
- •About the Authors
- •Dedication
- •Authors’ Acknowledgments
- •Contents at a Glance
- •Table of Contents
- •Introduction
- •About This Book
- •Foolish Assumptions
- •How This Book Is Organized
- •Part I: Introducing Service Management
- •Part II: Getting the Foundation in Place
- •Part VI: The Part of Tens
- •Icons Used in This Book
- •Where to Go from Here
- •Knowing That Everything Is a Service
- •Looking at How the Digital World Has Turned Everything Upside Down
- •Implementing Service Management
- •Managing Services Effectively
- •Seeing the Importance of Oversight
- •Understanding Customers’ Expectations
- •Looking at a Service from the Outside
- •Understanding Service Management
- •Dealing with the Commercial Reality
- •Understanding What Best Practices and Standards Can Do for You
- •Using Standards and Best Practices to Improve Quality
- •Finding Standards
- •Getting Certified
- •ITIL V3: A Useful Blueprint for Enterprise Service Management
- •Seeing What Service Management Can Do for Your Organization
- •Starting with the Service Strategy
- •Creating a Service Management Plan
- •Defining a Service Management Plan
- •Automating Service
- •Getting to the Desired End State
- •Four Key Elements to Consider
- •Federating the CMDB
- •Balancing IT and Business Requirements
- •Measuring and Monitoring Performance
- •Making Governance Work
- •Developing Best Practices
- •Seeing the Data Center As a Factory
- •Optimizing the Data Center
- •Managing the Data Center
- •Managing the Facility
- •Managing Workloads
- •Managing Hardware
- •Managing Data Resources
- •Managing the Software Environment
- •Understanding Strategy and Maturity
- •Seeing How a Service Desk Works
- •Managing Events
- •Dividing Client Management into Five Process Areas
- •Moving the Desktop into the Data Center
- •Creating a Data Management Strategy
- •Understanding Virtualization
- •Managing Virtualization
- •Taking Virtualization into the Cloud
- •Taking a Structured Approach to IT Security
- •Implementing Identity Management
- •Employing Detection and Forensics
- •Encrypting Data
- •Creating an IT Security Strategy
- •Defining Business Service Management
- •Putting Service Levels in Context
- •Elbit Systems of America
- •Varian Medical Systems
- •The Medical Center of Central Georgia
- •Independence Blue Cross
- •Sisters of Mercy Health System
- •Partners HealthCare
- •Virgin Entertainment Group
- •InterContinental Hotels Group
- •Commission scolaire de la Région-de-Sherbrooke
- •CIBER
- •Do Remember Business Objectives
- •Don’t Stop Optimizing after a Single Process
- •Do Remember Business Processes
- •Do Plan for Cultural Change
- •Don’t Neglect Governance
- •Do Keep Security in Mind
- •Don’t Try to Manage Services without Standardization and Automation
- •Do Start with a Visible Project
- •Don’t Postpone Service Management
- •Hurwitz & Associates
- •ITIL
- •ITIL Central
- •ISACA and COBIT
- •eSCM
- •CMMI
- •eTOM
- •TechTarget
- •Vendor Sites
- •Glossary
- •Index
104 Part III: Service Management Technical Foundation
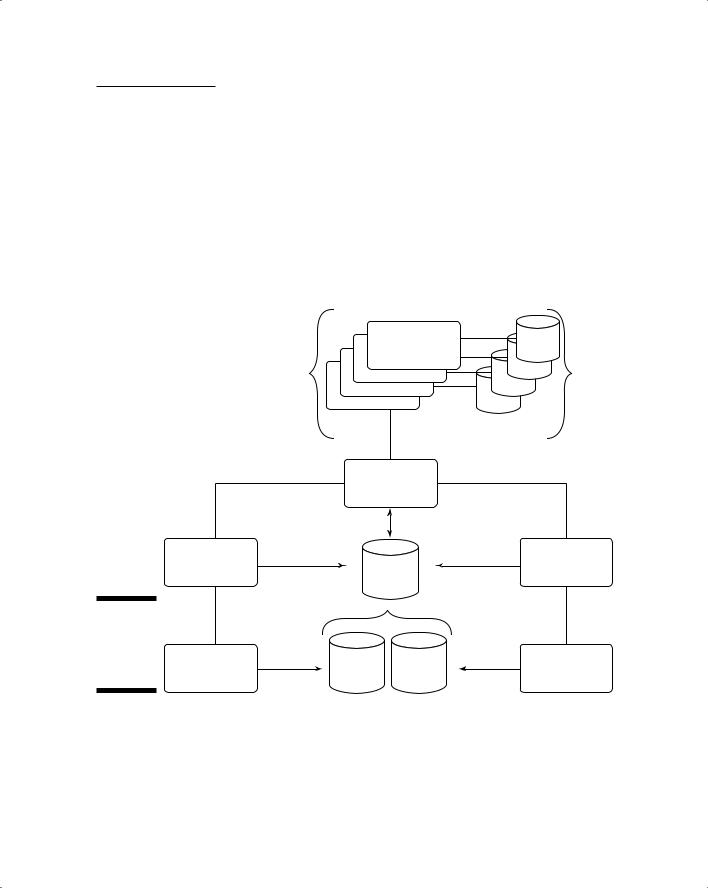
Figure 9-6: |
|
|
|
Config- |
|
|
|
uration |
Configuration |
|
CMDB |
manage- |
Management |
|
|
ment and |
|
|
|
|
|
|
|
the CMDB. |
|
|
|
|
|
|
|
|
|
|
|
The complexity of configurations became a little more complicated with the advent of enterprise application integration (EAI) technologies, which made it possible for applications to interact directly in ways that wouldn’t necessarily be visible in workload. Then the situation deteriorated even further with the advent of service oriented architecture (SOA). In an SOA, details of services (which means application capabilities) are held in the SOA registry. Consequently, SOA dependency mapping also involves accessing that registry to determine some of the dependencies among applications.
For more information on SOA, see Chapter 6. Alternatively, if you’re a real glutton for punishment, check out Service Oriented Architecture For Dummies,
2nd Edition (Wiley Publishing, Inc.), which we also wrote.
Federating the CMDB
You may notice that we present an incomplete picture in the preceding sections. We don’t explain how every single bit of the information that defines all the users, software, data, and hardware in a computing environment is assembled in a CMDB. All we do is identify the primary sources of important information that needs to reside in the CMDB. We do explain that the data the CMDB is supposed to contain is really distributed across multiple management databases that are used by a wide variety of service management applications. For that reason, we can really think only in terms of a federated CMDB.
In particular, we say very little about defining the inventory of data files that are held within any network. The truth is that the identity of data resources is in its infancy. Some applications, such as document management, define some data items very rigorously, and some important compliance rules involve certain kinds of data. But no service management application specifically gathers a comprehensive set of information about all data files.
Chapter 9: The Technical Foundation of Service Management 105
The processes involved in populating and maintaining the CMDB are illustrated again in Figure 9-7. Aside from their other functions, the goal of these activities is to make a comprehensive, accurate set of data available to all current service management applications (including any that may be created in the future) and to staff members. With the current state of technology, this process isn’t well automated, so you can expect to see significant improvements in this capability as time passes.
Having said that, it may help if we now take a brief look at how the CMDB fits into the strategic evolution of the data center and service management maturity as a whole.
ALL OTHER |
Service Mgt |
DB |
SERVICE |
Capability |
OTHER |
|
DATA |
|
MANAGEMENT |
|
|
|
STORES |
|
APPLICATIONS |
|
|
|
|
|
|
Integration |
|
|
|
|
Infrastructure |
|
|
|
Configuration |
|
|
Asset |
|
Management |
CMDB |
Management |
|
Figure 9-7: |
|
|
|
|
Federation |
|
|
|
|
and the |
|
Identity |
Asset |
|
CMDB |
Identity |
Asset |
||
system. |
Mgt |
Mgt Data |
Mgt Data |
Discovery |

106 Part III: Service Management Technical Foundation
Strategy
The general strategic direction of service management, as we discuss in Chapter 6, is evolution from systems management to business service management. Most organizations today still focus on systems management, although many enlightened organizations are beginning to align the goals of the business with both service management (to manage application services) and business service management to focus on management’s needs.
An effective CMDB is necessary for business service management to be possible at all, because it requires comprehensive, up-to-date information about what is deployed.
Strategically, the CMDB is important because it’s the platform for all other service management applications. Therefore, improving this capability is a priority. Unfortunately, very few approaches to establishing and managing a CMDB have proved to be effective and have paid for their investment. The
value of identity management, for example, lies in the improvements it makes in provisioning and IT security. The value of asset management is in the lifecycle management of those assets. The value of configuration management is mostly in change management and in problem resolution. The fact that they can all improve the coherence of the data available to the CMDB is a welcome side effect.
Maturity
In Figure 6-2, in Chapter 6, we define the maturity of service automation in terms of this progression:
Fragmented services Standardized services Integrated services
Optimized services
As we state earlier in this chapter, an integrated CMDB isn’t technically achievable right now, so in terms of maturity, the primary and practical goal is likely to be a move toward standardized services.
We think that the first step is implementing those service management applications — asset discovery, asset management, identity management, and dependency mapping — that haven’t been put in place or aren’t comprehensively implemented. IT also has to develop an effective integration infrastructure to support bringing these pieces together. Such an infrastructure may involve communications products such as enterprise service buses
Chapter 9: The Technical Foundation of Service Management 107
(ESBs) and messaging products, as well as a protocol to enable interaction among disparate service management processes. We’re not aware of any commercial products that do it all.
Key performance indicators
With the CMDB, what matters most is to assemble data that can be shared among all service management processes. No specific key performance indicators can be applied simply to measure the level of data integration. Indeed, integration itself is difficult to measure in almost any context. It is more productive simply to note the level of disruption that the lack of integration imposes on service management and to work toward reducing such disruption.

108 Part III: Service Management Technical Foundation
Chapter 10
Governing the Service Universe
In This Chapter
Considering IT governance in context
Striking a balance with business requirements
Measuring performance
Governing with best practices
You can’t implement effective service management unless IT takes a holistic approach to automation, oversight, and comprehensive asset
management across the organization. How can you do this? We recommend establishing a strong IT governance program that can provide the framework to make this happen.
IT governance in service management requires carefully combining rules for IT and business processes. You need governance rules for everything from IT security to general policies about service levels. In essence, think of a life cycle of business processes that focuses on the goal of improving
service quality and business agility. Governance from a service management perspective requires that your organization apply sound business and technical judgment. You have to make trade-offs. At times, you need to allow one service to degrade in favor of a more-business-critical service.
This chapter describes the importance of monitoring and measuring service performance, and discusses why IT governance requires companies to take a composite view of all the components of service management.
Understanding the Roles
of IT Governance
IT manages a complex infrastructure of hardware, data, storage, and software environments. The data center (some of the largest organizations have many

110 Part III: Service Management Technical Foundation
data centers) is designed to use all assets efficiently while guaranteeing a certain level of service to the customer or end user. A data center has teams of people responsible for managing everything from the overall facility, workloads, hardware, data, software, and network infrastructure.
To understand some of the complexities of service management from a data center perspective, we recommend reading Chapter 11.
In addition to the data center itself, your organization may have remote facilities with technology that depends on the data center. IT management has long-established processes for managing and monitoring individual IT components, which is good. What’s been a problem for many organizations is finding a way to monitor performance across all components in a way that reflects the overall impact of IT performance on the business.
Helping the organization meet its goals
You should direct IT governance at individual IT infrastructure components within the context of the larger challenges and goals, as well as within the company’s overall performance objectives.
IT governance is intended to help you meet the company’s overall performance indicators.
IT governance is supported in two ways:
Understanding the compliance and risk measures the business must follow: What does your business require to meet IT, corporate, industry, and government requirements? IT can support these requirements through technical controls; automation; and strict governance of processes, data, and workflows.
Understanding the performance goals of the business: You may measure your business performance in terms of sales revenue, profitability, stock price, quality of product or service provided, and time to delivery. Your IT performance measurements should focus on delivering IT services consistently and accurately so that the company gets to optimize its business performance.
Providing a view from the top
What’s one of the key benefits of taking a holistic approach to IT governance? When you have a comprehensive view, you can manage and deliver IT services
Chapter 10: Governing the Service Universe 111
more proactively. Imagine a chief information officer (CIO) who is frustrated by urgent calls from the company’s retail stores when terminals are slow or credit machines are unresponsive. The urgent calls always seem to come at the worst times, such as in the middle of a sale. Installing a remote service management system, however, would allow the CIO to do the following:
Monitor the performance of all IT services in the retail environment
Understand the relationships among those services
Notice service degradations so that problems could be fixed before stores had to make emergency calls
In this example, the remote monitoring system enables IT to create a more balanced approach to delivering services based on business objectives and regulatory requirements. The CIO can develop a better understanding of the priorities involved when he makes decisions about service management issues for the retail stores. Many companies have started using an overall business service management strategy as a technique for managing services from a unified business perspective.
We give you a lot more detail on business service management in Chapter 17.
Improving efficiency
Each industry has a set of governance principles based on its regulatory and competitive environment. The most important governance requirement in retail, for example, is for the sales process to be both efficient and accurate. What can happen in retail that becomes an IT governance challenge?
Consider another example: Store operations management would like the data center to promise 100 percent uptime supported by fully redundant servers to protect against any service slowdown, but the CIO has cost restraints.
The CIO compromises with the business. Business management and IT management agree that customers shouldn’t wait more than three minutes to complete a transaction and that the sales kiosks must be up 96 percent of the time. In addition, they agree that all customer data must be fully encrypted and protected against unauthorized access by anyone at any time.
If the CIO later discovers that performance slows so dramatically that customers leave stores without buying anything, IT governance has failed. If consistently slow credit machines cause sales clerks to make credit card sales without using the automatic credit check, the business is put at risk, and
IT governance has failed. On the other hand, if performance is excellent but customer data isn’t protected — you got it — IT governance failed again.
