
- •Network Intrusion Detection, Third Edition
- •Table of Contents
- •Copyright
- •About the Authors
- •About the Technical Reviewers
- •Acknowledgments
- •Tell Us What You Think
- •Introduction
- •Chapter 1. IP Concepts
- •Layers
- •Data Flow
- •Packaging (Beyond Paper or Plastic)
- •Bits, Bytes, and Packets
- •Encapsulation Revisited
- •Interpretation of the Layers
- •Addresses
- •Physical Addresses, Media Access Controller Addresses
- •Logical Addresses, IP Addresses
- •Subnet Masks
- •Service Ports
- •IP Protocols
- •Domain Name System
- •Routing: How You Get There from Here
- •Summary
- •Chapter 2. Introduction to TCPdump and TCP
- •TCPdump
- •TCPdump Behavior
- •Filters
- •Binary Collection
- •TCPdump Output
- •Absolute and Relative Sequence Numbers
- •Dumping in Hexadecimal
- •Introduction to TCP
- •Establishing a TCP Connection
- •Server and Client Ports
- •Connection Termination
- •The Graceful Method
- •The Abrupt Method
- •Data Transfer
- •What's the Bottom Line?
- •TCP Gone Awry
- •An ACK Scan
- •A Telnet Scan?
- •TCP Session Hijacking
- •Summary
- •Chapter 3. Fragmentation
- •Theory of Fragmentation
- •All Aboard the Fragment Train
- •The Fragment Dining Car
- •The Fragment Caboose
- •Viewing Fragmentation Using TCPdump
- •Fragmentation and Packet-Filtering Devices
- •The Don't Fragment Flag
- •Malicious Fragmentation
- •TCP Header Fragments
- •Teardrop
- •Summary
- •Chapter 4. ICMP
- •ICMP Theory
- •Why Do You Need ICMP?
- •Where Does ICMP Fit In?
- •Understanding ICMP
- •Summary of ICMP Theory
- •Mapping Techniques
- •Tireless Mapper
- •Efficient Mapper
- •Clever Mapper
- •Cerebral Mapper
- •Summary of Mapping
- •Normal ICMP Activity
- •Host Unreachable
- •Port Unreachable
- •Admin Prohibited
- •Need to Frag
- •Time Exceeded In-Transit
- •Embedded Information in ICMP Error Messages
- •Summary of Normal ICMP
- •Malicious ICMP Activity
- •Smurf Attack
- •Tribe Flood Network
- •WinFreeze
- •Loki
- •Unsolicited ICMP Echo Replies
- •Theory 1: Spoofing
- •Theory 2: TFN
- •Theory 3: Loki
- •Summary of Malicious ICMP Traffic
- •To Block or Not to Block
- •Unrequited ICMP Echo Requests
- •Kiss traceroute Goodbye
- •Silence of the LANs
- •Broken Path MTU Discovery
- •Summary
- •Chapter 5. Stimulus and Response
- •The Expected
- •Request for Comments
- •TCP Stimulus-Response
- •Destination Host Listens on Requested Port
- •Destination Host Not Listening on Requested Port
- •Destination Host Doesn't Exist
- •Destination Port Blocked
- •Destination Port Blocked, Router Doesn't Respond
- •UDP Stimulus-Response
- •Destination Host Listening on Requested Port
- •Destination Host Not Listening on Requested Port
- •Windows tracert
- •TCPdump of tracert
- •Protocol Benders
- •Active FTP
- •Passive FTP
- •UNIX Traceroute
- •Summary of Expected Behavior and Protocol Benders
- •Abnormal Stimuli
- •Evasion Stimulus, Lack of Response
- •Evil Stimulus, Fatal Response
- •No Stimulus, All Response
- •Unconventional Stimulus, Operating System Identifying Response
- •Bogus "Reserved" TCP Flags
- •Anomalous TCP Flag Combinations
- •No TCP Flags
- •Summary of Abnormal Stimuli
- •Summary
- •Chapter 6. DNS
- •Back to Basics: DNS Theory
- •The Structure of DNS
- •Steppin' Out on the Internet
- •DNS Resolution Process
- •TCPdump Output of Resolution
- •Strange TCPdump Notation
- •Caching: Been There, Done That
- •Reverse Lookups
- •Master and Slave Name Servers
- •Zone Transfers
- •Summary of DNS Theory
- •Using DNS for Reconnaissance
- •The nslookup Command
- •Name That Name Server
- •HINFO: Snooping for Details
- •List Zone Map Information
- •Tainting DNS Responses
- •A Weak Link
- •Cache Poisoning
- •Summary
- •Part II: Traffic Analysis
- •Chapter 7. Packet Dissection Using TCPdump
- •Why Learn to Do Packet Dissection?
- •Sidestep DNS Queries
- •Normal Query
- •Evasive Query
- •Introduction to Packet Dissection Using TCPdump
- •Where Does the IP Stop and the Embedded Protocol Begin?
- •Other Length Fields
- •The IP Datagram Length
- •Increasing the Snaplen
- •Dissecting the Whole Packet
- •Freeware Tools for Packet Dissection
- •Ethereal
- •tcpshow
- •Summary
- •Chapter 8. Examining IP Header Fields
- •Insertion and Evasion Attacks
- •Insertion Attacks
- •Evasion Attacks
- •IP Header Fields
- •IP Version Number
- •Protocol Number
- •The Don't Fragment (DF) Flag
- •The More Fragments (MF) Flag
- •Mapping Using Incomplete Fragments
- •IP Numbers
- •IP Identification Number
- •Time to Live (TTL)
- •Looking at the IP ID and TTL Values Together to Discover Spoofing
- •IP Checksums
- •Summary
- •Chapter 9. Examining Embedded Protocol Header Fields
- •Ports
- •TCP Checksums
- •TCP Sequence Numbers
- •Acknowledgement Numbers
- •TCP Flags
- •TCP Corruption
- •ECN Flag Bits
- •Operating System Fingerprinting
- •Retransmissions
- •Using Retransmissions Against a Hostile Host—LaBrea Tarpit Version 1
- •TCP Window Size
- •LaBrea Version 2
- •Ports
- •UDP Port Scanning
- •UDP Length Field
- •ICMP
- •Type and Code
- •Identification and Sequence Numbers
- •Misuse of ICMP Identification and Sequence Numbers
- •Summary
- •Chapter 10. Real-World Analysis
- •You've Been Hacked!
- •Netbus Scan
- •How Slow Can you Go?
- •RingZero Worm
- •Summary
- •Chapter 11. Mystery Traffic
- •The Event in a Nutshell
- •The Traffic
- •DDoS or Scan
- •Source Hosts
- •Destination Hosts
- •Scanning Rates
- •Fingerprinting Participant Hosts
- •Arriving TTL Values
- •TCP Window Size
- •TCP Options
- •TCP Retries
- •Summary
- •Part III: Filters/Rules for Network Monitoring
- •Chapter 12. Writing TCPdump Filters
- •The Mechanics of Writing TCPdump Filters
- •Bit Masking
- •Preserving and Discarding Individual Bits
- •Creating the Mask
- •Putting It All Together
- •TCPdump IP Filters
- •Detecting Traffic to the Broadcast Addresses
- •Detecting Fragmentation
- •TCPdump UDP Filters
- •TCPdump TCP Filters
- •Filters for Examining TCP Flags
- •Detecting Data on SYN Connections
- •Summary
- •Chapter 13. Introduction to Snort and Snort Rules
- •An Overview of Running Snort
- •Snort Rules
- •Snort Rule Anatomy
- •Rule Header Fields
- •The Action Field
- •The Protocol Field
- •The Source and Destination IP Address Fields
- •The Source and Destination Port Field
- •Direction Indicator
- •Summary
- •Chapter 14. Snort Rules - Part II
- •Format of Snort Options
- •Rule Options
- •Msg Option
- •Logto Option
- •Ttl Option
- •Id Option
- •Dsize Option
- •Sequence Option
- •Acknowledgement Option
- •Itype and Icode Options
- •Flags Option
- •Content Option
- •Offset Option
- •Depth Option
- •Nocase Option
- •Regex Option
- •Session Option
- •Resp Option
- •Tag Option
- •Putting It All Together
- •Summary
- •Part IV: Intrusion Infrastructure
- •Chapter 15. Mitnick Attack
- •Exploiting TCP
- •IP Weaknesses
- •SYN Flooding
- •Covering His Tracks
- •Identifying Trust Relationships
- •Examining Network Traces
- •Setting Up the System Compromise?
- •Detecting the Mitnick Attack
- •Trust Relationship
- •Port Scan
- •Host Scan
- •Connections to Dangerous Ports
- •TCP Wrappers
- •Tripwire
- •Preventing the Mitnick Attack
- •Summary
- •Chapter 16. Architectural Issues
- •Events of Interest
- •Limits to Observation
- •Human Factors Limit Detects
- •Limitations Caused by the Analyst
- •Limitations Caused by the CIRTs
- •Severity
- •Criticality
- •Lethality
- •Countermeasures
- •Calculating Severity
- •Scanning for Trojans
- •Analysis
- •Severity
- •Host Scan Against FTP
- •Analysis
- •Severity
- •Sensor Placement
- •Outside Firewall
- •Sensors Inside Firewall
- •Both Inside and Outside Firewall
- •Analyst Console
- •Faster Console
- •False Positive Management
- •Display Filters
- •Mark as Analyzed
- •Drill Down
- •Correlation
- •Better Reporting
- •Event-Detection Reports
- •Weekly/Monthly Summary Reports
- •Summary
- •Chapter 17. Organizational Issues
- •Organizational Security Model
- •Security Policy
- •Industry Practice for Due Care
- •Security Infrastructure
- •Implementing Priority Countermeasures
- •Periodic Reviews
- •Implementing Incident Handling
- •Defining Risk
- •Risk
- •Accepting the Risk
- •Trojan Version
- •Malicious Connections
- •Mitigating or Reducing the Risk
- •Network Attack
- •Snatch and Run
- •Transferring the Risk
- •Defining the Threat
- •Recognition of Uncertainty
- •Risk Management Is Dollar Driven
- •How Risky Is a Risk?
- •Quantitative Risk Assessment
- •Qualitative Risk Assessments
- •Why They Don't Work
- •Summary
- •Chapter 18. Automated and Manual Response
- •Automated Response
- •Architectural Issues
- •Response at the Internet Connection
- •Internal Firewalls
- •Host-Based Defenses
- •Throttling
- •Drop Connection
- •Shun
- •Proactive Shunning
- •Islanding
- •Reset
- •Honeypot
- •Proxy System
- •Empty System
- •Honeypot Summary
- •Manual Response
- •Containment
- •Freeze the Scene
- •Sample Fax Form
- •On-Site Containment
- •Site Survey
- •System Containment
- •Hot Search
- •Eradication
- •Recovery
- •Lessons Learned
- •Summary
- •Chapter 19. Business Case for Intrusion Detection
- •Part One: Management Issues
- •Bang for the Buck
- •The Expenditure Is Finite
- •Technology Used to Destabilize
- •Network Impacts
- •IDS Behavioral Modification
- •The Policy
- •Part of a Larger Strategy
- •Part Two: Threats and Vulnerabilities
- •Threat Assessment and Analysis
- •Threat Vectors
- •Threat Determination
- •Asset Identification
- •Valuation
- •Vulnerability Analysis
- •Risk Evaluation
- •Part Three: Tradeoffs and Recommended Solution
- •Identify What Is in Place
- •Identify Your Recommendations
- •Identify Options for Countermeasures
- •Cost-Benefit Analysis
- •Follow-On Steps
- •Repeat the Executive Summary
- •Summary
- •Chapter 20. Future Directions
- •Increasing Threat
- •Improved Targeting
- •How the Threat Will Be Manifested
- •Defending Against the Threat
- •Skills Versus Tools
- •Analysts Skill Set
- •Improved Tools
- •Defense in Depth
- •Emerging Techniques
- •Virus Industry Revisited
- •Smart Auditors
- •Summary
- •Part V: Appendixes
- •Appendix A. Exploits and Scans to Apply Exploits
- •False Positives
- •All Response, No Stimulus
- •Scan or Response?
- •SYN Floods
- •Valid SYN Flood
- •False Positive SYN Flood
- •Back Orifice?
- •IMAP Exploits
- •10143 Signature Source Port IMAP
- •111 Signature IMAP
- •Source Port 0, SYN and FIN Set
- •Source Port 65535 and SYN FIN Set
- •DNS Zone Followed by 0, SYN FIN Targeting NFS
- •Scans to Apply Exploits
- •mscan
- •Son of mscan
- •Access Builder?
- •Single Exploit, Portmap
- •rexec
- •Targeting SGI Systems?
- •Discard
- •Weird Web Scans
- •IP-Proto-191
- •Summary
- •Appendix B. Denial of Service
- •Brute-Force Denial-of-Service Traces
- •Smurf
- •Directed Broadcast
- •Echo-Chargen
- •Elegant Kills
- •Teardrop
- •Land Attack
- •We're Doomed
- •nmap
- •Distributed Denial-of-Service Attacks
- •Intro to DDoS
- •DDoS Software
- •Trinoo
- •Stacheldraht
- •Summary
- •Appendix C. Detection of Intelligence Gathering
- •Network and Host Mapping
- •Host Scan Using UDP Echo Requests
- •Netmask-Based Broadcasts
- •Port Scan
- •Scanning for a Particular Port
- •Complex Script, Possible Compromise
- •"Random" Port Scan
- •Database Correlation Report
- •SNMP/ICMP
- •FTP Bounce
- •NetBIOS-Specific Traces
- •A Visit from a Web Server
- •Null Session
- •Stealth Attacks
- •Explicit Stealth Mapping Techniques
- •FIN Scan
- •Inverse Mapping
- •Answers to Domain Queries
- •Answers to Domain Queries, Part 2
- •Fragments, Just Fragments
- •Measuring Response Time
- •Echo Requests
- •Actual DNS Queries
- •Probe on UDP Port 33434
- •3DNS to TCP Port 53
- •Worms as Information Gatherers
- •Pretty Park Worm
- •RingZero
- •Summary

and the web browser host strips the received message to pass to the application layer supporting the web browser.
Packaging (Beyond Paper or Plastic)
At a very granular level, data exchanged between hosts must be bundled in some kind of standard format. A host is a generic term that can reference a workstation on your desk, a router, or a web server to name just a few examples. The important distinction is that these computers are connected to a network capable of transporting data to and from the computer. In the generic sense, the packaging of associated data is called a packet. The problem in terminology arises because this data package is labeled differently at various layers of communication between the source application and the destination application located on different hosts. This section discusses some of the key concepts related to data packaging,
including bits, bytes, packets, data encapsulation, and interpretation of the layers.
Bits, Bytes, and Packets
The atom of computing is a bit, a single storage location that has a value of either 0 or 1 (also known as binary). Although succinct and compact, you cannot actually store or convey a lot of information with a single bit, so bits are grouped into clumps of eight. A unit of eight bits is a byte (or octet, if you prefer). Eight times a very small amount of information is still pretty small, but an octet can contain an American Standard Code for Information Interchange (ASCII) character, such as the letter a or a comma (,). It can also hold a large integer
number, as high as 255 (28-1).
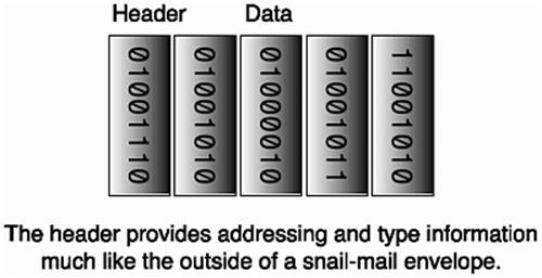
Bits, Bytes, and Binary
Figure 1.2 shows a byte. Because this discussion is focusing on bits, binary is the language used— the language of 0s and 1s. Each bit is represented as a power of 2, the base of binary. Notice that a byte spans powers of 2 from 20 through 27. If all bits have a value of 0, the byte is obviously 0. Now, imagine that all bits are 1s. Add up all the individual bit values, starting with the smallest value (20 = 1, any base with an exponent of 0 is 1); you will have 1 + 2 + 4 + 8 + 16 + 32 + 64 + 128. The total value is 255, and that is the maximum value that a given byte can have. This value is examined later when the discussion turns to IP addresses.
Figure 1.2.
You just saw an example of how binary-to-decimal conversion is done. If you are given a byte of data, just re-create this byte with the appropriate powers of 2 and their associated decimal values. Any bit that is set is assigned the accompanying decimal value of that bit. Then, just total up all the decimal values; voila, the conversion is done. This is not really rocket science after all.
Multiple bytes, or octets, are grouped together for shipping across a network by packaging
them into packets. Figure 1.3 shows one of the great truths of networking: An overhead cost accrues when slinging packets around the network.You have to go through a lot of trouble to package your content for shipping across a network and then to unwrap it when it gets to the other side (and even more trouble, of course, to finish the job with a tamper-proof seal). A field known as the cyclical redundancy check (CRC), or checksum, is used to validate that the frame (the name given to the packet on the wire) has not been damaged or corrupted in transit.
Figure 1.3. Portrait of a packet.
Like an envelope addressed for mailing, IP packets need to include the addresses of both the sending and receiving hosts (see Figure 1.3). If you live in a house with a street address, you can think of that as your hardware address, the address assigned to your house. In networking, at least with Ethernet networks, this is analogous to a network interface card's (NIC) Media Access Controller (MAC) address. This hardware address is assigned to the NIC when the card is constructed. The MAC address is 48 bits long, which means it can hold a very large number (248-1). The "Addresses" section later in this chapter discusses the differences between MAC addresses and IP addresses.
To create a frame, which is the name the packet acquires when transmitted on physical media, you construct the packet using various protocol layers and then include the physical information. Finally, the frame is placed on the networking medium by the NIC. The frame has a frame header of 14 bytes, with fields such as the source and destination MAC addresses,
frame data that can vary in length, and a trailer of 4 bytes that represents the CRC.
Encapsulation Revisited
Figure 1.4 represents the concept of the layered packaging configuration. Different layers of protocols theoretically "talk" to like layers of protocols on the source and destination hosts. The layers are stacked atop one another— hence, the origin of the term "TCP/IP stack." At each layer of the stack, the packet consists of a header of its own and data, sometimes known as the payload. All the encapsulation is done for the purpose of sending some kind of content, but the encapsulation requires different header information at different levels in its journey from source to destination.
Figure 1.4. One layer's header is another layer's data.
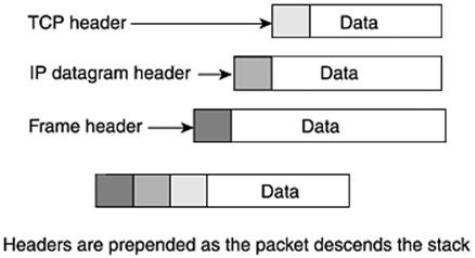
Suppose that you have a message or other content to send. It is first collected by the application, which could be a program such as telnet or electronic mail; these TCP applications are discussed in more detail in the section "IP Protocols." The TCP packet is known as a TCP segment and includes the TCP header and TCP data. If this were UDP, the packet would be known as a datagram, which is confusing because it is redundant with the name at the IP layer.
At this point, the TCP segment is handed down from the TCP layer of the TCP/IP stack to the IP layer. The IP layer prepends (that means appends at the front) header information to the TCP segment and becomes known as an IP datagram. Really, the TCP header and data become invisibly enmeshed as data for the IP datagram, which has its own header. The IP datagram is delivered to the link layer of the TCP/IP stack, and it is known as a frame. The link layer prepends the frame header to the IP datagram to carry it across the physical medium, such as Ethernet.
The process is repeated in reverse when the frame arrives at the destination host and all headers are stripped away and passed to the proper upper-layer protocols. Each layer of the TCP/IP stack with its embedded message converses with the similar layer of the receiving
host.
Interpretation of the Layers
With all the layering going on, the bottom line is that you have a bunch of adjacent 0s and 1s. How do you know how to interpret them? Suppose that you are looking at the IP header; how do you know what kind of embedded protocol you will find following it? Surely that must be known to properly interpret the protocol. The term protocol is meant to denote a set of agreed upon rules or formats. Each protocol (such as IP, TCP, UDP, and ICMP) has its own layouts and formats.
Figure 1.5 shows an example of the organization of the IP header. You can see that a certain number of bits are allocated for each field in the header. A Protocol field identifies the embedded protocol. Each row that you see in the IP header is 32 bits (0 through 31, inclusive), which means four (8-bit) bytes. To complicate matters a little, counting starts with 0 when talking about bit and byte locations. The first row represents bytes 0 through 3; the second row represents bytes 4 through 7; and the third row represents bytes 8 through 11. Notice that the circled Protocol field is in the third row. The preceding time-to-live (TTL) field is 1 byte long, which makes it the 8th byte; and the Protocol field, which is also 1 byte long, represents the 9th byte. This means that the 9th byte (actually, it's the 10th byte, but remember counting starts at 0) is examined to find the embedded protocol. The point is that most packets at their respective levels are positional; fields can be discovered by going to known displacements in the packet.
Figure 1.5. Positional layouts.
