
20411B-ENU-TrainerHandbook
.pdf
Administering Windows Server® 2012 |
MCT |
|
4-21 |
|
|
•Complexity enabled: Yes
•Account Lockout duration: 30 minutes
•Account lockout threshold: 5 attempts
•Reset account lockout counter after: 15 minutes
|
|
|
USE |
|
The report has also recommended that a separate policy be applied to users in the Managers group, due |
||||
to the elevated privileges assigned to those user accounts. The policy applied to the Managers groups |
|
|||
should contain the following settings: |
.ONLY |
|||
• |
Password history: 20 passwords |
|||
|
||||
• |
Maximum password age: 20 days |
|
||
• |
Minimum password age: 1 day |
|
||
• |
Password length: 15 characters |
|
||
• |
Complexity enabled: Yes |
|
||
• |
Account Lockout duration: 0 minutes (An administrator will have to unlock the account) |
STUDENT |
||
• |
Account lockout threshold: 3 attempts |
|||
|
||||
• |
Reset account lockout counter after: 30 minutes |
|
||
The main tasks for this exercise are as follows: |
|
|||
1. |
Configure a domain-based password policy. |
|
||
2. |
Configure an account-lockout policy. |
|
||
3. |
Configure and apply a fine-grained password policy. |
|
||
Task 1: Configure a domain-based password policy |
|
|||
1. |
On LON-DC1, open the Group Policy Management console. |
|
||
2. |
Edit the Default Domain Policy, and configure the following Account Password Policy settings: |
USE |
||
|
o Password history: 20 passwords |
|||
|
o Maximum password age: 45 days |
|||
|
o |
Minimum password age: 1 day |
||
|
o Password length: 10 characters |
PROHIBITED |
||
|
o |
Complexity enabled: Yes |
||
|
|
|||
1. |
In the Group Policy Management Editor, configure the following Account Lockout Policy settings for |
|||
|
the Default Domain Policy: |
|
||
|
o Account Lockout duration: 30 minutes |
|
||
|
o Account lockout threshold: 5 attempts |
|
||
|
o Reset account lockout counter after: 15 minutes |
|
||
2. |
Close Group Policy Management Editor. |
|
||
3. |
Close Group Policy Management. |
|
||

4-22 Managing User and Service Accounts
Task 3: Configure and apply a fine-grained password policy
1.On LON-DC1, open the Active Directory Administrative Center console.
2.Change the group scope for the Managers group to Global.
 Note: Ensure you open the Properties page for the Managers group, and not the Managers OU.
Note: Ensure you open the Properties page for the Managers group, and not the Managers OU.
3.In Active Directory Administrative Center, configure a fine-grained password policy for the Adatum\Managers group with the following settings:
o Name: ManagersPSO o Precedence: 10
o Password length: 15 characters o Password history: 20 passwords o Complexity enabled: Yes
o Minimum password age: 1 day
o Maximum password age: 30 days
o Number of failed logon attempts allowed: 3 attempts o Reset failed logon attempts count after: 30 minutes
o Until an administrator manually unlocks the account: selected
4.Close Active Directory Administrative Center.
Results: After completing this exercise, you will have configured password-policy and account-lockout settings.
Exercise 2: Creating and Associating a Managed Service Account
Scenario
You need to configure a managed service account to support a new Web-based application that is being deployed to the DefaultAppPool Web service on LON-DC1. Using a managed service account will help maintain the password security requirements for the account.
The main tasks for this exercise are as follows:
1.Create and associate a Managed Service Account.
2.Install a managed service account on a LON-DC1.
3.To prepare for the next module.
Task 1: Create and associate a Managed Service Account
1.On LON-DC1, open the Active Directory Module for Windows PowerShell console.
2.Create the KDS root key by using the Add-KdsRootKey cmdlet. Make the effective time minus 10 hours, so the key will be effective immediately.
3.Create the new service account named Webservice for the host LON-DC1.
PROHIBITED USE STUDENT .ONLY USE MCT

4.Associate the Webservice managed account with LON-DC1. MCT
5.Verify the group managed service account was created by using the Get-ADServiceAccount cmdlet.
Task 2: Install a managed service account on a LON-DC1
1. |
On LON-DC1, install the Webservice service account. |
USE |
|
2. |
From the Tools menu in Server Manager, open Internet Information Services (IIS) Manager. |
||
|
|||
3. |
Configure the DefaultAppPool to use the Webservice$ account as the identity. |
|
|
4. |
Stop and start the application pool. |
|
To prepare for the next module
•When you are finished the lab, revert the virtual machines to their initial state.
Results: After completing this exercise, you will have created and associated a Managed Service Account.ONLY .STUDENT
PROHIBITED USE
4-24 Managing User and Service Accounts
Module Review and Takeaways
Common Issues and Troubleshooting Tips
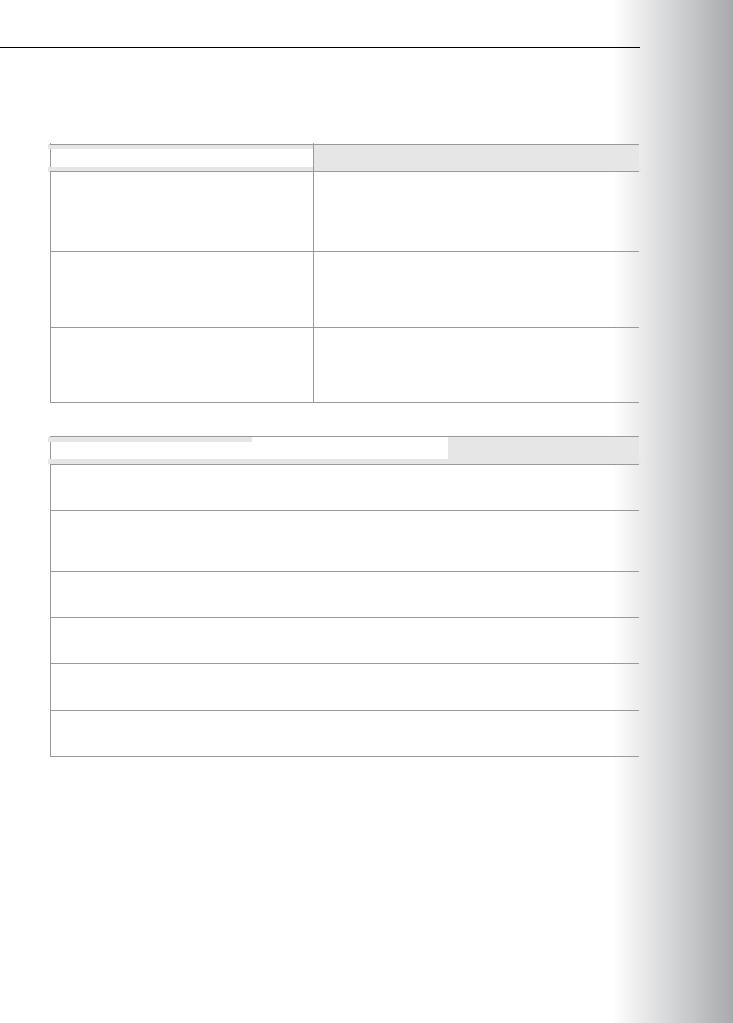
Common Issue |
Troubleshooting Tip |
|
|
User accounts contained in a .csv file fail to import when using the Comma-Separated Values Data Exchange tool.
User password settings are not applying as expected.
The New-ADServiceAccount cmdlet fails with key-related messages.
Tools
|
|
|
|
Tool |
What it is used for |
Where to find it |
|
|
|
|
|
Comma-Separated Values Data |
Importing and exporting users |
Command prompt: csvde.exe |
|
Exchange tool |
by using .csv files |
|
|
LDIFDE |
Importing, exporting, and |
Command prompt: ldifde.exe |
|
|
modifying users by using .ldf |
|
|
|
files |
|
|
Local Security Policy |
Configuring local account- |
Secpol.msc |
|
|
policy settings |
|
|
Group Policy Management |
Configuring domain Group |
Server Manager – Tools |
|
console |
Policy account-policy settings |
|
|
Active Directory Administrative |
Creating and managing |
Server Manager – Tools |
|
Center |
Password Settings Objects |
|
|
Active Directory module for |
Creating and Managing |
Server Manager - Tools |
|
Windows PowerShell |
Managed Service Accounts |
|
|
|
|
|
 PROHIBITED USE STUDENT .ONLY USE MCT
PROHIBITED USE STUDENT .ONLY USE MCT

Module 5
Implementing a Group Policy Infrastructure
Contents:
Module Overview |
5-1 |
Lesson 1: Introducing Group Policy |
5-2 |
Lesson 2: Implementing and Administering GPOs |
5-10 |
Lesson 3: Group Policy Scope and Group Policy Processing |
5-16 |
Lesson 4: Troubleshooting the Application of GPOs |
5-31 |
Lab: Implementing a Group Policy Infrastructure |
5-38 |
Module Review and Takeaways |
5-44 |
Module Overview
Group Policy provides an infrastructure within which you can define settings centrally and deploy them to users and computers in your enterprise. In an environment managed by a well-implemented Group Policy infrastructure, very little configuration takes place by an administrator directly touching a user’s computer. You can define, enforce, and update the entire configuration by using the settings in Group Policy Objects (GPOs) or GPO filtering. By using GPO settings, you can affect an entire site or domain within an enterprise, or narrow your focus to a single organizational unit (OU). This module will detail what Group Policy is, how it works, and how best to implement it in your organization.
Objectives
After completing this module, you will be able to:
•Describe the components and technologies that comprise the Group Policy framework.
•Configure and understand a variety of policy setting types.
•Scope GPOs by using links, security groups, Windows® Management Instrumentation (WMI) filters, loopback processing, and preference targeting.
•Describe how GPOs are processed.
•Locate the event logs that contain Group Policy-related events and troubleshoot the Group Policy application.
5MCT-1 USEONLY
STUDENT . PROHIBITED USE
5-2 Implementing a Group Policy Infrastructure
Lesson 1
Introducing Group Policy
A Group Policy infrastructure has several interacting components, and you need to understand what each component does, as well as how they work together and how you can assemble them into different configurations. This lesson provides a comprehensive overview of Group Policy components, procedures, and functions.
Lesson Objectives
After completing this lesson, you will be able to:
•Identify the business requirements for configuration management.
•Describe the core components and terminology of Group Policy.
•Explain the benefits of implementing GPOs.
•Describe GPOs.
•Explain the function and behavior of the client-side GPO components.
•Explain GPO refresh.
•Create and configure GPOs.
What Is Configuration Management?
If you have only one computer in your environment—at home, for example—and you need to modify the desktop background, you can achieve that in several different ways. Most people would probably open Appearance and Personalization from Control Panel, and make the change by using the Windows interface. While that works well for one computer, it may be tedious if you want to make the change across multiple computers. Implementing any change
and maintaining a consistent environment is more difficult with multiple computers.
Configuration management is a centralized approach to applying one or more changes to one or more users or computers. The key elements of configuration management are:
•Setting. A setting is also known as a centralized definition of a change. The setting brings a user or a computer to a desired state of configuration.
•Scope. The scope of the change is the ability to change users’ computers.
•Application. The application is a mechanism or process that ensures that the setting is applied to users and computers within the scope.
Group Policy is a framework within Windows—with components that reside in Active Directory® Domain Services (AD DS), on domain controllers, and on each Windows server and client—that enables you to manage configuration in an AD DS domain.
PROHIBITED USE STUDENT .ONLY USE MCT

5MCT-3 USEONLY
policy setting, a change is made to the configuration of users and computers to which the GPO is applied. When you return a setting to its Not Configured value, you return it to its default value.
In a new GPO, every policy setting defaults to Not Configured. This means that the GPO cannot modify.STUDENT the existing configuration of that particular setting for a user or computer. If you enable or disable a
PROHIBITED USE
5-4 Implementing a Group Policy Infrastructure
Benefits of Using Group Policy
Group Policies are very powerful administrative tools. You can use them to push various settings to a large number of users and computers.
Because you can apply them to various levels from local to domain, you also can focus these settings very precisely.
Primarily, you can use Group Policies to configure settings that you do not want users to configure. Additionally, you can use Group Policies to standardize desktop environments on
all computers in an OU or in an entire enterprise, to provide additional security and some advanced
system settings, and for other purposes that the following sections detail.
Apply Security Settings
In the Windows Server® 2012 operating system, GPOs include a large number of security-related settings that you can apply to both users and computers. For example, you can enforce settings for Windows Firewall, and configure auditing and other security settings. You also can configure full sets of user-rights assignments.
Manage Desktop and Application Settings
You can use a Group Policy to provide a consistent desktop and application environment to all users in your organization. By using GPOs, you can configure each setting that affects the look and feel of user environment and also configure settings for some applications that support GPOs.
Deploy Software
Group Policies enable you to deploy software to users and computers. You can use Group Policy to deploy all software that is in the .msi format. Additionally, you can enforce automatic software installation or you can let your users decide whether they want the software to deploy to their machines.
 Note: Deploying large packages with GPOs may not be the most efficient way of distributing an application to your organization’s computers. In many circumstances, it may be more effective to distribute the applications as part of the desktop computer image.
Note: Deploying large packages with GPOs may not be the most efficient way of distributing an application to your organization’s computers. In many circumstances, it may be more effective to distribute the applications as part of the desktop computer image.
Manage Folder Redirection
With folder redirection, you can manage and back up data quickly and easily. By redirecting folders, you also ensure that users have access to their data regardless of the computer on which they sign in. Additionally, you can centralize all users’ data to one place on the network server, while still providing a
user experience that is similar to storing these folders on their computers. For example, you can configure folder redirection to redirect the users’ Documents folders to a shared folder on a network server.
Configure Network Settings
Using Group Policy enables you to configure various network settings on client computers. For example, you can enforce settings for wireless networks to allow users to connect only to specific service set identifiers (SSIDs), and with predefined authentication and encryption settings. You also can deploy policies that apply to wired network settings as well as configure the client side of services, such as Network Access Protection (NAP).
PROHIBITED USE STUDENT .ONLY USE MCT
5MCT-5 USEONLY
see that the Group Policy Management Editor displays folders, which also are called nodes or policy setting groups. Within the folders are the policy settings themselves.
The next two levels of the hierarchy are nodes called Policies and Preferences. You will learn about the.STUDENT difference between these two nodes later in this module. Progressing further down the hierarchy, you can
PROHIBITED USE
5-6 Implementing a Group Policy Infrastructure
cannot change the setting on their computer—they will always be subject to the configuration enforced by Group Policy. However, standard users can change some settings, and many can be changed if a user is an administrator on that system. If users in your environment are administrators on their computers, you
|
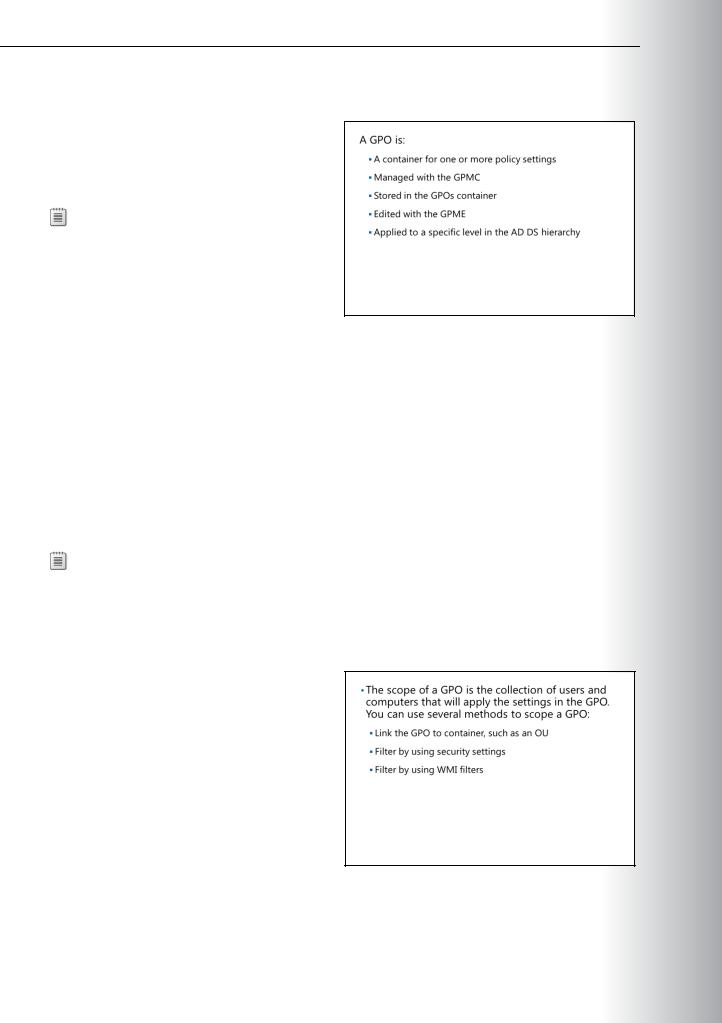
Note: You can link a GPO to more than one domain, OU, or site. Linking GPOs to multiple |
MCT |
||
sites can introduce performance issues when the policy is being applied, and you should avoid |
||||
linking a GPO to multiple sites. This is because in a multisite network, the GPOs are stored in the |
||||
USE |
||||
domain controllers of the forest root domain. The consequence of this is that computers in other |
||||
domains may need to traverse a slow wide area network (WAN) link to obtain the GPOs. |
||||
You can further narrow the scope of the GPO with one of two types of filters. Security filters specify |
||||
security groups that fall within the GPO’s scope, but to which the GPO explicitly should or should not |
||||
|
||||
apply. WMI filters specify a scope by using characteristics of a system, such as operating-system version or |
||||
free disk space. Use security filters and WMI filters to narrow or specify the scope within the initial scope |
.ONLY |
|||
that the GPO link created. |
||||
|
Note: Windows Server 2008 introduced a new component of Group Policy: Group Policy |
|||
|
||||
Preferences. Settings that are configured by Group Policy Preferences within a GPO can be |
||||
filtered or targeted based on several criteria. Targeted preferences allow you to further refine the |
||||
scope of preferences within a single GPO. |
||||
STUDENT |
||||
Group Policy Client and Client-Side Extensions |
||||
|
|
|||
Group Policy Application |
|
|||
It is important to understand how Group Policies |
|
|||
apply on client computers. The outline below |
|
|||
details the process: |
|
|||
1. When Group Policy refresh begins, a |
|
|||
|
|
|||
|
service that is running on all Windows-based |
|
|
|
|
computers, known as the Group Policy Client |
|
|
|
|
in Windows Vista®, Windows 7, Windows 8, |
|
|
|
|
Windows Server 2008, Windows Server 2008 |
|
|
|
|
R2, and Windows Server 2012, determines |
|
|
|
|
which GPOs apply to the computer or user. |
USE |
||
2. This service downloads any GPOs that are not cached already. |
||||
|
||||
3. Client-side extensions (CSEs) interpret the settings in a GPO and make appropriate changes to the |
|
|||
|
local computer or to the currently logged-on user. There are CSEs for each major category of policy |
|
||
|
setting. For example, there is a security CSE that applies security changes, a CSE that executes startup |
|
||
|
and logon scripts, a CSE that installs software, and a CSE that makes changes to registry keys and |
|
||
|
values. Each Windows version has added CSEs to extend the functional reach of Group Policy, and |
|
||
|
there are several dozen CSEs in Windows. |
PROHIBITED |
||
One of the more important concepts to remember about Group Policy is that it is very client-driven. The |
||||
Group Policy client pulls the GPOs from the domain, triggering the CSEs to apply settings locally. Group |
||||
Policy is not a push technology. |
||||
In fact, you can configure the behavior of CSEs by using Group Policy. Most CSEs will apply settings in |
||||
a GPO only if that GPO has changed. This behavior improves overall policy processing by eliminating |
||||
redundant applications of the same settings. Most policies are applied in such a way that standard users |
||||
|
|
|
||
