only when she is out of the office and dialing in remotely does she use the one-time password. This helps keep initial costs down and lets you dole out one-time passwords in an incremental manner. Also, using regular passwords in conjunction with one-time passwords helps increase a company’s security, because now authentication is based on something you have and something you know.
Instead of time, some devices use what is known as a challenge response. The user presents his user ID to the system and the system responds with
“Hackers Beware “ New Riders Publishing |
387 |
a challenge. The user then types the challenge into the device, and the device displays a response, which the user then types as his password.
Another form, which is less expensive, is software-based, one-time passwords. A common implementation of this is called SKEY. SKEY uses one-time passwords that are pre-computed when the system is set up. Each user gets a pre-computed list of passwords, and they use a different password each time they logon.
The weakness is that the password list resides on the user’s computer, so it is easier for an attacker to access. Also, if the computer’s hard drive gets damaged, the keys are also lost. On the other hand, because the passwords are on the computer, they are harder for the user to lose than smart cards or other devices the user carries around. The following web site provides additional information on SKEY: http://lheawww.gsfc.nasa.gov/~srr/skey_info.html
Use Biometrics
Passwords are getting easier and easier to crack because machines are getting so fast, which means more companies are turning to biometrics as the solution. Biometrics authenticate a user based on human factors, such as a fingerprint, handprint, retinal scan, or voice scan. These methods are highly reliable and are with a user at all times, so you do not need to worry about someone losing or misplacing a token, which is the case with one-time passwords. Because biometrics are essentially impossible for the user to lose, and there is nothing for an attacker to steal, they are much more reliable. There are several biometric solutions available for computers today. One of the issues is cost because every machine a user could possibly log on to must have an authentication device. Even though biometrics have been proven to be safe, some users are concerned about safety issues, such as having their eyes scanned. Lastly, many people feel uncomfortable having big brother take their personal information and having the ability to track them wherever they go.
The following site is a great reference for additional information on biometrics: http://www.biometricgroup.com/. It contains links to over 100 vendors that provide biometric solutions. It also contains detailed information on the following types of biometrics: finger, facial, iris, retina, hand, voice, and signature.
Audit Access to Key Files
Because password cracking is performed offline in most cases, the only way you can detect whether someone is performing such an attack is to catch them when they are accessing the SAM database. Even if you do not check the audit logs on a regular basis, you must have scripts that scan
“Hackers Beware “ New Riders Publishing |
388 |
the audit log looking for someone accessing key files. If you detect that someone has, you might have to take action, because it probably means that someone compromised, or is in the process of compromising, your passwords. Programs such as tripwire are a good start and should be part of your security plan. The problem with such programs is that they only catch files that have been modified. With password cracking, someone only has to access or read the file, they do not actually have to make any changes.
Scan for Cracking Tools
In some cases, you might get lucky and an attacker might actually run the password-cracking program on your system. This is not nearly as covert as downloading the password file and cracking it offline, however an attacker might do it to use the computing power of the system. In such cases, running a periodic scan for known hacker tools, such as crack, is fairly easy to do, and it can have a huge payoff if an attacker is actually running the password-cracking program on the local system. When I perform security assessments, often I find large numbers of hacker tools on systems that the administrators did not know about because they never looked. To secure your systems, you have to know what is running on them. Do your homework, and check for these tools before they do a lot of damage.
Keep Inventory of Active Accounts
Active accounts that belong to people who are either on leave or no longer work at a company present a huge vulnerability. They are easy for an attacker to compromise because no one is using the account, and there is no one logging in on a regular basis to detect the unauthorized access. In other words, there is no one to verify that the last logon date is incorrect, which would indicate whether someone other than the user has been accessing the account. A company must have a policy for checking active accounts and removing accounts that no longer should be active. If you do not periodically check your accounts, an attacker can create a backdoor account on your system, give it root access, and you would never know about it. Only by checking the system and being able to detect new or suspicious accounts can you prevent this type of behavior.
Limit Who Has Domain Administrator Access
Only a small percentage of users should have domain administrator access. I have found that it tends to be an ego thing in a lot of companies where everyone has to have privileged access. “Well I am certified” or “I am a senior administrator.” Therefore, the individual feels he must have domain administrator access. This type of thinking is a huge security risk and must be changed. If a large number of people have domain
“Hackers Beware “ New Riders Publishing |
389 |
