
Hackers Beware
.pdfBob wants to initiate a connection with the server. During the first leg of the three-way handshake, Bob sends a packet to the server with the synchronization (SYN) bit set saying, “I want to communicate with you.” Having the SYN bit set indicates that the value in the sequence number (SN) field is valid. So, not only does Bob set the SYN bit, but also he sends a value for the initial sequence (ISN) number, which is sequence number for Bob (SN-B). (Sequence numbers will be covered in the section that follows). After the server receives this packet, it sends back a packet with the SYN bit set and an ISN for the server. It also sets the ACK bit acknowledging that it received the first packet and increments Bob’s SN by 1. That completes the second part of the three-way handshake. The last piece occurs when Bob sets the ACK bit saying that the machine acknowledges recipient of the packet and does that by incrementing the SN-S or the sequence number for the server by 1. At this point, the two machines have established a session and can begin communicating.
Sequence Numbers
Sequence numbers are very important to provide reliable communication but they are also crucial to hijacking a session. Sequence numbers are a 32-bit counter, which means the value can be any of over 4 billion possible combinations. In the simplest sense, sequence numbers are used to tell the receiving machine what order the packets should go in when they are received.
Also, the receiving machine uses sequence numbers to tell the sender which packets have been received and which ones have not, so that the sender can resend the lost packets. For example, if the sender sends four packets with sequence numbers 1258, 1256, 1257, and 1255, the recipient uses these numbers to put the packets back into the correct order, which is sequential. Also, the recipient uses the sender’s sequence number to acknowledge the receipt of the packets. In this case, the recipient sends back an acknowledgement of 1259, which says, “1259 is the next packet that I am expecting from the sender.”
Another key point of sequence numbers is that there is one for the sender and one for the receiver. Whenever the sender sends a packet, it uses the sender’s sequence number; and whenever the recipient acknowledges receiving a packet from the sender, it also uses the sender’s sequence number in the acknowledgement. On the other end, the receiver uses its own sequence numbers when sending data back. For example, if Bob and Alice are communicating, there are two different sequence numbers: one for Bob and one for Alice. Bob uses his sequence number for sending packets to Alice, and Alice uses Bob’s sequence numbers for acknowledging which packets she received from Bob. Then, Alice uses her sequence number to send packets to Bob, and Bob uses this sequence number to acknowledge which packets he received from Alice.
“Hackers Beware “ New Riders Publishing |
170 |
Let’s briefly look at how sequence numbers are chosen. This is for an implementation of Linux but can be different, depending on how the operating system vendors implemented the TCP/IP protocol stack. First, when the system boots up, the sequence number is set to 1. The sequence number is then incremented every second, usually by 128,000. Now, if you calculate the math, this means that the sequence number wraps approximately every nine hours, if no connections are made. However, if a connection is made, the sequence number is incremented by 64,000.
One reason sequence numbers are somewhat predictable is to prevent overlapping of sequence numbers. For example, if a packet gets caught up in a routing loop, it could arrive and have the same sequence number as an existing session, which could cause a lot of problems. This presents an interesting dilemma because as you will see, from a security standpoint, you would want the sequence numbers to be as random as possible; but from a functionality standpoint, the less random the better. The following example is sniffer output from an initial connection showing how the sequence numbers work. The computer with the IP address of 10.246.68.46 sends a packet to computer 10.246.68.48 with the SYN bit set and an initial sequence number of 2881395377, as follows:
03:12:26.309374 eth0 P 10.246.68.46.3419 > 10.246.68.48.telnet: S
2881395377:2881395377(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
Next, computer 10.246.68.48 replies to 10.246.68.46 with the SYN bit set and an initial sequence number of 2427498030. Because this is the second leg of the three-way handshake, it also has the ACK bit set and is saying that the next byte it is expecting from machine 10.246.68.46 is 2881395378, which is the initial sequence number plus 1, as follows:
03:12:26.309435 eth0 P 10.246.68.48.telnet > 10.246.68.46.3419: S
2427498030:2427498030(0) ack 2881395378 win 32120 <mss 1460,nop,nop,sackOK> (DF)
Finally, computer 10.146.68.46 completes the last leg of the three-way handshake by sending a packet back to 10.246.68.48 with the ACK bit set, as follows:
03:12:26.309538 eth0 P 10.246.68.46.3419 > 10.246.68.48.telnet: .
1:1(0) ack 1 win 8760 (DF)
“Hackers Beware “ New Riders Publishing |
171 |

The preceding shows a three-way handshake for a telnet session. Here you can see the initial sequence numbers that are sent in the first two packets. After that, you can see the acknowledgement of subsequent sequence numbers and the next packet each side is expecting.
What Is TCPdump?
TCPdump is a sniffer program that is available on most versions of Linux. Depending on which installation options were used to install the software, it might be installed by default. If you type tcpdump and the program does not start, you might have to manually install it off of the distribution CDs.
As you can see from the preceding examples, TCPdump is a good program for pulling off network traffic and seeing what is occurring on your network. It has numerous options that can be used to filter certain fields. For additional information, you can type man tcpdump on your system to get additional information and examples of how it can be used on your network.
There is also a port of TCPdump for the Windows platform called windump. It runs in a DOS window but has similar features and functionality.
At this point, you have enough information to understand the basics of session hijacking and the topics presented in this chapter. Now it is time to look at session hijacking up close. For a more detailed explanation of the TCP/IP protocols, please refer to TCP/IP Illustrated, Volume 1 by Stevens.
Detailed Description of Session Hijacking
Let’s take a closer look at exactly what has to happen to hijack a session. The following are the main steps that must be taken to perform an active session hijack, where the goal is to take over an existing session:
1.Find a target.
2.Perform sequence prediction.
3.Find an active session.
4.Guess the sequence numbers.
5.Take one of the parties offline.
6.Take over the session.
“Hackers Beware “ New Riders Publishing |
172 |
Find a Target
This might seem obvious, but to hijack a session, the attacker must find a suitable target. There are some key points he observes when searching for a suitable target. First, he usually wants the target to be a server that allows session-oriented connections like telnet and FTP. Also, from a firewall standpoint, the attacker probably wants to make sure he can get access to the target beforehand to sample the sequence number. For example, if a firewall only allows a certain address through the firewall to the server, he might be able to hijack that session; but it is difficult to perform because he could not access the server ahead of time and find out some initial information.
Perform Sequence Prediction
Depending on the session he is taking over and whether he can observe the traffic before hijacking the session, the attacker might have to be able to guess the sequence number. This can be easy or difficult depending on which operating system is being used. The following is output from nmap that shows the level of difficulty with guessing sequence numbers on various operating systems (to have nmap perform operating system fingerprinting, you would type the following command nmap –O ip-
address):
Starting nmap V. 2.53 by fyodor@insecure.org ( |
||
www.insecure.org/nmap/ |
) |
|
Interesting ports on (10.246.68.46): |
||
(The 1516 ports scanned but not shown below are in state: |
||
closed) |
State |
Service |
Port |
||
25/tcp |
open |
smtp |
79/tcp |
open |
finger |
106/tcp |
open |
pop3pw |
107/tcp |
open |
rtelnet |
110/tcp |
open |
pop-3 |
139/tcp |
open |
netbios-ssn |
427/tcp |
open |
svrloc |
TCP Sequence Prediction: Class=trivial time dependency Difficulty=1 (Trivial joke)
Remote operating system guess: Windows NT4 / Win95 / Win98 |
|
|
Nmap run completed -- |
1 IP address (1 host up) scanned in 3 |
|
seconds |
|
|
Starting nmap V. 2.53 by fyodor@insecure.org ( |
|
|
www.insecure.org/nmap/ ) |
|
|
Interesting ports on |
(10.246.68.48): |
|
(The 1510 ports scanned but not shown below are in state: |
|
|
closed) |
|
|
“Hackers Beware “ New Riders Publishing |
173 |
|
Port |
State |
Service |
21/tcp |
open |
ftp |
23/tcp |
open |
telnet |
25/tcp |
open |
smtp |
79/tcp |
open |
finger |
98/tcp |
open |
linuxconf |
111/tcp |
open |
sunrpc |
113/tcp |
open |
auth |
513/tcp |
pen |
login |
514/tcp |
open |
shell |
515/tcp |
open |
printer |
948/tcp |
open |
unknown |
1024/tcp |
open |
kdm |
6000/tcp |
open |
X11 |
TCP Sequence Prediction: Class=random positive increments Difficulty=1872725 (Good luck!)
Remote operating system guess: Linux 2.1.122 - 2.2.14
Nmap run completed -- 1 IP address (1 host up) scanned in 0 seconds
One of the things nmap uses to determine the operating system is the predictability of the sequence numbers on the remote operating system. In this case, you can see that Windows operating systems have very predictable sequence numbers, whereas Linux has very hard-to-guess sequence numbers.
Also, to show you how sequence number prediction is done, the attacker connects to a machine several times to see how the numbers change over time. The following are some sample sequence numbers from trying to connect to a Linux system from a Windows system several times. Only the initial sequence numbers are shown for each side. Essentially, the first two legs of the three-way handshake are shown, which means there are two packets for each connection, and I connected five times:
1st connection
04:54:35.209720 eth0 P 10.246.68.46.3428 > 10.246.68.48.telnet: S
2887495515:2887495515(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
04:54:35.209887 eth0 P 10.246.68.48.telnet > 10.246.68.46.3428: S
321765071:321765071(0) ack 2887495516 win 32120 <mss 1460,nop,nop,sackOK> (DF)
2nd connection
“Hackers Beware “ New Riders Publishing |
174 |
04:54:40.195616 eth0 P 10.246.68.46.3429 > 10.246.68.48.telnet: S
2887500502:2887500502(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
04:54:40.195694 eth0 P 10.246.68.48.telnet > 10.246.68.46.3429: S
332010905:332010905(0) ack 2887500503 win 32120 <mss 1460,nop,nop,sackOK> (DF)
3rd connection
04:54:46.799968 eth0 P 10.246.68.46.3430 > 10.246.68.48.telnet: S
2887507109:2887507109(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
04:54:46.800040 eth0 P 10.246.68.48.telnet > 10.246.68.46.3430: S
338617656:338617656(0) ack 2887507110 win 32120 <mss 1460,nop,nop,sackOK> (DF)
4th connection
04:54:52.001391 eth0 P 10.246.68.46.3431 > 10.246.68.48.telnet: S
2887512311:2887512311(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
04:54:52.001473 eth0 P 10.246.68.48.telnet > 10.246.68.46.3431: S
339459049:339459049(0) ack 2887512312 win 32120 <mss 1460,nop,nop,sackOK> (DF)
5th connection
04:54:56.805266 eth0 P 10.246.68.46.3432 > 10.246.68.48.telnet: S
2887517117:2887517117(0) win 8192 <mss 1460,nop,nop,sackOK> (DF)
04:54:56.805348 eth0 P 10.246.68.48.telnet > 10.246.68.46.3432: S
334021331:334021331(0) ack 2887517118 win 32120 <mss 1460,nop,nop,sackOK> (DF)
“Hackers Beware “ New Riders Publishing |
175 |
Table 5.1 is a summary chart showing the ISN (initial sequence numbers) for each side of the connection.
Table 5.1. Comparison of sequence numbers on a Windows and Linux system.
Connection Number |
Windows Client |
Linux Server |
1 |
2887495515 |
321765071 |
2 |
2887500502 |
332010905 |
3 |
2887507109 |
338617656 |
4 |
2887512311 |
339459049 |
5 |
2887517117 |
334021331 |
|
|
|
As you can see, this information confirms what nmap already told us— Windows sequence numbers are much more predictable than Linux sequence numbers.
Find an Active Session
Now let’s look at how an attacker finds an active session. Because he is actively taking over a session, there needs to be a legitimate user’s connection that he can take over. Therefore, contrary to most attacks, which attackers want to perform when no one is around because they are harder to detect, with session hijacking, an attacker wants to perform them when there is a lot of traffic. The logic is twofold. First, he has a lot of sessions to choose from, and second, the more traffic that is occurring, the less chance that someone will notice what is going on. If only one person is connected and he gets knocked off several times, that user might get suspicious, especially if there is not a lot of traffic on the network. On the other hand, if there are many people connected and a lot of traffic, a user will probably overlook getting knocked off, thinking that it is because of the high level of traffic on the network.
Guess the Sequence Numbers
For two parties to communicate, the following are required: the IP addresses, the port numbers, and the sequence number. Finding out the IP address and the port is fairly easy to do; they are listed in the IP packets and do not change throughout the session. After you know that these two addresses are communicating on these two ports, that information stays the same for the remainder of the session. The sequence numbers, however, change. Therefore, an attacker must successfully guess a sequence number. If the server is expecting sequence number 12345 and an attacker sends a packet with 55555, the server will get very confused and will try to re-synch with the original system, which can cause a lot of problems, as you will see. On the other hand, if an attacker sends 12345, the server accepts the packet and processes it, which is the attacker’s goal. If he can get a server to receive
“Hackers Beware “ New Riders Publishing |
176 |
his spoofed packets and execute them, he has successfully hijacked the session.
Take One of the Parties Offline
After the attacker knows the sequence numbers, he has to take one of the parties offline so he can take over the session. The easiest way to take a computer offline is to launch a Denial of Service attack against the system so that it can no longer respond. The server still sends responses back to the system, but because the attacker crashed the system, it cannot respond. (for more information on Denial of Service attacks, see Chapter 6).
The computer that is taken offline is usually the client computer, because ideally an attacker wants to hijack a session with a server. If he is trying to send packets to the server while the other computer is also sending packets, the server can get very confused. This step assumes that the attacker is performing an active hijack of the session. If he only wants to watch the traffic, this step is unnecessary. Because, in most cases, an attacker wants to take over the session, he takes the computer offline.
Take Over the Session
Now that the attacker has all of the information he needs, he can start sending packets to the server and take over the session. He spoofs the source information and the sequence number. If everything was done correctly, the server receives the packets and processes them. Remember, with a session hijacking attack, the attacker is basically flying blind, because he does not receive any of the response packets. Therefore, it is critical for the attacker to predict what the server is going to do, so that his commands can be executed. In the simplest sense, he wants to send packets to a telnet session that creates a new account. This way, he can get back on the machine whenever he wants.
In this example, we are talking about the more complex session hijacking attack where the attacker does not observe all of the traffic. This is similar to the sequence guessing attack that Kevin Mitnick used to break into Tsutomu Shimomura’s system. If an attacker can see all traffic, there is no need to guess the sequence numbers and the attack is much simpler. Therefore, I am covering the more complicated version.
ACK Storms
When an attacker hijacks a session, there can be adverse side effects. One of the side effects is called an ACK storm.
“Hackers Beware “ New Riders Publishing |
177 |
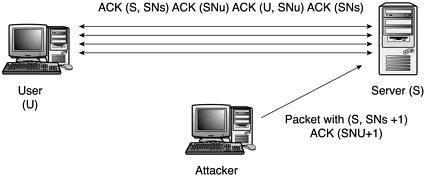
An ACK storm occurs when an attacker first starts to take over a session and sends spoofed packets. Because there is a good chance the attacker does not guess the sequence numbers correctly on first try, this causes some problems. When the server receives the spoofed packets from the attacker, it thinks they came from the legitimate user and notices that the sequence numbers are out of synch. It then tries to re-synch the sequence numbers. The server does this by sending SYN and ACK packets, which the other system replies to with its own SYN and ACK packets. The result is an ACK storm.
ACK storms also occur if the user whose session is being hijacked is not taken offline with a Denial of Service attack. In this case, the server acknowledges the packets that the attacker sent and the user’s machine responds, because it never sent the packets that the server is responding to.
When an ACK storm occurs, performance suffers because a large amount of bandwidth is consumed by the large number of packets that are being sent between the hosts. Figure 5.4 shows what happens when an ACK storm occurs.
Figure 5.4. A graphical depiction of an ACK storm.
Programs That Perform Hijacking
There are several programs available that perform hijacking. We will cover four of them in this section:
•Juggernaut
•Hunt
•TTY Watcher
•IP Watcher
“Hackers Beware “ New Riders Publishing |
178 |
Juggernaut
Juggernaut is a network sniffer that can also be used to hijack TCP sessions. It runs on Linux operating systems in a terminal window. It was one of the first session hijacking tools and is easy to install and run.
Juggernaut can be set to watch for all network traffic or it can be given a keyword or token to look for. For example, a typical token might be the keyword login. Whenever Juggernaut sees this keyword, it captures the session, which means an attacker can capture a user’s password as he is authenticating to a machine. Or from a defensive standpoint, this tool can be set to look for keywords that can indicate a possible attack. By doing this, it becomes easier for an administrator to spot possible breaches of security and take action.
The main function of this program is to maintain information about the various session connections that are occurring on the network. This means that an administrator can use the tool to determine all connections that are occurring on a network. Also, an administrator can take a snapshot of the current connections and look for any unusually activity. On the other hand, an attacker can see all sessions and pick which ones he wants to hijack. As you will see, after Juggernaut detects an active session, there are lots of things that an attacker can do.
Installing Juggernaut
Installing Juggernaut is very straightforward. To install this program, perform the following steps:
1.Download the compressed tar file from packetstorm.securify.com.
2.Uncompress the file by typing gunzip 1.2.tar.gz.
3.Uncompress the tar file by typing tar –xvf 1.2.tar.
2 and 3 can be combined by using the –z option and issuing the following command: tar –zxvf 1.2.tar.gz.
4.Change to the Juggernaut directory by typing cd 1.2.
5.Edit the makefile. The following are some of the key fields you might want to change:
MULTI_P. If this is defined, the program uses the multi-process model of multi-tasking.
IP_HDRINCL. If this is defined, you need to use the IP_HDRINCL socket option to build IP headers.
“Hackers Beware “ New Riders Publishing |
179 |
