
CISSP - Certified Information Systems Security Professional Study Guide, 2nd Edition (2004)
.pdf
Answers to Review Questions |
561 |
Answers to Review Questions
1.C. A crime is any violation of a law or regulation. The violation stipulation defines the action as a crime. It is a computer crime if the violation involves a computer either as the target or a tool.
2.B. A military and intelligence attack is targeted at the classified data that resides on the system. To the attacker, the value of the information justifies the risk associated with such an attack. The information extracted from this type of attack is often used to plan subsequent attacks.
3.A. Confidential information that is not related to the military or intelligence agencies is the target of business attacks. The ultimate goal could be destruction, alteration, or disclosure of confidential information.
4.B. A financial attack focuses primarily on obtaining services and funds illegally.
5.B. A terrorist attack is launched to interfere with a way of life by creating an atmosphere of fear. A computer terrorist attack can reach this goal by reducing the ability to respond to a simultaneous physical attack.
6.D. Any action that can harm a person or organization, either directly or through embarrassment, would be a valid goal of a grudge attack. The purpose of such an attack is to “get back” at someone.
7.A, C. Fun attacks have no reward other than providing a boost to pride and ego. The thrill of launching a fun attack comes from the act of participating in the attack (and not getting caught).
8.C. Although the other options have some merit in individual cases, the most important rule is to never modify, or taint, evidence. If you modify evidence, it becomes inadmissible in court.
9.D. The most compelling reason for not removing power from a machine is that you will lose the contents of memory. Carefully consider the pros and cons of removing power. After all is considered, it may be the best choice.
10.C. Although an organization would not want to report a large number of incidents (unless reporting them is mandatory), the reality is that many incidents are never discovered. The lack of well-trained users results in many incidents that are never recognized.
11.D. An incident is defined by your security policy. Actions that you define as an incident may not be considered an incident in another organization. For example, your organization may prohibit Internet access while another organization encourages it. Accessing the Internet would be an incident in your organization.
12.B. Some port scans are normal. An unusually high volume of port scan activity can be a reconnaissance activity preceding a more dangerous attack. When you see unusual port scanning, you should always investigate.
13.A. Anytime an attacker exceeds their authority, the incident is classified as a system compromise. This includes valid users who exceed their authority as well as invalid users who gain access through the use of a valid user ID.

562 Chapter 18 Incidents and Ethics
14.C. Although options A, B, and D are actions that can make you aware of what attacks look like and how to detect them, you will never successfully detect most attacks until you know your system. When you know what the activity on your system looks like on a normal day, you can immediately detect any abnormal activity.
15.B. In this case, you need a search warrant to confiscate equipment without giving the suspect time to destroy evidence. If the suspect worked for your organization and you had all employees sign consent agreements, you could simply confiscate the equipment.
16.A. Log files contain a large volume of generally useless information. However, when you are trying to track down a problem or an incident, they can be invaluable. Even if an incident is discovered as it is happening, it may have been preceded by other incidents. Log files provide valuable clues and should be protected and archived.
17.A, D. You must report an incident when the incident resulted in the violation of a law or regulation. This includes any damage (or potential damage) to or disclosure of protected information.
18.D. Ethics are simply rules of personal behavior. Many professional organizations establish formal codes of ethics to govern their members, but ethics are personal rules individuals use to guide their lives.
19.B. The second canon of the (ISC)2 Code of Ethics states how a CISSP should act, which is honorably, honestly, justly, responsibly, and legally.
20.B. RFC 1087 does not specifically address the statements in A, C, or D. Although each type of activity listed is unacceptable, only the activity identified in option B is identified in RFC 1087.
Chapter Physical Security
19 Requirements
THE CISSP EXAM TOPICS COVERED IN THIS
CHAPTER INCLUDE:
Physical Security Threats
Facility Requirements
Forms of Physical Access Controls
Technical Controls
Environment and Life Safety



566 Chapter 19 Physical Security Requirements
Where are the closest emergency services located (fire, medical, police)? What unique hazards are found in the area (chemical plants, homeless shelter, university, construction, etc.)?
Accessibility
The accessibility to the area is also important. Single entrances are great for providing security, but multiple entrances are better for evacuation during emergencies. What types of roads are nearby? What means of transportation are easily accessible (trains, highway, airport, shipping)? What is the level of traffic throughout the day?
Natural Disasters
Another concern is the effect of natural disasters in the area. Is the area prone to earthquakes, mud slides, sink holes, fires, floods, hurricanes, tornadoes, falling rocks, snow, rainfall, ice, humidity, heat, extreme cold, and so on? You must prepare for natural disasters and equip your IT environment to either survive an event or be easily replaceable.
Facility Design
When designing a facility for construction, you need to understand the level of security needed by your organization. The proper level of security must be planned and designed before construction begins. Some important issues to consider include the combustibility, fire rating, construction materials, load rating, placement, and control of items such as walls, doors, ceilings, flooring, HVAC, power, water, sewage, gas, and so on. Forced intrusion, emergency access, resistance to entry, direction of entries and exits, use of alarms, and conductivity are other important aspects to evaluate. Every element within a facility should be evaluated in terms of how it could be used for and against the protection of the IT infrastructure and personnel (for example, positive flows for both air and water from inside the facility to the outside of the facility).
Work Areas
The design and configuration of work areas and visitor areas should be carefully considered. There should not be equal access to all locations within a facility. Areas that contain assets of higher value or importance should have restricted access. For example, anyone who enters the facility should be able to access the restrooms and the public telephone, but only the network administrators and security staff should have access to the server room. Valuable and confidential assets should be located in the heart or center of protection provided by a facility. In effect, you should focus on deploying concentric circles of protection. This type of configuration requires increased levels of authorization to gain access into the more sensitive areas of the organization. Walls or partitions can be used to separate similar but distinct work areas. Such divisions deter casual shoulder surfing or eavesdropping. Shoulder surfing is the act of gathering information from a system by observing the monitor or the use of the keyboard by the operator. Floor-to-ceiling walls should be used to separate areas with differing levels of sensitivity and
confidentiality.
Facility Requirements |
567 |
Each work area should be evaluated and assigned a type of classification just as IT assets are classified. Only people with clearance or classifications corresponding to the classification of the work area should be allowed access. Areas with different purposes or uses should be assigned different levels of access or restrictions. The more access to assets the equipment within an area offers, the greater the restrictions to control who enters those areas and what activities they perform should be.
Server Rooms
Centralized server or computer rooms need not be human compatible. In fact, the more human incompatible a server room is, the more protection against both casual and determined attacks it will offer. Human incompatibility can be accomplished by including Halon or other oxygendisplacement fire detection and extinguishing systems, low temperatures, little or no lighting, and equipment stacked so there is little room for walking or moving. Server rooms should be designed to best support the operation of the IT infrastructure and to prevent unauthorized human access and intervention.
Visitors
If a facility employs restricted areas to control physical security, then a mechanism to handle visitors is required. Often an escort is assigned to visitors and their access and activities are monitored closely. Failing to track the actions of outsiders when they are granted access into a protected area can result in malicious activity against the most protected assets.
Deploying Physical Access Controls
In the real world, you will deploy multiple layers of physical access controls to manage the traffic of authorized and unauthorized individuals within your facility. The outermost layer will be lighting. The entire outer perimeter of your site should be clearly lit. This will provide for easy identification of personnel and make it easier to notice intrusions. Just inside of the lighted area should be a fence or wall designed to prevent intrusion. Specific controlled points along that fence or wall should be entrance points. There should be gates, turnstiles, or mantraps all monitored by closed-circuit television (CCTV) and security guards. Identification and authentication should be required at these entrance points before entrance is granted.
Within the facility, areas of different sensitivity or confidentiality levels should be distinctly separated and compartmentalized. This is especially true of public areas and areas accessible to visitors. An additional identification/authentication process to validate a need to enter should be required when anyone is moving from one area to another. The most sensitive resources and systems should be isolated from all but the most privileged personnel and located at the center or core of the facility.

568 Chapter 19 Physical Security Requirements
Forms of Physical Access Controls
There are many types of physical access control mechanisms that can be deployed in an environment to control, monitor, and manage access to a facility. These range from deterrents to detection mechanisms.
The various sections, divisions, or areas of a site or facility should be clearly designated as public, private, or restricted. Each of these areas requires unique and focused physical access controls, monitoring, and prevention mechanisms. The following sections discuss many of the mechanisms that can be used to separate, isolate, and control access to the various types of areas on a site.
Fences, Gates, Turnstiles, and Mantraps
A fence is a perimeter-defining device. Fences are used to clearly differentiate between areas that are under a specific level of security protection and those that aren’t. Fencing can include a wide range of components, materials, and construction methods. It can consist of stripes painted on the ground, chain link fences, barbed wire, concrete walls, and even invisible perimeters using laser, motion, or heat detectors. Various types of fences are effective against different types of intruders:
Fences that are 3 to 4 feet high deter casual trespassers.
Fences that are 6 to 7 feet high are too hard to climb easily.
Fences that are 8 feet high with three strands of barbed wire deter determined intruders.
A gate is a controlled exit and entry point in a fence. The deterrent level of a gate must be equivalent to the deterrent level of the fence to sustain the effectiveness of the fence as a whole. Hinges and locking/closing mechanisms should be hardened against tampering, destruction, or removal. When a gate is closed, it should not offer any additional access vulnerabilities. Gates should be kept to a minimum. They may be manned by guards or not. When they’re not protected by guards, deployment of dogs or CCTV is recommended.
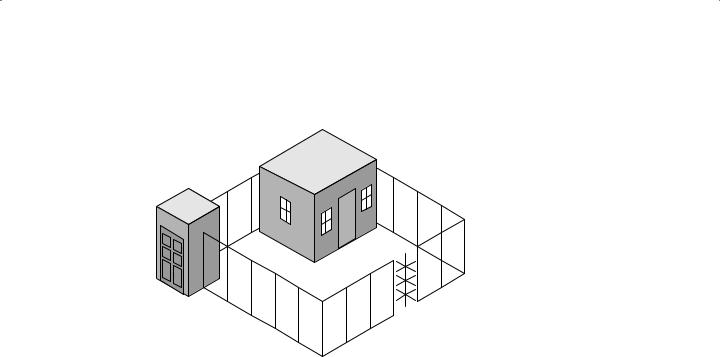
A turnstile (see Figure 19.1) is a form of gate that prevents more than one person from gaining entry at a time and often restricts movement in one direction. It is used to gain entry but not exit or vice versa. A turnstile is basically a fencing equivalent of a secured revolving door.
A mantrap is a double set of doors that is often protected by a guard (see Figure 19.1). The purpose of a mantrap is to contain a subject until their identity and authentication is verified. If they are proven to be authorized for entry, the inner door opens, allowing them to enter the facility or premises. If they are not authorized, both doors remain closed and locked until an escort (typically a guard or a police officer) arrives to escort them off the property or arrest them for trespassing.
Lighting
Lighting is one of the most commonly used forms of perimeter security control. The primary purpose of lighting is to discourage casual intruders, trespassers, prowlers, and would-be thieves who would rather perform their maliciousness in the dark. However, lighting is not a strong deterrent. It should not be used as the primary or sole protection mechanism except in areas with a low threat level.
Forms of Physical Access Controls |
569 |
F I G U R E 1 9 . 1 A secure physical boundary with a mantrap and a turnstile
Secured area
Mantrap
Turnstile
Lighting should not illuminate the positions of guards, dogs, patrol posts, or other similar security elements. It should be combined with guards, dogs, CCTV, or some form of intrusion detection or surveillance mechanism. Lighting must not cause a nuisance or problem for nearby residents, roads, railways, airports, and so on.
The National Institute of Standards and Technology (NIST) standard for perimeter protection using lighting is that critical areas should be illuminated with 2 candle feet of power at a height of 8 feet.
Security Guards and Dogs
All physical security controls, whether static deterrents or active detection and surveillance mechanisms, ultimately rely upon personnel to intervene and stop actual intrusions and attacks. Security guards exist to fulfill this need. Guards may be posted around a perimeter or inside to monitor access points or watch detection and surveillance monitors. The real benefit of guards is that they are able to adapt and react to any condition or situation. Guards are able to learn and recognize attack and intrusion activities and patterns, can adjust to a changing environment, and are able to make decisions and judgment calls. Security guards are often an appropriate security control when immediate, onsite, situation handling and decision making is necessary.
Unfortunately, using security guards is not a perfect solution. There are numerous disadvantages to deploying, maintaining, and relying upon security guards. Not all environments and facilities support security guards. This may be due to actual human incompatibility or to the layout, design, location, and construction of the facility. Not all security guards are themselves reliable. Prescreening, bonding, and training do not guarantee that you won’t end up with an ineffective and unreliable security guard. Likewise, even if a guard is initially reliable, they are subject to physical injury and illness, take vacations, can become distracted, are vulnerable to social engineering, and can become unemployable due to substance abuse. In addition, they are

570 Chapter 19 Physical Security Requirements
sometimes focused on self-preservation instead of the preservation of the security of the guarded facility. This may mean that security guards can offer protection only up to the point at which their life is endangered. Additionally, security guards are usually unaware of the scope of the operations within a facility and are therefore not thoroughly equipped to know how to respond to every situation. Finally, security guards are expensive.
Guard dogs can be an alternative to security guards. They can often be deployed as a perimeter security control. As a detection and deterrent, dogs are extremely effective. However, dogs are costly, require a high level of maintenance, and impose serious insurance and liability requirements.
Keys and Combination Locks
Locks are used to keep closed doors closed. They are designed and deployed to prevent access to everyone without proper authorization. A lock is a crude form of an identification and authorization mechanism. If you posses the correct key or combination, you are considered authorized and permitted entry. Key-based locks are the most common and inexpensive forms of physical access control devices. These are often known as preset locks. Programmable or combination locks offer a broader range of control than preset locks. Some programmable locks can be configured with multiple valid access combinations or may include digital or electronic controls employing keypads, smart cards, or cipher devices.
Locks serve as an alternative to security guards as a perimeter entrance access control device. A gate or door can be opened and closed to allow access by a security guard who verifies your identity before granting access, or the lock itself can serve as the verification device that also grants or restricts entry.
Badges
Badges, identification cards, and security IDs are forms of physical identification and/or of electronic access control devices. A badge can be as simple as a name tag indicating whether you are a valid employee or a visitor. Or it can be as complex as a smart card or token device that employs multifactor authentication to verify and prove your identity and provide authentication and authorization to access a facility, specific rooms, or secured workstations. Badges often include pictures, magnetic strips with encoded data, and personal details to help a security guard verify identity.
Badges may be used in environments in which physical access is primarily controlled by security guards. In such conditions, the badge serves as a visual identification tool for the guards. They can verify your identity by comparing your picture to your person and consult a printed or electronic roster of authorized personnel to determine whether you have valid access.
Badges can also serve in environments guarded by scanning devices rather than security guards. In such conditions, the badge can be used either for identification or for authentication. When the badge is used for identification, it is swiped in a device and then the badge owner must provide one or more authentication factors, such as a password, pass phrase, or biological trait (if a biometric device is used). When the badge is used for authentication, the badge owner provides their ID, username, and so on and then swipes the badge to authenticate.
